Get the free REPORTING BREACHES
Show details
REPORTING BREACHES
OF DATABASES Thomas P. Brady
313.965.8291
tbrady@clarkhill.comBrian D. Shekel
313.965.8803
bshekell@clarkhill.comOBJECTIVES
When does a security breach occur? When is notice required?
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign reporting breaches
Edit your reporting breaches form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
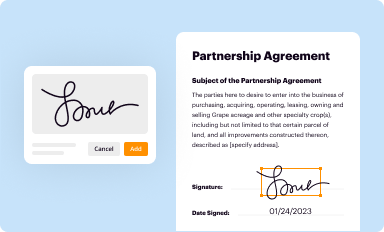
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
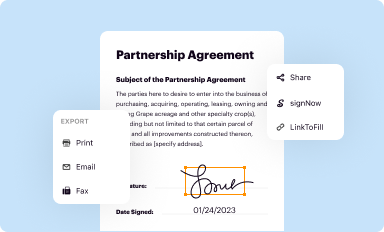
Share your form instantly
Email, fax, or share your reporting breaches form via URL. You can also download, print, or export forms to your preferred cloud storage service.
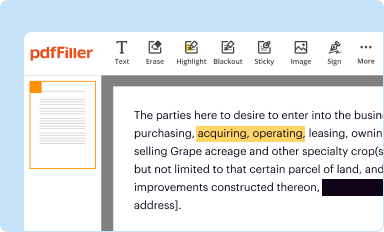
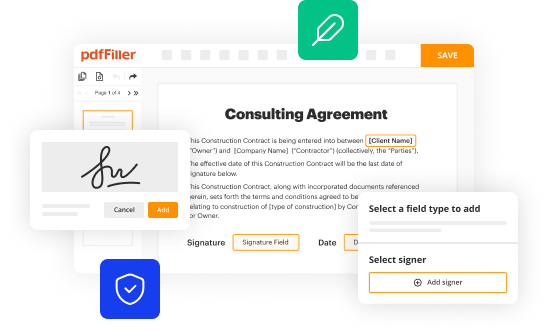
Editing reporting breaches online
Follow the steps down below to take advantage of the professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit reporting breaches. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, it's always easy to work with documents. Try it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out reporting breaches
How to fill out reporting breaches:
01
Gather all necessary information: Before filling out a report for a breach, it is important to gather all relevant information related to the incident. This may include details such as the date and time of the breach, the type of breach, any potential harm or damage caused, and any individuals or systems affected.
02
Follow reporting guidelines: Different organizations may have their own specific reporting guidelines for breaches. It is essential to familiarize yourself with these guidelines and ensure that you follow them accurately. This may involve using a specific reporting form or following a specific reporting process.
03
Provide a detailed description: When filling out the report, provide a detailed description of the breach. Include any relevant information that may aid in understanding the incident, such as the methods used by the attacker, any vulnerabilities exploited, or any preventive measures in place.
04
Include any relevant evidence: If possible, include any evidence or documentation related to the breach. This may include log files, screenshots, or any other supporting materials that can provide additional context or evidence of the incident.
05
Report to the appropriate authority: Depending on the nature of the breach, it may be necessary to report it to certain authorities or regulatory bodies. Ensure that you are aware of any legal or compliance obligations and report the breach to the appropriate authorities within the required timeframe.
Who needs reporting breaches:
01
Organizations: It is crucial for organizations to report breaches as it allows them to understand the extent of the incident, assess and mitigate any potential damage, and take necessary actions to prevent future breaches. Reporting breaches also helps organizations fulfill their legal and regulatory obligations, as well as maintain transparency with stakeholders.
02
Individuals affected by the breach: Reporting breaches is essential for individuals who have been affected by the breach. By reporting the incident, individuals can alert the relevant authorities, organizations, or institutions that hold their sensitive information, enabling them to take necessary measures to protect their data and prevent further harm.
03
Regulatory bodies and authorities: Reporting breaches to regulatory bodies and authorities is necessary to ensure compliance with applicable laws and regulations. These bodies can investigate the breach, identify any lapses in security measures, and enforce necessary actions or penalties to hold the responsible parties accountable.
04
Industry peers and stakeholders: Reporting breaches to industry peers and stakeholders promotes information sharing and collaboration. By sharing information about breaches, organizations can help others learn from their experiences, implement effective security measures, and collectively improve cybersecurity practices across industries.
In summary, reporting breaches involves gathering relevant information, following reporting guidelines, providing a detailed description, including evidence, and reporting to the appropriate authorities. Organizations, individuals affected by the breach, regulatory bodies, and industry peers all require reporting breaches for different reasons.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit reporting breaches online?
The editing procedure is simple with pdfFiller. Open your reporting breaches in the editor, which is quite user-friendly. You may use it to blackout, redact, write, and erase text, add photos, draw arrows and lines, set sticky notes and text boxes, and much more.
Can I create an eSignature for the reporting breaches in Gmail?
Upload, type, or draw a signature in Gmail with the help of pdfFiller’s add-on. pdfFiller enables you to eSign your reporting breaches and other documents right in your inbox. Register your account in order to save signed documents and your personal signatures.
How do I edit reporting breaches straight from my smartphone?
You can easily do so with pdfFiller's apps for iOS and Android devices, which can be found at the Apple Store and the Google Play Store, respectively. You can use them to fill out PDFs. We have a website where you can get the app, but you can also get it there. When you install the app, log in, and start editing reporting breaches, you can start right away.
What is reporting breaches?
Reporting breaches is the act of notifying the relevant authorities about a security incident or data breach.
Who is required to file reporting breaches?
Any organization or entity that experiences a security incident or data breach is required to file reporting breaches.
How to fill out reporting breaches?
Reporting breaches can be filled out by providing all the necessary details about the security incident or data breach, including when it occurred, how it happened, and what data was compromised.
What is the purpose of reporting breaches?
The purpose of reporting breaches is to ensure transparency and accountability in the handling of security incidents or data breaches, as well as to prevent future occurrences.
What information must be reported on reporting breaches?
Information that must be reported on reporting breaches includes the nature of the security incident or data breach, the date and time it occurred, the type of data that was compromised, and any actions taken to mitigate the impact.
Fill out your reporting breaches online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Reporting Breaches is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.