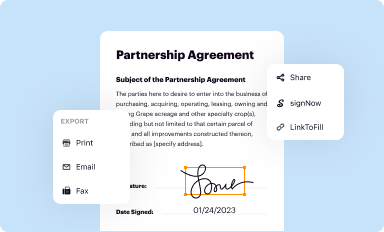
Get the free MANAGING STUDENT THREATS AND RISK
Show details
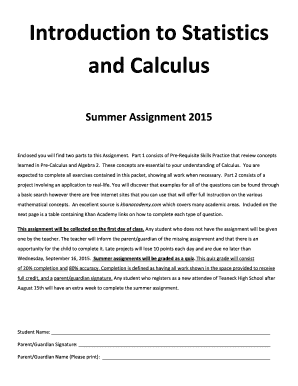
WEBCAST MANAGING STUDENT THREATS AND RISK: EFFECT TIME POLICIES AND PR ACT ICES November 14, 19 & 26, 2012 :: 1:00 2:30 p.m. EST OF E R V I E W Recent campus tragedies involving students with psychological
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign managing student threats and
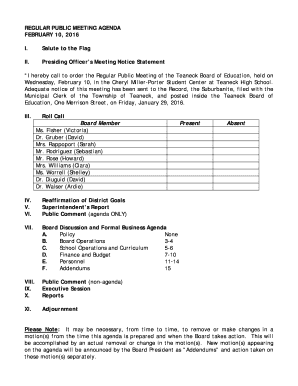
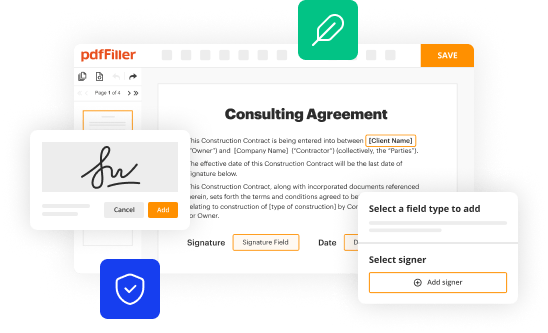
Edit your managing student threats and form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
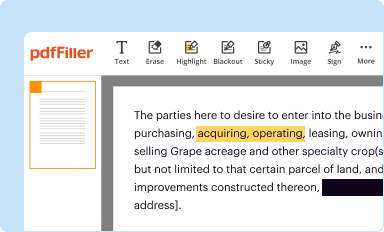
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
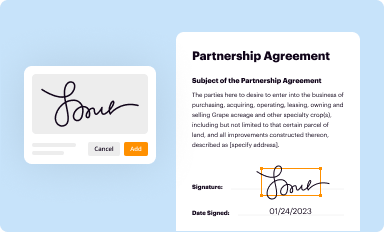
Share your form instantly
Email, fax, or share your managing student threats and form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit managing student threats and online
To use our professional PDF editor, follow these steps:
1
Log in to your account. Click on Start Free Trial and sign up a profile if you don't have one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit managing student threats and. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out managing student threats and
How to fill out managing student threats and:
01
Start by gathering all relevant information about the student and the threat. This includes the student's name, age, grade level, and any previous incidents or disciplinary actions.
02
Clearly identify the nature of the threat. Is it physical, verbal, or cyber-related? Determine if it is directed towards a specific individual or a general threat to the school community.
03
Evaluate the severity of the threat. Determine if it is a low-level, moderate, or high-level threat. Consider factors such as the credibility of the threat, the presence of any weapons, and the potential harm it poses.
04
Document the threat in detail. Write down exactly what was said or done, including any specific language, gestures, or actions. Make sure to include the date, time, and location of the threat.
05
Notify the appropriate authorities. Depending on the severity of the threat, this could include the school administration, the school resource officer, local law enforcement, or the district superintendent. Provide them with all the information you have gathered.
06
Implement any necessary safety measures. If the threat is deemed credible or poses immediate danger, take any necessary steps to protect the potential victims and the school community. This may include implementing a lockdown, increasing security measures, or arranging for counseling support for affected individuals.
Who needs managing student threats and:
01
School administrators: They play a crucial role in managing student threats by ensuring that appropriate protocols are followed, coordinating with law enforcement if necessary, and implementing preventive measures to maintain a safe learning environment.
02
School staff and teachers: They need to be aware of the processes and procedures for managing student threats in order to promptly report any threats they may come across. They need to work collaboratively with administrators to create a safe and supportive environment for all students.
03
Students' parents or guardians: It is important for parents or guardians to understand the procedures involved in managing student threats. They should be informed about any threats involving their child and be kept up-to-date on any actions taken by the school to ensure their child's safety.
04
Law enforcement agencies: They need to be informed of any threats made by students that may constitute a criminal offense. They can provide guidance, expertise, and support in managing and investigating serious threats.
05
Mental health professionals: They play a vital role in managing student threats by providing counseling and support services to both the students making threats and the potential victims. They can also assist in assessing the level of risk and developing intervention plans.
Overall, managing student threats requires a collaborative effort from various stakeholders, including school administrators, staff, parents, law enforcement, and mental health professionals. By following proper procedures and involving the necessary individuals, threats can be effectively addressed and the safety of the school community can be upheld.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send managing student threats and for eSignature?
When you're ready to share your managing student threats and, you can swiftly email it to others and receive the eSigned document back. You may send your PDF through email, fax, text message, or USPS mail, or you can notarize it online. All of this may be done without ever leaving your account.
Where do I find managing student threats and?
The premium version of pdfFiller gives you access to a huge library of fillable forms (more than 25 million fillable templates). You can download, fill out, print, and sign them all. State-specific managing student threats and and other forms will be easy to find in the library. Find the template you need and use advanced editing tools to make it your own.
Can I create an electronic signature for the managing student threats and in Chrome?
Yes, you can. With pdfFiller, you not only get a feature-rich PDF editor and fillable form builder but a powerful e-signature solution that you can add directly to your Chrome browser. Using our extension, you can create your legally-binding eSignature by typing, drawing, or capturing a photo of your signature using your webcam. Choose whichever method you prefer and eSign your managing student threats and in minutes.
What is managing student threats and?
Managing student threats and involves identifying, assessing, and addressing potential threats made by students in an educational setting.
Who is required to file managing student threats and?
School administrators, teachers, and counselors are typically required to file managing student threats and reports.
How to fill out managing student threats and?
To fill out managing student threats and, individuals must document the threat, assess its credibility, and develop a plan to address it.
What is the purpose of managing student threats and?
The purpose of managing student threats and is to ensure the safety and well-being of students, staff, and the school community by proactively addressing potential threats.
What information must be reported on managing student threats and?
Information reported on managing student threats and usually includes details of the threat, the person making the threat, actions taken, and any follow-up measures.
Fill out your managing student threats and online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Managing Student Threats And is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.