Last updated on Apr 6, 2026

Get the free Security Access Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is security access form
The Security Access Form is a business document used by employees and consultants of the Nevada System of Higher Education (NSHE) to request access to sensitive data.
pdfFiller scores top ratings on review platforms




Who needs security access form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to security access form
What is the Security Access Form?
The Security Access Form is a crucial document utilized by employees and consultants within the Nevada System of Higher Education (NSHE) to request access to sensitive data. This form not only facilitates the data access process but also plays a significant role in ensuring security protocols are followed diligently. Utilizing this form ensures that those who need access to specific data have undergone necessary compliance checks regarding data access and security.
By completing this form, users express their need for data access while adhering to the required security practices mandated by NSHE.
Purpose and Benefits of the Security Access Form
The purpose of the Security Access Form is to serve as a formal request for access to sensitive data within the NSHE framework. It is essential for complying with various regulations, including FERPA and the Campus Computing Agreement. These compliance requirements ensure that individuals accessing data are qualified and hold the appropriate approvals necessary for security and privacy.
Securing the necessary approvals through this form strengthens the protocols around data protection, ultimately safeguarding both the individual's and institution's sensitive information.
Key Features of the Security Access Form
The Security Access Form contains several key components that facilitate the application process. It includes:
-
Multiple fillable fields for personal and job-related information.
-
Checkboxes to confirm understanding and acceptance of data security policies.
-
Signature requirements from both a supervisor and the project lead to validate the request.
These features reinforce security protocols within NSHE, ensuring that only authorized personnel gain access to sensitive information.
Who Needs the Security Access Form?
The target audience for the Security Access Form includes employees and consultants who require access to sensitive data. Different roles in this process involve:
-
Applicants who fill out and submit the form.
-
Supervisors who provide necessary approvals.
-
Project leads who also need to sign the form for verification.
Understanding job-related information is vital for all involved, as accurate completion of the form is crucial for proper approvals and access.
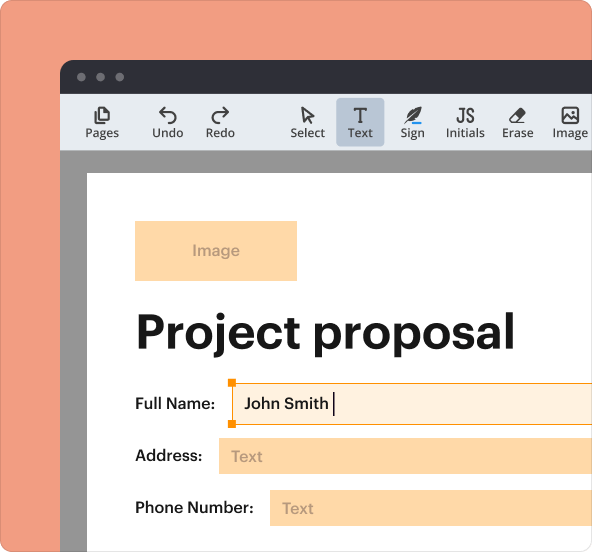
How to Fill Out the Security Access Form Online
To successfully complete the Security Access Form using pdfFiller, follow these steps:
-
Open the form using pdfFiller.
-
Carefully fill in all required fields, ensuring your personal information is accurate.
-
Justify your data access request clearly to avoid complications.
-
Obtain the required signatures from your supervisor and project lead.
Pay special attention to fields that require detailed justification, and be mindful of common errors such as missing information or incorrect signatures.
Submission Methods for the Security Access Form
Once the Security Access Form is complete, multiple submission methods are available:
-
Online submission through the designated NSHE platform.
-
Email submission to the specified department address.
-
In-person delivery at the appropriate NSHE office.
It is important to be aware of any state-specific rules or fees associated with the submission process, as well as the expected processing time for requests.
Security and Compliance for the Security Access Form
Security measures surrounding the Security Access Form are stringent. Data protection practices include:
-
Encryption of all submitted data to maintain confidentiality.
-
Compliance with FERPA and other relevant legal frameworks.
-
Adherence to record retention requirements post-submission.
Understanding these security protocols is essential for ensuring compliance and protecting sensitive information throughout the form's use.
Tracking and Confirmation After Submitting the Security Access Form
After submitting the Security Access Form, users can anticipate receiving confirmation of their submission. To confirm and track the status of their application, users should:
-
Check their email for submission confirmation notifications.
-
Contact the designated department to verify receipt and processing status.
Being proactive in verifying application status is crucial to ensure timely access to needed data.
How pdfFiller Can Help with the Security Access Form
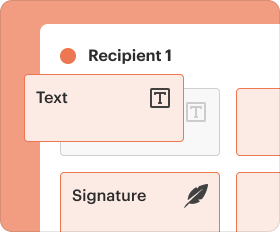
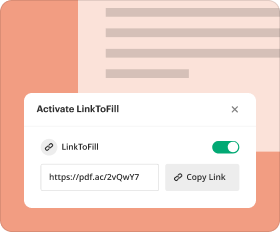
pdfFiller significantly eases the process of filling out, signing, and submitting the Security Access Form. Its capabilities include:
-
Editing and annotating the form easily to ensure accuracy.
-
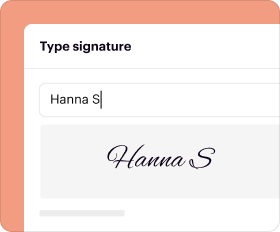
Facilitating electronic signatures for swift processing.
-
Ensuring document security throughout the filling and submission process.
Utilizing pdfFiller can enhance the user experience, making the handling of the Security Access Form more efficient and secure.
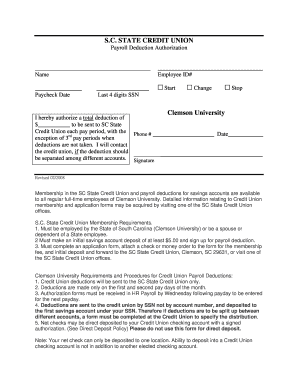
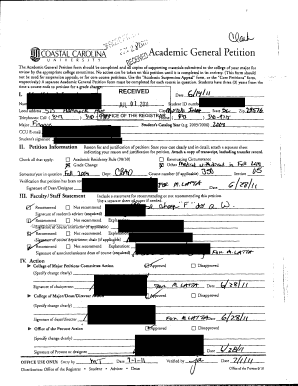
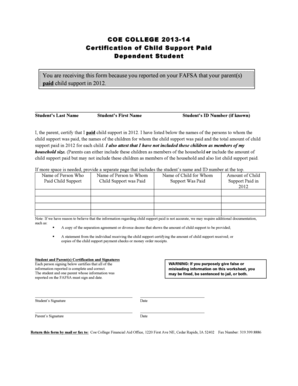
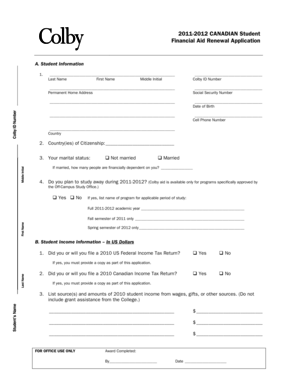
Sample Completed Security Access Form
To assist users in completing the Security Access Form correctly, a sample filled-out form is provided for reference. It is annotated to demonstrate how each field should be completed, offering practical insights into what requires attention. When reviewing the sample, individuals should:
-
Note the type of information provided in each field.
-
Follow the formatting and details as illustrated.
This reference can help reinforce correct procedures when filling out the actual form.
How to fill out the security access form
-
1.Access the Security Access Form on pdfFiller by using a provided link or searching for it directly on the site.
-
2.Once opened, navigate through the form using the intuitive interface. You can use scroll bars or mouse clicks to reach different sections.
-
3.Before starting, gather necessary personal details, job-related information, and your supervisor's and project lead's contact information for their signatures.
-
4.Complete each field carefully, filling out personal data, job role details, and agreeing to terms outlined in the Campus Computing Agreement and FERPA.
-
5.Utilize drop-down menus or checkboxes wherever applicable to save time and ensure accuracy in your responses.
-
6.After filling out the form, review every entry for typos or missing information. Make edits as needed for clarity and correctness.
-
7.Finalize your form by checking it doesn't require notarizing. Save your progress frequently to avoid losing data.
-
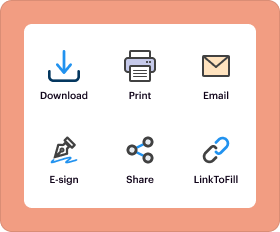
8.Once you're satisfied with the completed form, download it or submit it directly through pdfFiller's submission options to send it to the relevant parties.
Who is eligible to fill out the Security Access Form?
Employees or consultants of the Nevada System of Higher Education (NSHE) who need access to sensitive data are eligible to fill out the Security Access Form.
What is the purpose of the Security Access Form?
The purpose of the Security Access Form is to formally request access to sensitive data, ensuring compliance with protocols like the Campus Computing Agreement and FERPA.
How do I submit the completed Security Access Form?
Once completed, the Security Access Form can be submitted directly through pdfFiller's submission functions or downloaded to share via email or physical delivery as required.
What documents do I need to provide with the form?
While specific supporting documents aren't mentioned, applicants typically need to provide personal and job-related information to fill out the form accurately.
How long does the approval process take?
Processing times can vary based on the institution's workload and policies. It's best to submit your form as early as possible to allow for potential delays.
What common mistakes should I avoid when filling out the form?
Common mistakes include leaving fields blank, misspelling names or information, and failing to obtain necessary signatures from supervisors and project leads.
Is notarization required for this form?
No, notarization is not required for the Security Access Form, making the submission process simpler for applicants.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.