Get the free ISACA Authorized Cybersecurity Training Partner Application - cybersecurity isaca
Show details
ISACA Authorized Cybersecurity Training Partner Application Please complete this application to indicate your interest in becoming an ISACA Authorized Cybersecurity Training Partner. Please then email
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign isaca authorized cybersecurity training
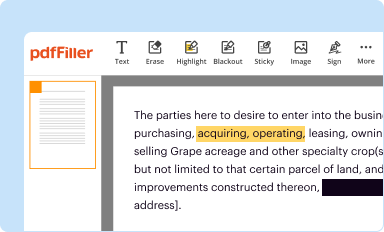
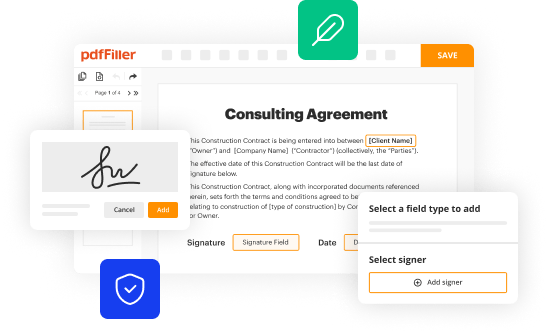
Edit your isaca authorized cybersecurity training form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
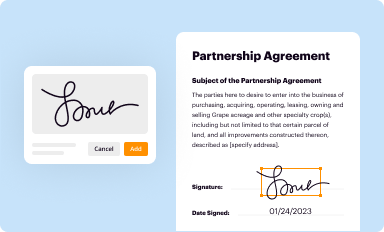
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
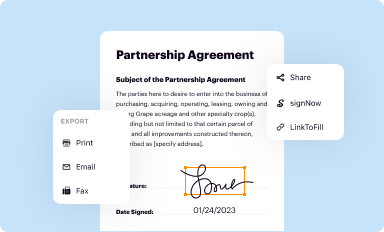
Share your form instantly
Email, fax, or share your isaca authorized cybersecurity training form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing isaca authorized cybersecurity training online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit isaca authorized cybersecurity training. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, it's always easy to deal with documents. Try it right now
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out isaca authorized cybersecurity training
How to fill out ISACA authorized cybersecurity training:
01
Visit the ISACA website: Start by visiting the official website of ISACA, the organization that provides authorized cybersecurity training. Navigate to the training section of their website.
02
Choose the desired training course: Explore the available cybersecurity training courses offered by ISACA. Look for the one that best fits your needs and career goals. Consider factors such as the level of expertise required, the duration of the course, and any prerequisites.
03
Review the course details: Once you have selected a particular cybersecurity training course, carefully read through the course details and requirements. Ensure that you meet all the eligibility criteria and have the necessary technical knowledge or experience.
04
Register for the course: After reviewing the course details, proceed to register for the ISACA authorized cybersecurity training course. Follow the instructions provided on the website for registration. This may involve creating an account, providing personal information, and making payment for the course.
05
Access course materials: Once your registration is confirmed, you will typically receive access to the course materials. These materials may include online modules, videos, practice exams, and other resources. Familiarize yourself with the course structure and start studying the provided materials.
06
Engage in practical exercises: Many ISACA authorized cybersecurity training courses include practical exercises or simulations to enhance learning. Take advantage of these opportunities to apply the concepts and techniques taught in the course.
07
Attend live or virtual sessions: Depending on the course format, you may have the opportunity to attend live or virtual instructor-led sessions. These sessions can provide valuable insights and allow you to interact with industry professionals and fellow participants.
Who needs ISACA authorized cybersecurity training?
01
IT Professionals: ISACA authorized cybersecurity training is highly beneficial for IT professionals working in various roles, such as network administrators, system analysts, IT auditors, and cybersecurity specialists. These individuals can enhance their knowledge and skills to effectively protect their organization's systems and data.
02
Security Analysts: Security analysts, who are responsible for assessing and mitigating risks, can benefit from ISACA authorized cybersecurity training. It equips them with the latest techniques and methodologies to identify vulnerabilities and develop robust security measures.
03
IT Audit Professionals: Professionals involved in IT auditing can greatly benefit from ISACA authorized cybersecurity training. It helps them understand the evolving threat landscape and develop appropriate controls and measures to ensure data confidentiality, integrity, and availability.
04
Individuals pursuing cybersecurity careers: Anyone aspiring to pursue a career in cybersecurity can greatly benefit from ISACA authorized cybersecurity training. It provides a comprehensive foundation in cybersecurity principles and practices, along with industry-recognized certifications that can enhance career prospects.
05
Managers and decision-makers: Even non-technical professionals, such as managers and decision-makers, can benefit from ISACA authorized cybersecurity training. Understanding the fundamentals of cybersecurity helps them make informed decisions regarding risk management, compliance, and implementing effective security strategies within their organizations.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send isaca authorized cybersecurity training for eSignature?
Once you are ready to share your isaca authorized cybersecurity training, you can easily send it to others and get the eSigned document back just as quickly. Share your PDF by email, fax, text message, or USPS mail, or notarize it online. You can do all of this without ever leaving your account.
How do I edit isaca authorized cybersecurity training online?
With pdfFiller, it's easy to make changes. Open your isaca authorized cybersecurity training in the editor, which is very easy to use and understand. When you go there, you'll be able to black out and change text, write and erase, add images, draw lines, arrows, and more. You can also add sticky notes and text boxes.
Can I create an electronic signature for signing my isaca authorized cybersecurity training in Gmail?
You can easily create your eSignature with pdfFiller and then eSign your isaca authorized cybersecurity training directly from your inbox with the help of pdfFiller’s add-on for Gmail. Please note that you must register for an account in order to save your signatures and signed documents.
What is isaca authorized cybersecurity training?
ISACA authorized cybersecurity training is training that has been approved by ISACA, a global professional association focused on IT governance. This training is designed to improve individuals' cybersecurity knowledge and skills.
Who is required to file isaca authorized cybersecurity training?
Individuals working in cybersecurity roles or those looking to advance their careers in cybersecurity may be required to complete ISACA authorized cybersecurity training.
How to fill out isaca authorized cybersecurity training?
ISACA authorized cybersecurity training can be filled out by enrolling in an approved training course, attending all sessions, and successfully completing any assessments or exams.
What is the purpose of isaca authorized cybersecurity training?
The purpose of ISACA authorized cybersecurity training is to enhance individuals' cybersecurity expertise, expand their professional network, and improve their career prospects in the cybersecurity field.
What information must be reported on isaca authorized cybersecurity training?
Information such as the training provider, course name, completion date, and any certifications obtained must be reported on ISACA authorized cybersecurity training.
Fill out your isaca authorized cybersecurity training online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Isaca Authorized Cybersecurity Training is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.