
Get the free From Information Systems Security
Show details
From Information Systems Security820254DATA SECURITY MANAGEMENTRECORDS RETENTION AND
S SECURITY REGULATIONS
THINK ABOUT IT!
Rebecca Herold, CISP, CISA, FLMIINSIDESecurity; Regulations; Health Insurance
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign from information systems security
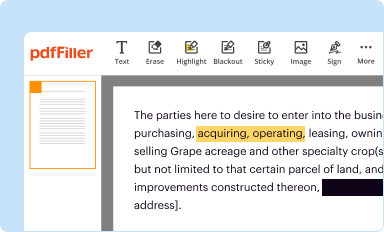
Edit your from information systems security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
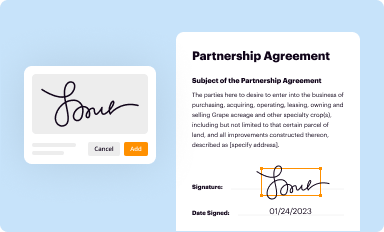
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
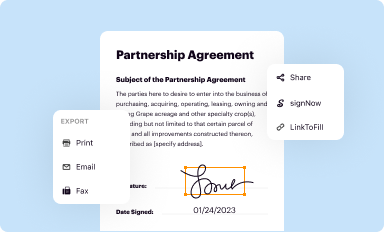
Share your form instantly
Email, fax, or share your from information systems security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
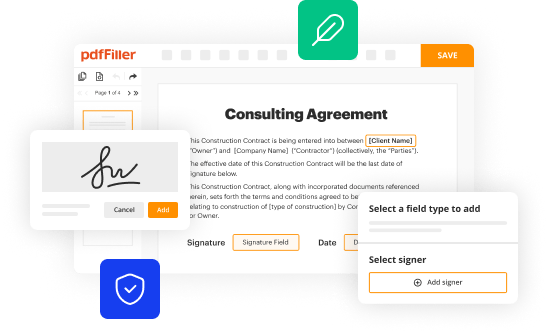
How to edit from information systems security online
Follow the steps below to benefit from the PDF editor's expertise:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit from information systems security. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out from information systems security
How to fill out from information systems security:
01
Understand the purpose: Before filling out any form related to information systems security, it is crucial to understand the purpose of the form. This will help provide the necessary information and ensure accuracy.
02
Gather required information: Take the time to collect all the relevant information that the form asks for. This may include personal details, contact information, employment history, and any certifications or qualifications related to information systems security.
03
Review the form instructions: Carefully read through the instructions provided with the form. This will help in understanding any specific requirements or guidelines for filling out the form correctly.
04
Complete the form accurately: Fill out the form accurately, ensuring that all information provided is correct and up-to-date. Double-check the form for any errors or missing information before submitting it.
05
Provide supporting documentation: If the form requires any supporting documentation, ensure that all the required documents are attached before submitting the form. This could be copies of relevant certifications, identification documents, or any other requested paperwork.
06
Submit the form: Once the form is fully completed and reviewed, submit it according to the designated method or to the appropriate authority responsible for information systems security forms.
Who needs from information systems security?
01
Organizations and businesses: Companies of all sizes, across various industries, require information systems security to protect their sensitive data, prevent cyber threats, and ensure the integrity of their systems.
02
Government agencies: Government agencies, whether at the federal, state, or local level, deal with vast amounts of sensitive information and are prime targets for cyberattacks. Information systems security is essential to safeguard classified data, systems, and operations.
03
Individuals: With the increasing prevalence of online activities and dependence on digital systems, individuals also need information systems security. This ranges from securing personal data stored on devices to protecting online identities, ensuring safe financial transactions, and safeguarding against identity theft.
In conclusion, filling out a form for information systems security requires understanding the purpose, gathering all necessary information, following the instructions, accurately completing the form, providing required documentation, and submitting it appropriately. The need for information systems security applies to organizations, government agencies, and individuals alike.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is from information systems security?
Information systems security refers to the practice of protecting computer systems and networks from unauthorized access, use, disclosure, disruption, modification, or destruction.
Who is required to file from information systems security?
Organizations that handle sensitive information or information with regulatory requirements are generally required to file information systems security reports.
How to fill out from information systems security?
Information systems security reports can be filled out electronically or manually, depending on the requirements of the organization or regulatory body.
What is the purpose of from information systems security?
The purpose of information systems security is to ensure the protection and confidentiality of sensitive information, prevent unauthorized access, and comply with regulatory requirements.
What information must be reported on from information systems security?
Information such as security incidents, security controls, risk assessments, and security policies must be reported on information systems security.
How do I modify my from information systems security in Gmail?
You may use pdfFiller's Gmail add-on to change, fill out, and eSign your from information systems security as well as other documents directly in your inbox by using the pdfFiller add-on for Gmail. pdfFiller for Gmail may be found on the Google Workspace Marketplace. Use the time you would have spent dealing with your papers and eSignatures for more vital tasks instead.
How can I fill out from information systems security on an iOS device?
Download and install the pdfFiller iOS app. Then, launch the app and log in or create an account to have access to all of the editing tools of the solution. Upload your from information systems security from your device or cloud storage to open it, or input the document URL. After filling out all of the essential areas in the document and eSigning it (if necessary), you may save it or share it with others.
How do I fill out from information systems security on an Android device?
Use the pdfFiller app for Android to finish your from information systems security. The application lets you do all the things you need to do with documents, like add, edit, and remove text, sign, annotate, and more. There is nothing else you need except your smartphone and an internet connection to do this.
Fill out your from information systems security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

From Information Systems Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.


















