Get the free USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT - usg
Show details
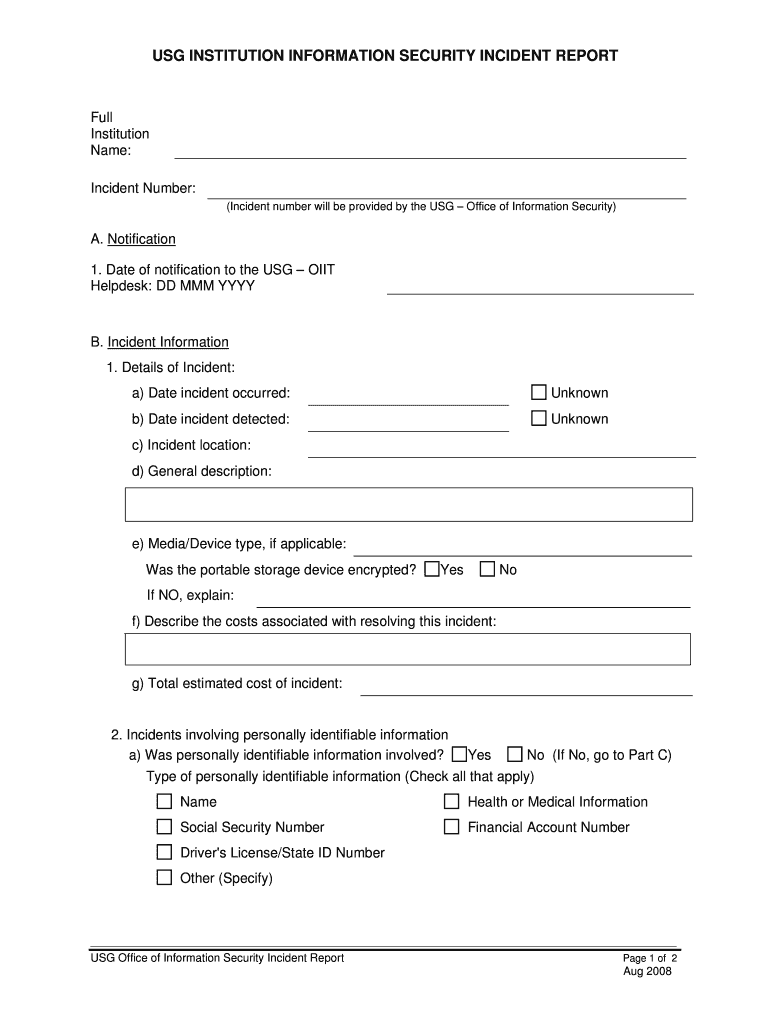
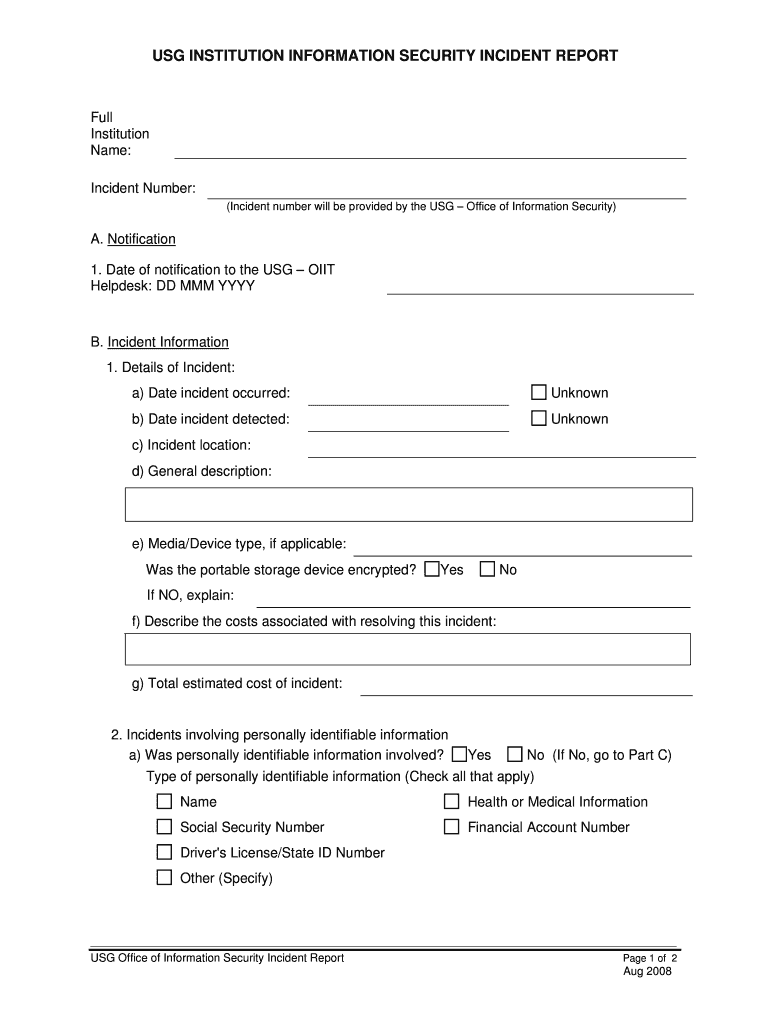
This document serves as a formal report to document security incidents occurring in USG institutions, detailing the nature of the incident, notification process, and corrective actions taken.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign usg institution information security

Edit your usg institution information security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your usg institution information security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing usg institution information security online
To use our professional PDF editor, follow these steps:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit usg institution information security. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out usg institution information security

How to fill out USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT
01
Begin by entering the date and time of the incident in the appropriate fields.
02
Identify the institution where the incident occurred and provide the relevant contact information.
03
Describe the nature of the security incident, providing details about what happened.
04
Outline the specific systems or data affected by the incident.
05
Indicate who discovered the incident and how it was brought to attention.
06
Include any preliminary actions that were taken to mitigate the incident.
07
Specify the individuals who are involved in responding to the incident.
08
Add any additional comments or relevant information that may assist in understanding the incident.
09
Review the completed report for accuracy and completeness.
10
Submit the report to the designated authority within your institution.
Who needs USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT?
01
USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT is needed by security personnel, IT staff, compliance officers, and incident response teams within educational institutions.
02
It may also be required by regulatory bodies or external auditors who review information security practices and incidents.
Fill
form
: Try Risk Free






People Also Ask about
How to write a report for a security incident?
A good cybersecurity incident report template should include: Name or names of all witnesses Date and time at which the incident occurred/was detected Specific services affected by the incident A large space in which a detailed account can be written Multiple signature lines Detail of any action taken (if any)
How can you report a security incident?
Report to the Cybersecurity and Infrastructure Security Agency (CISA) (CISA) CISA provides secure means for constituents and partners to report incidents, phishing attempts, malware, and vulnerabilities.
How should an information security incident be reported?
Information to include in the report: Your name. Department. Email address. Telephone number. Description of the information security problem. Date and time the problem was first noticed (if possible) Any other known resources affected.
What are examples of information security incidents?
The different types of cybersecurity incidents include: Ransomware / Malware. Password Attacks. Credential Stuffing. Business Email Compromise.
How to write an incident report example?
A general staff incident report generally includes: Person's name and contact details. Incident Time, date, and site. Pertinent details about what happened. Kind of injury or damage. Name of witnesses. Safety measures taken Suggestions for prevention.
How to write an information security report?
Key steps to writing a security incident report Capture incident details. A well-written incident description is the core of your report. Identify involved parties. Describe the sequence of events. Document the response. Record evidence and supporting information. Assess impact and damages. Recommend follow-up actions.
What are the 3 C's of report writing in security?
There are certain qualities that all effective reports should have. A good way to remember the qualities of a well-written report is the "Three (3) C's of report writing." The 3 C's of report writing are a guideline to the characteristics of a good report. Reports are to be clear, concise, and complete.
How do I write a security incident report example?
Step-by-step guide to writing an incident report Start with basic information. Do what you can to set the scene as accurately as possible. Describe the incident. Offer a detailed account of what happened. Identify people involved. Detail the actions taken. Include follow-up actions.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT?
The USG Institution Information Security Incident Report is a formal document used to report and document security incidents affecting information systems and data within USG institutions. It helps in identifying, analyzing, and managing security breaches.
Who is required to file USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT?
Any employee, contractor, or third-party individual who encounters, witnesses, or becomes aware of a security incident involving sensitive or protected information within USG institutions is required to file the report.
How to fill out USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT?
To fill out the report, provide detailed information about the incident, including date and time of occurrence, description of the incident, systems affected, and any immediate action taken. Ensure that all sections of the report are completed and accurate.
What is the purpose of USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT?
The purpose of the USG Institution Information Security Incident Report is to ensure a systematic approach to identifying and managing security incidents, maintain compliance with regulations, improve future response and prevention strategies, and promote awareness of information security.
What information must be reported on USG INSTITUTION INFORMATION SECURITY INCIDENT REPORT?
The report must include information such as the nature and type of incident, identification of individuals and systems involved, detailed timeline of events, impact assessment, and any containment or remediation actions taken.
Fill out your usg institution information security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Usg Institution Information Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.