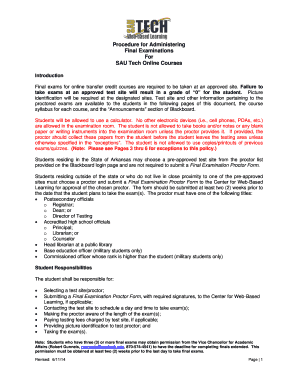
Get the free Social Engineering - sans
Show details
Interested in learning more about security? SANS Institute InfoSec Reading Room This paper is from the SANS Institute Reading Room site. Reposting is not permitted without express written permission.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign social engineering - sans

Edit your social engineering - sans form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your social engineering - sans form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit social engineering - sans online
To use our professional PDF editor, follow these steps:
1
Log into your account. It's time to start your free trial.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit social engineering - sans. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
Dealing with documents is always simple with pdfFiller. Try it right now
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out social engineering - sans

How to Fill Out Social Engineering:
01
Social engineering refers to the manipulation of individuals through psychological tactics, in order to gain unauthorized access to information and systems. To fill out social engineering, one needs to understand the various techniques and strategies used in this field.
02
The first step in filling out social engineering is to study the different types of social engineering attacks, such as phishing, pretexting, baiting, and tailgating. Each attack method involves different approaches to deceive and manipulate targets.
03
Once familiar with the attack methods, it is important to understand the psychology behind social engineering. This includes studying human behavior, cognitive biases, and emotional triggers that can be exploited to persuade individuals to divulge sensitive information or perform certain actions.
04
To fill out social engineering effectively, one must also learn the art of pretexting, which involves creating a plausible scenario or pretext to deceive the target. This can be done by gathering relevant information about the target and customizing the pretext accordingly.
05
Additionally, acquiring knowledge about social engineering tools and techniques can greatly enhance one's ability to fill out social engineering. This may include learning about reconnaissance techniques, creating convincing phishing emails, or using social media manipulation to gather information.
06
It is crucial to stay updated on the latest social engineering trends, as attackers continuously evolve their tactics. Following reputable sources, attending security conferences, and participating in online forums can help in staying informed about emerging threats and countermeasures.
07
Regularly practicing and simulating social engineering scenarios can greatly improve one's skills in this area. Organizations often conduct social engineering assessments to identify vulnerabilities in their systems and train employees on how to recognize and defend against social engineering attacks.
Who Needs Social Engineering:
01
Social engineering is a topic that is relevant to a wide range of individuals and organizations. Anyone who uses technology, handles sensitive information, or has online presence needs to be aware of social engineering.
02
Businesses and organizations of all sizes can benefit from understanding social engineering, as it helps identify and mitigate vulnerabilities in their systems and educate employees about the risks involved.
03
IT professionals, information security specialists, and cybersecurity experts should have a deep understanding of social engineering, as they play a critical role in protecting networks and data from social engineering attacks.
04
Individuals who regularly use online services, such as email, social media, or online banking, need to be aware of social engineering techniques in order to protect their personal information from being exploited.
05
Government agencies and law enforcement bodies should have knowledge about social engineering to combat cybercrime and protect national security.
06
Educators and parents can also benefit from understanding social engineering, as they can teach students and children about the risks and help them develop critical thinking skills to identify and prevent social engineering attacks.
07
Ultimately, anyone who wants to enhance their cybersecurity awareness and protect themselves, their businesses, or their clients from social engineering attacks can benefit from learning about and utilizing social engineering techniques.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I create an electronic signature for the social engineering - sans in Chrome?
Yes, you can. With pdfFiller, you not only get a feature-rich PDF editor and fillable form builder but a powerful e-signature solution that you can add directly to your Chrome browser. Using our extension, you can create your legally-binding eSignature by typing, drawing, or capturing a photo of your signature using your webcam. Choose whichever method you prefer and eSign your social engineering - sans in minutes.
How do I edit social engineering - sans straight from my smartphone?
You may do so effortlessly with pdfFiller's iOS and Android apps, which are available in the Apple Store and Google Play Store, respectively. You may also obtain the program from our website: https://edit-pdf-ios-android.pdffiller.com/. Open the application, sign in, and begin editing social engineering - sans right away.
How do I fill out social engineering - sans on an Android device?
On Android, use the pdfFiller mobile app to finish your social engineering - sans. Adding, editing, deleting text, signing, annotating, and more are all available with the app. All you need is a smartphone and internet.
What is social engineering?
Social engineering is a manipulation technique used by cybercriminals to trick individuals into divulging confidential information or performing actions that may compromise security.
Who is required to file social engineering?
Any individual or organization that collects or maintains sensitive information about individuals is required to file social engineering.
How to fill out social engineering?
Social engineering reports can be filled out online through the designated portal provided by regulatory bodies.
What is the purpose of social engineering?
The purpose of social engineering is to raise awareness about potential security threats and help organizations protect sensitive information from malicious actors.
What information must be reported on social engineering?
Social engineering reports typically include details of attempted or successful security breaches, information on the methods used by cybercriminals, and any potential impact on affected individuals or organizations.
Fill out your social engineering - sans online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Social Engineering - Sans is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.