Get the free Network Security Technologies - FTP Directory Listing
Show details
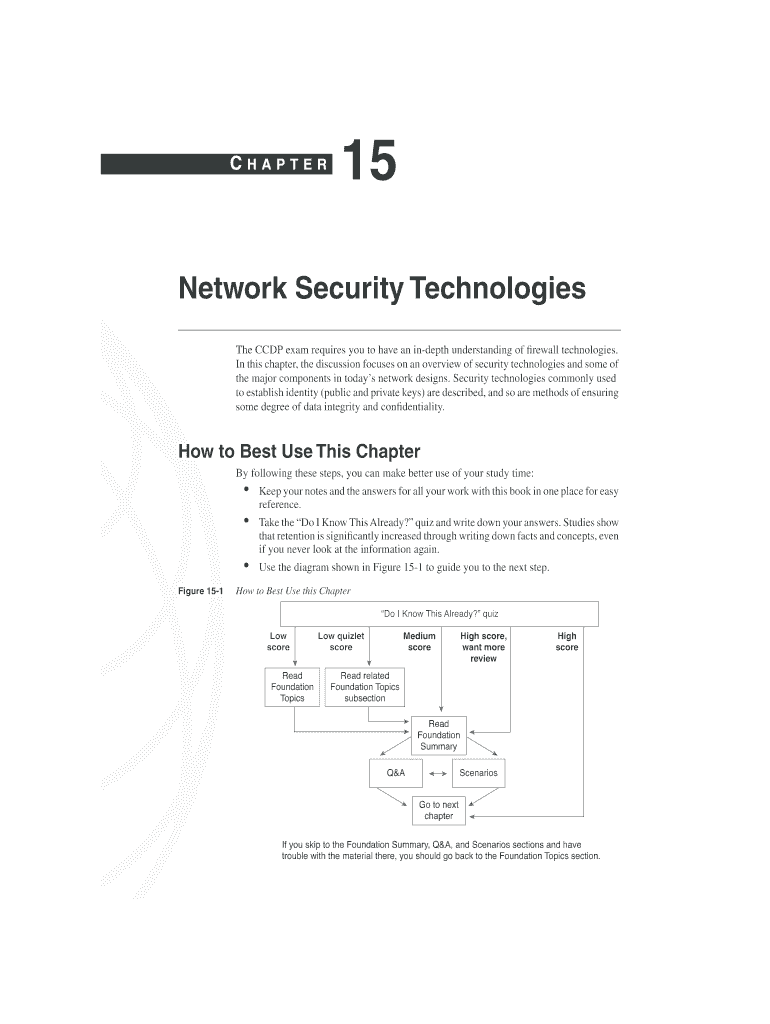
87200333.book Page 551 Wednesday, August 22, 2001 1:41 PM CHAPTER 15 Network Security Technologies The CCD exam requires you to have an in depth understanding of recall technologies. In this chapter,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign network security technologies

Edit your network security technologies form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your network security technologies form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit network security technologies online
In order to make advantage of the professional PDF editor, follow these steps:
1
Sign into your account. It's time to start your free trial.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit network security technologies. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
Dealing with documents is simple using pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out network security technologies

How to fill out network security technologies:
01
Identify your network's vulnerabilities: Conduct a comprehensive assessment of your network to identify any potential weaknesses or vulnerabilities. This can include conducting penetration tests, vulnerability scans, and reviewing network configurations.
02
Implement strong access controls: Establish user access controls and ensure that only authorized individuals have access to network resources. This can involve implementing strong password policies, two-factor authentication, and role-based access controls.
03
Encrypt network traffic: Ensure that all sensitive data transmitted over your network is encrypted to protect it from unauthorized access. This can be done through the use of protocols such as SSL/TLS, VPNs, and encryption algorithms.
04
Establish intrusion detection and prevention systems: Implement systems that can detect and prevent unauthorized access or malicious activity on your network. This can involve using firewalls, intrusion detection systems, and network behavior analysis tools.
05
Regularly update and patch network devices: Keep your network devices and software up to date with the latest security patches and updates. This helps protect against known vulnerabilities that attackers might exploit.
06
Educate and train employees: Provide ongoing training and education to employees about network security best practices. This can include teaching them how to identify and report phishing emails, how to create strong passwords, and how to use network resources securely.
Who needs network security technologies:
01
Businesses: Organizations of all sizes and industries need network security technologies to protect their sensitive data, intellectual property, and customer information. This includes sectors such as finance, healthcare, and government.
02
Home users: Individuals who use the internet at home for tasks such as online banking, shopping, or social media also need network security technologies to protect their personal information and ensure their online privacy.
03
Government agencies: Government agencies require robust network security technologies to safeguard national security information, critical infrastructure, and confidential government data.
04
Educational institutions: Schools and universities need network security technologies to protect student and staff information, as well as to secure their research and intellectual property.
05
Non-profit organizations: Non-profit organizations also need network security technologies to protect their donor information, as well as to ensure the security and privacy of the individuals they serve.
In conclusion, network security technologies are essential for protecting network infrastructures and the sensitive data they handle. By following best practices and implementing appropriate security measures, both individuals and organizations can safeguard against potential threats and mitigate the risks associated with network vulnerabilities.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I get network security technologies?
It's simple with pdfFiller, a full online document management tool. Access our huge online form collection (over 25M fillable forms are accessible) and find the network security technologies in seconds. Open it immediately and begin modifying it with powerful editing options.
How do I execute network security technologies online?
Easy online network security technologies completion using pdfFiller. Also, it allows you to legally eSign your form and change original PDF material. Create a free account and manage documents online.
How can I edit network security technologies on a smartphone?
You can do so easily with pdfFiller’s applications for iOS and Android devices, which can be found at the Apple Store and Google Play Store, respectively. Alternatively, you can get the app on our web page: https://edit-pdf-ios-android.pdffiller.com/. Install the application, log in, and start editing network security technologies right away.
What is network security technologies?
Network security technologies refer to tools, policies, and practices put in place to protect a network from unauthorized access, misuse, or disruption.
Who is required to file network security technologies?
Network security technologies may need to be implemented by organizations, businesses, or individuals that rely on computer networks to protect sensitive information and ensure secure communication.
How to fill out network security technologies?
Filling out network security technologies involves assessing the security needs of a network, selecting appropriate security measures, implementing them, and regularly updating and monitoring the network security.
What is the purpose of network security technologies?
The purpose of network security technologies is to safeguard networks and the data they transmit or store from potential threats such as hackers, malware, and unauthorized access.
What information must be reported on network security technologies?
The information that must be reported on network security technologies may include the types of security measures implemented, any incidents or breaches that occurred, and the effectiveness of the security measures.
Fill out your network security technologies online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Network Security Technologies is not the form you're looking for?Search for another form here.
Relevant keywords
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.