Get the free Practical Implementation and Performance Analysis on Security of Sensor Networks - r...
Show details
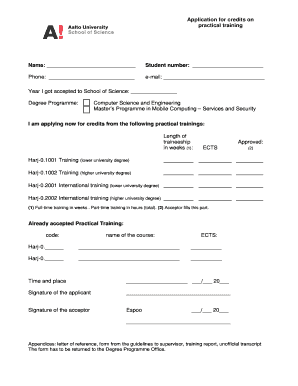
This document is a master's thesis analyzing the security of wireless sensor networks and proposing implementations using symmetric and asymmetric cryptography.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign practical implementation and performance

Edit your practical implementation and performance form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your practical implementation and performance form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing practical implementation and performance online
To use the professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit practical implementation and performance. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out practical implementation and performance

How to fill out Practical Implementation and Performance Analysis on Security of Sensor Networks
01
Identify the key objectives of the security analysis.
02
Choose the relevant sensor network architecture and components for implementation.
03
Collect data on current security protocols used in similar sensor networks.
04
Design and implement security measures such as encryption, authentication, and intrusion detection.
05
Establish performance metrics to evaluate the effectiveness of the security measures.
06
Conduct experiments to assess the performance under various conditions.
07
Analyze the collected data to determine the impact of security measures on sensor network performance.
08
Document findings comprehensively, detailing both practical implementations and performance analysis.
Who needs Practical Implementation and Performance Analysis on Security of Sensor Networks?
01
Network security professionals looking to enhance sensor network safety.
02
Businesses deploying IoT solutions that rely on sensor networks.
03
Researchers focusing on cybersecurity in distributed systems.
04
Government agencies concerned with national security involving sensor networks.
05
Academics interested in the field of cybersecurity and sensor technologies.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Practical Implementation and Performance Analysis on Security of Sensor Networks?
It refers to the process of applying security measures in sensor networks and evaluating their effectiveness in real-world scenarios, focusing on ensuring data integrity, confidentiality, and availability.
Who is required to file Practical Implementation and Performance Analysis on Security of Sensor Networks?
Researchers, practitioners, and organizations involved in deploying sensor networks must file this analysis to assess and demonstrate the security measures implemented.
How to fill out Practical Implementation and Performance Analysis on Security of Sensor Networks?
To fill it out, gather data on the deployment, security measures implemented, performance metrics, vulnerabilities identified, and mitigation strategies, then compile this information in a structured format.
What is the purpose of Practical Implementation and Performance Analysis on Security of Sensor Networks?
The purpose is to identify potential security risks, evaluate the effectiveness of existing security protocols, and provide insights for improving the overall security architecture of sensor networks.
What information must be reported on Practical Implementation and Performance Analysis on Security of Sensor Networks?
Reporting must include details on the network architecture, security mechanisms in use, performance metrics (like latency and throughput), identified vulnerabilities, and recommendations for enhancements.
Fill out your practical implementation and performance online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Practical Implementation And Performance is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
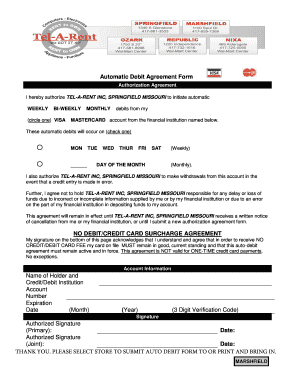
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.