Get the free Request to Access Protected Health Information (PHI). Request to Access Protected He...
Show details
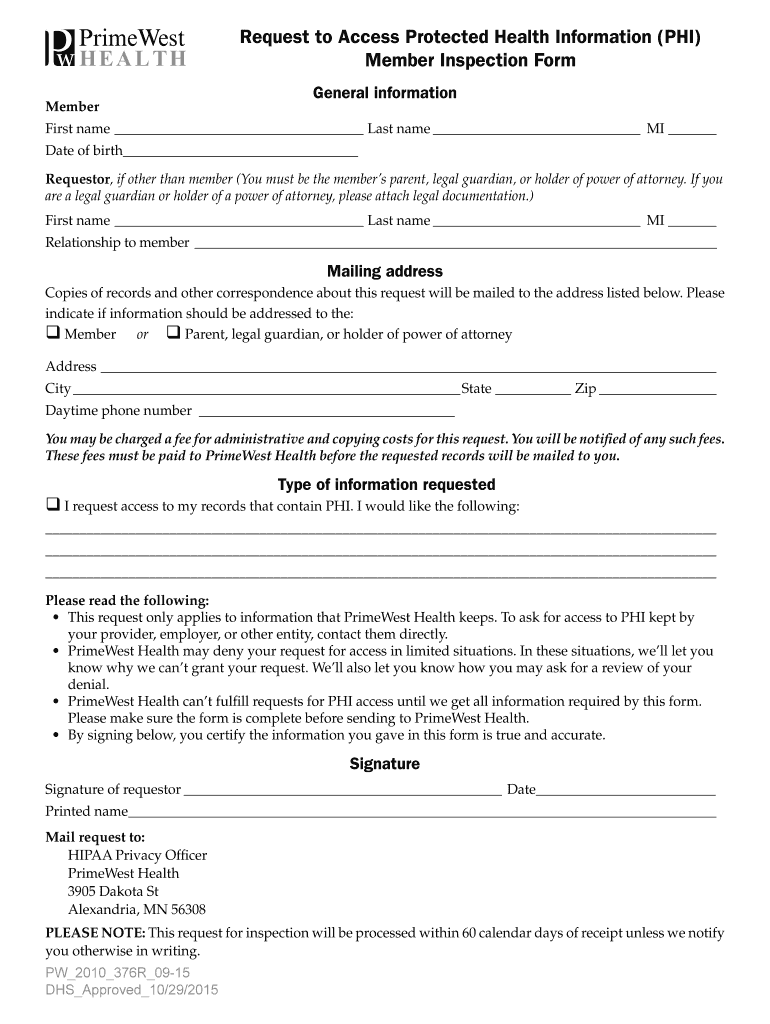
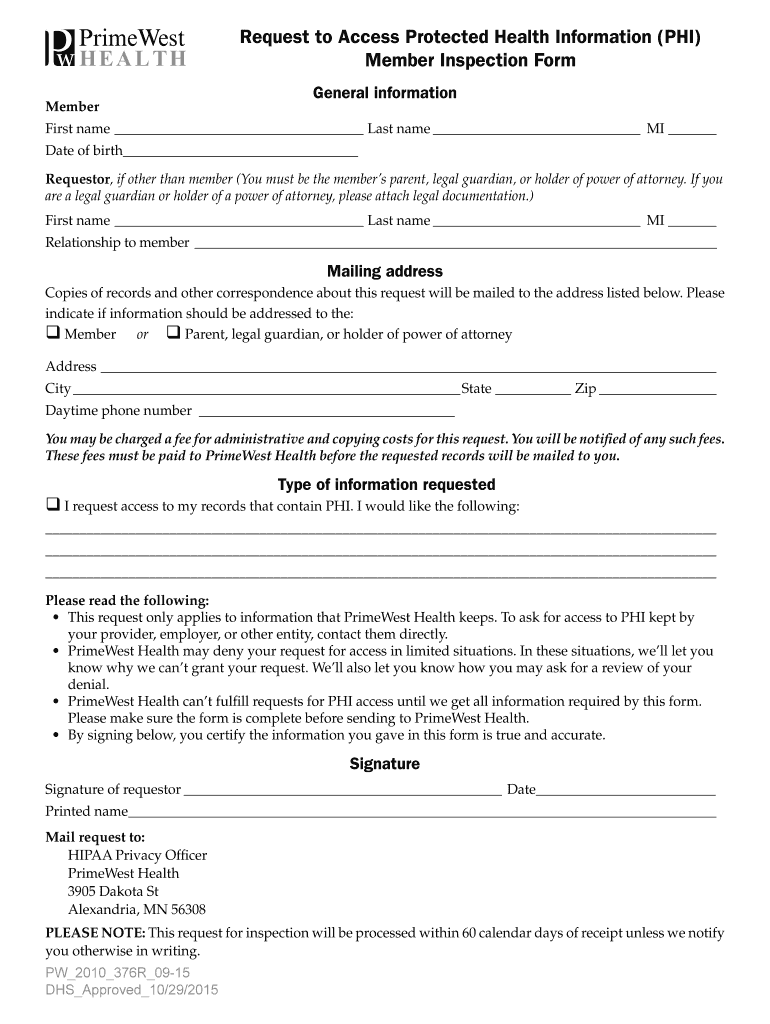
Request to Access Protected Health Information (PHI) Member Inspection Form Member General information First name Last name MI Date of birth Requestor, if other than member (You must be the members
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign request to access protected
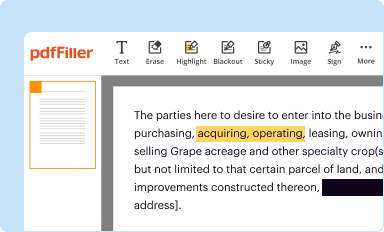
Edit your request to access protected form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
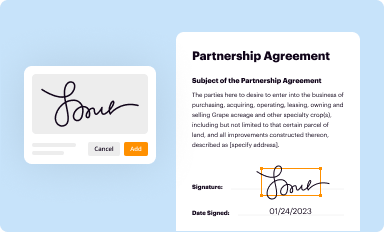
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
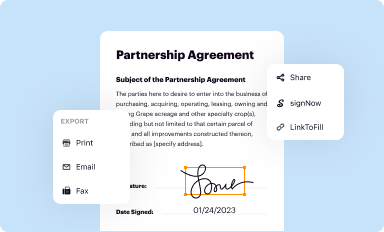
Share your form instantly
Email, fax, or share your request to access protected form via URL. You can also download, print, or export forms to your preferred cloud storage service.
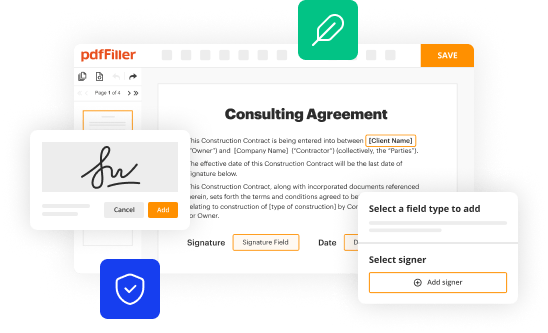
How to edit request to access protected online
To use our professional PDF editor, follow these steps:
1
Check your account. In case you're new, it's time to start your free trial.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit request to access protected. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Try it right now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out request to access protected
To fill out a request to access protected, follow these steps:
01
Start by clearly stating the purpose of your request. This will help the recipient understand why you need access to the protected content. Be concise and specific in your explanation.
02
Provide your personal information, including your full name, contact details, and any relevant identification numbers or credentials. This will help the recipient identify and verify your identity.
03
Specify the exact content or resources you are seeking access to. Include any relevant details such as the location, timeframe, or specific files or information required. This will help the recipient understand the scope of your request.
04
Explain your reasons for needing access to the protected content. This could involve stating your role or responsibilities that require access, or explaining the potential benefits or importance of gaining access.
05
Indicate the duration of access you are requesting. Whether it's a one-time access or a regular basis, be clear about the timeframe or period for which you require access.
06
If applicable, provide any supporting documents or evidence that can strengthen your case for access. This could include letters of recommendation, previous relevant experience, or any other documentation that demonstrates your need for the protected content.
07
Finally, conclude your request by expressing your gratitude and willingness to comply with any terms or conditions associated with the access to the protected content.
Who needs a request to access protected?
Individuals or entities who require access to protected content or resources can submit a request for access. This could include employees seeking access to restricted company files, researchers requesting access to confidential data, or individuals looking to obtain permission to view protected online content. The need for a request to access protected may vary depending on the policies and protocols set by the content owner or governing authority. It is important to familiarize yourself with the specific procedures and requirements for each situation to ensure a successful request.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my request to access protected in Gmail?
It's easy to use pdfFiller's Gmail add-on to make and edit your request to access protected and any other documents you get right in your email. You can also eSign them. Take a look at the Google Workspace Marketplace and get pdfFiller for Gmail. Get rid of the time-consuming steps and easily manage your documents and eSignatures with the help of an app.
How do I make edits in request to access protected without leaving Chrome?
Get and add pdfFiller Google Chrome Extension to your browser to edit, fill out and eSign your request to access protected, which you can open in the editor directly from a Google search page in just one click. Execute your fillable documents from any internet-connected device without leaving Chrome.
How do I fill out the request to access protected form on my smartphone?
You can quickly make and fill out legal forms with the help of the pdfFiller app on your phone. Complete and sign request to access protected and other documents on your mobile device using the application. If you want to learn more about how the PDF editor works, go to pdfFiller.com.
Fill out your request to access protected online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Request To Access Protected is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.