Get the free Techniques for bpermittingb access across a context barrier in a small bb
Show details
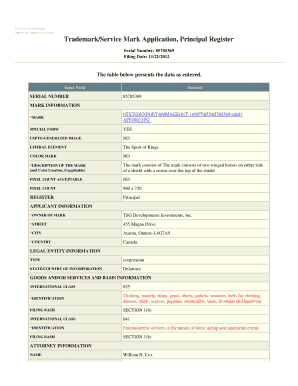
US007395535B2 (12) Bulleted States Patent (10) Patent N0.: Sussex et a . (54) US 7,395,535 B2 (45) Date of Patent: TECHNIQUES FOR PERMITTING ACCESS 5,204,897 A *Jul. 1, 2008 4/1993 Woman ACROSS A
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign techniques for bpermittingb access

Edit your techniques for bpermittingb access form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your techniques for bpermittingb access form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit techniques for bpermittingb access online
To use our professional PDF editor, follow these steps:
1
Log in to your account. Start Free Trial and sign up a profile if you don't have one.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit techniques for bpermittingb access. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
It's easier to work with documents with pdfFiller than you could have believed. Sign up for a free account to view.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out techniques for bpermittingb access

To fill out techniques for permitting access, follow these steps:
01
Start by identifying the specific access requirements or criteria that need to be addressed in the techniques.
02
Research and gather information on the different types of permits or access permissions that may be required in your particular situation.
03
Create a comprehensive list of the techniques or practices that can be implemented to facilitate the permitting process.
04
Organize the techniques in a structured manner, such as categorizing them based on the type of access or the steps involved in obtaining permits.
05
Provide detailed instructions or explanations for each technique, including any necessary documentation, forms, or applications that need to be filled out.
06
Include any relevant regulations, laws, or guidelines that should be followed when applying the techniques for permitting access.
07
If applicable, mention any potential challenges or obstacles that may arise during the permitting process and provide strategies or solutions for overcoming them.
08
Review and revise the techniques as needed to ensure they are accurate, up-to-date, and in compliance with any changes in regulations or requirements.
8.1
Techniques for permitting access can be useful for a wide range of individuals or organizations. These may include:
09
Construction companies and contractors: They often require various permits and access rights to carry out their projects, such as building permits, safety permits, or permits for accessing restricted areas.
10
Facility managers or property owners: They need to understand the techniques for permitting access to ensure compliance with safety regulations, security protocols, and environmental guidelines.
11
Event organizers: They may need to obtain permits for hosting events in public or private spaces, including permits for temporary structures, noise permits, or permits to access roadways.
12
Government agencies or departments: They may use techniques for permitting access to regulate activities in certain areas, such as permits for fishing, camping, hunting, or exploration.
13
Environmental professionals: They often require permits for conducting surveys, research, or data collection in protected or sensitive areas, including permits for accessing national parks, wildlife reserves, or marine sanctuaries.
14
Transportation companies: They may need to obtain permits for operating vehicles or transporting goods through certain routes or jurisdictions, such as oversize permits, overweight permits, or hazardous materials permits.
In summary, techniques for permitting access are valuable for anyone involved in obtaining the necessary permissions, rights, or authorizations to carry out specific activities or gain access to restricted areas. By following the step-by-step process and understanding who can benefit from these techniques, individuals and organizations can navigate the permitting process more efficiently and effectively.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is techniques for permitting access?
Techniques for permitting access refer to the methods and processes used to grant or provide access to a particular system, resource, or information.
Who is required to file techniques for permitting access?
Individuals or entities responsible for managing access to a system or resource are required to file techniques for permitting access.
How to fill out techniques for permitting access?
Techniques for permitting access are typically filled out by documenting the steps and procedures involved in granting access, including any necessary permissions or restrictions.
What is the purpose of techniques for permitting access?
The purpose of techniques for permitting access is to ensure that access to a system or resource is granted in a controlled and secure manner, following established protocols.
What information must be reported on techniques for permitting access?
Techniques for permitting access must include details such as user identities, access levels, authentication methods, and any relevant access control policies.
Where do I find techniques for bpermittingb access?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific techniques for bpermittingb access and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
How do I edit techniques for bpermittingb access online?
pdfFiller not only allows you to edit the content of your files but fully rearrange them by changing the number and sequence of pages. Upload your techniques for bpermittingb access to the editor and make any required adjustments in a couple of clicks. The editor enables you to blackout, type, and erase text in PDFs, add images, sticky notes and text boxes, and much more.
How do I edit techniques for bpermittingb access on an Android device?
Yes, you can. With the pdfFiller mobile app for Android, you can edit, sign, and share techniques for bpermittingb access on your mobile device from any location; only an internet connection is needed. Get the app and start to streamline your document workflow from anywhere.
Fill out your techniques for bpermittingb access online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Techniques For Bpermittingb Access is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.