Last updated on Apr 6, 2026

Get the free McKesson Security Agreement
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is mckesson security agreement
The McKesson Security Agreement is a healthcare form used by the Medical University of South Carolina to protect patient information in the electronic medical record (EMR).
pdfFiller scores top ratings on review platforms




Who needs mckesson security agreement?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to mckesson security agreement
What is the McKesson Security Agreement?
The McKesson Security Agreement serves as a crucial document for healthcare providers, primarily aimed at safeguarding patient information. Its primary purpose is to ensure that all users accessing electronic medical records (EMR) understand their responsibilities in protecting patient confidentiality. In the healthcare sector, maintaining the security of sensitive information is paramount, as breaches can undermine trust and compliance with regulations.
This agreement highlights the importance of securing patient information, making it clear that confidentiality is not just a policy but a fundamental duty of all authorized personnel. Keywords related to the agreement include "mckesson security agreement," "patient information security," and "healthcare information access."
Purpose and Benefits of the McKesson Security Agreement
The McKesson Security Agreement plays a vital role in protecting patient records by establishing guidelines that assure the confidentiality and integrity of sensitive data. One major advantage of this agreement is its contribution to compliance with healthcare regulations, which is crucial for healthcare providers operating within legal frameworks.
Furthermore, this agreement facilitates enhanced healthcare delivery by allowing secure access to information necessary for patient care. Its relevance extends to various stakeholders, including those from the Medical University of South Carolina, reinforcing the importance of patient data confidentiality.
Who Needs the McKesson Security Agreement?
This agreement is essential for medical professionals and authorized users who require access to electronic medical records. Specific roles, such as doctors, nurses, and administrative staff, must complete the McKesson Security Agreement to ensure that they comply with security protocols when accessing patient information.
Maintaining security in accessing sensitive data is critical in healthcare environments, where unauthorized access can lead to serious breaches. Keywords such as "healthcare user identification" and "emr access form" underscore the necessity of this agreement for personnel in healthcare settings.
How to Fill Out the McKesson Security Agreement Online (Step-by-Step)
Completing the McKesson Security Agreement online requires attention to detail. Users must begin by entering their unique user identification code in the designated fields. The following steps outline the process of filling out the necessary sections:
-
Provide your FULL Name.
-
Enter your Credentials (e.g., RN, MD).
-
Sign and date the form accurately.
Ensuring the accuracy of details provided is crucial, as errors can lead to delays in processing access requests. Keywords like "musc security agreement" and "electronic medical record access" are salient in this context.
Field-by-Field Instructions for the McKesson Security Agreement
Understanding the various fields within the McKesson Security Agreement is necessary for proper completion. Each fillable field carries significant meaning, as incorrect entries can cause confusion during processing.
Here are key instructions for specific fields:
-
FULL Name: Enter your complete legal name as it appears in official documents.
-
Credentials: Clearly print your professional designation (e.g., RN, MD).
-
Signature: Your signature must be accompanied by the date of signing.
Additional special notes include checkboxes for “Application Requested,” emphasizing that users must complete all fields as per instructions to avoid common pitfalls during submission.
Submission Methods and Delivery for the McKesson Security Agreement
Once completed, users can submit the McKesson Security Agreement through various methods. Electronic submission is often preferred to streamline processing, but physical delivery options are also available. Here are tips for ensuring secure transmission of sensitive information:
-
Always use secure channels for electronic submissions.
-
If submitting physically, utilize a secure method of delivery, such as registered mail.
These methods help protect the integrity of the document while ensuring compliance with healthcare user identification practices.
Security and Compliance for the McKesson Security Agreement
The McKesson Security Agreement emphasizes robust security measures to protect sensitive documents. These measures include data encryption and adherence to HIPAA compliance, which are critical in safeguarding patient data in healthcare contexts.
Understanding the importance of data protection helps reinforce trust between healthcare providers and patients, prioritizing patient data confidentiality and security compliance.
What Happens After You Submit the McKesson Security Agreement?
After submitting the McKesson Security Agreement, users can anticipate several potential next steps. Typically, the timeline for approval or feedback may vary based on the specific processes of the healthcare provider. It is advisable to follow up to validate the submission and track its status, ensuring that access to the necessary systems is granted promptly.
Keywords like "mckesson security agreement" and "healthcare information access" relate directly to the expectations following submission.
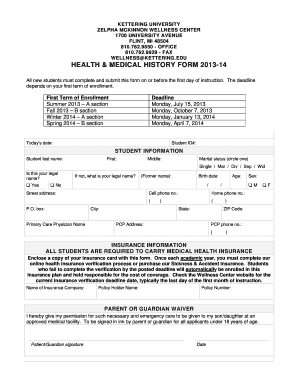
Sample McKesson Security Agreement
Reviewing a sample McKesson Security Agreement can be significantly beneficial for users. A visual example helps in comprehending the necessary components and format required for completion.
Key components highlighted in the sample include required fields and signatures, ensuring that users have guidance for a correct and compliant submission. This practice supports clarity when navigating the completion process.
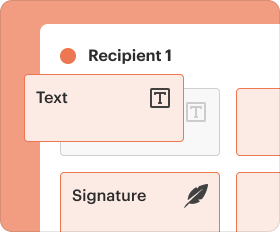
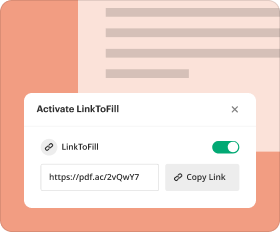
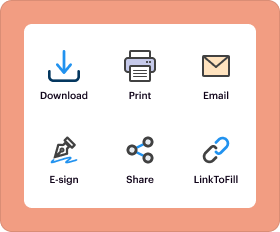
Streamline Your McKesson Security Agreement Process with pdfFiller
Utilizing pdfFiller offers numerous advantages for managing the McKesson Security Agreement. The platform simplifies document management and eSigning while ensuring compliance with security features essential for handling sensitive materials.
Users are encouraged to access pdfFiller for a seamless experience in filling out and managing healthcare forms confidently.
How to fill out the mckesson security agreement
-
1.Access the McKesson Security Agreement by visiting pdfFiller and searching for the document using the platform's search feature.
-
2.Once located, click to open the form in the pdfFiller editor where you can see fillable fields and instructions displayed.
-
3.Before filling out the form, gather necessary information such as your full name, credentials, and any identification numbers you may need.
-
4.Proceed by entering your full name in the designated space, ensuring you provide accurate spelling and formatting.
-
5.Next, fill in your credentials as instructed, using print formatting for clarity—this may include designations such as RN, MD, or PCT.
-
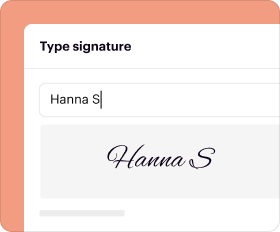
6.Follow up by digitally signing the form in the specified area and adding the date to ensure your consent is properly documented.
-
7.Ensure all fields are completed before finalizing your submission; review your information for accuracy before moving on to save or submit the form.
-
8.Once you are satisfied with the completed document, choose the save option to store it on your device, or use the download feature to save a copy for your records.
-
9.If required, submit the completed form through the designated submission method, ensuring it reaches the OCIO-IS department as instructed.
Who is eligible to sign the McKesson Security Agreement?
Healthcare professionals and employees of the Medical University of South Carolina who need access to the electronic medical record (EMR) are eligible to sign the McKesson Security Agreement.
What is the deadline for submitting the McKesson Security Agreement?
While a specific deadline isn't mentioned, it's advisable to complete and submit the McKesson Security Agreement as soon as access is needed to ensure compliance with data security standards.
How do I submit the McKesson Security Agreement once completed?
After completing the McKesson Security Agreement, it should be returned to the OCIO-IS department. Ensure you check for any specific submission methods provided by the institution.
What supporting documents are required with the McKesson Security Agreement?
No specific supporting documents are mentioned in the metadata, but it may be helpful to include any identification such as a work ID or professional credentials when submitting the form.
What common mistakes should I avoid when completing this form?
Avoid incomplete fields, incorrect signatures, and outdated information. Always check your entries against the requirements outlined in the form to prevent delays.
How long does it take to process the McKesson Security Agreement?
Processing time for the McKesson Security Agreement may vary. It generally depends on the department workload; expect a few business days for routine processing.
Can I fill out the McKesson Security Agreement on my mobile device?
Yes, pdfFiller is accessible on mobile devices, allowing users to fill out the McKesson Security Agreement conveniently.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.