Get the free Policy Name Information Security Incident Management
Show details
RUTGERS POLICY Section: 70.2.20 Section Title: Legacy UMD NJ policies associated with Information Technology Policy Name: Information Security: Incident Management Formerly Book: 95010902:00 Approval
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign policy name information security

Edit your policy name information security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your policy name information security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing policy name information security online
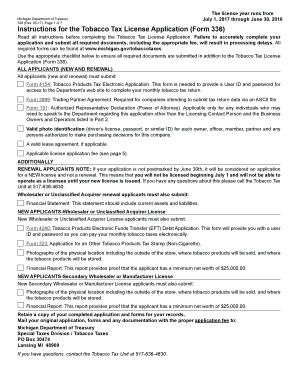
Follow the guidelines below to benefit from a competent PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit policy name information security. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out policy name information security

How to fill out policy name information security:
01
Start by clearly identifying the purpose and scope of the policy. This includes stating the objectives and goals of the policy, as well as defining the domains and assets that are covered.
02
Next, outline the roles and responsibilities of the individuals involved in implementing and enforcing the policy. Specify who is responsible for maintaining and updating the policy, as well as who is accountable for ensuring compliance.
03
Provide a detailed description of the security measures and protocols that should be followed. This may include guidelines on access control, data protection, incident response, and other relevant areas. Be sure to reference any applicable laws, regulations, or industry standards.
04
Consider including a section on employee awareness and training. Highlight the importance of educating staff members about the policy, and provide resources or procedures for delivering training sessions or raising awareness about information security best practices.
05
Finally, establish a review and update process to ensure that the policy remains relevant and effective. Set intervals for reviewing the policy, and determine how changes or updates will be communicated and implemented.
Who needs policy name information security:
01
Organizations of all sizes and industries can benefit from having an information security policy. It is essential for any entity that handles sensitive or confidential data, regardless of whether it is stored electronically or in physical format.
02
Policy name information security is particularly important for companies that operate in regulated industries, such as finance, healthcare, or government. It helps ensure compliance with industry-specific regulations and standards, and provides a framework for protecting critical information assets.
03
Additionally, policy name information security is relevant for organizations that want to establish a culture of security and risk management. By having a formal policy in place, businesses can demonstrate their commitment to safeguarding information and maintaining customer trust.
Remember, creating and implementing an information security policy requires careful consideration and involvement from various stakeholders. It should be a collaborative effort involving management, IT personnel, legal advisors, and other relevant parties to ensure its effectiveness and adherence.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send policy name information security for eSignature?
When you're ready to share your policy name information security, you can send it to other people and get the eSigned document back just as quickly. Share your PDF by email, fax, text message, or USPS mail. You can also notarize your PDF on the web. You don't have to leave your account to do this.
Can I create an eSignature for the policy name information security in Gmail?
Upload, type, or draw a signature in Gmail with the help of pdfFiller’s add-on. pdfFiller enables you to eSign your policy name information security and other documents right in your inbox. Register your account in order to save signed documents and your personal signatures.
How do I fill out policy name information security using my mobile device?
Use the pdfFiller mobile app to fill out and sign policy name information security on your phone or tablet. Visit our website to learn more about our mobile apps, how they work, and how to get started.
What is policy name information security?
Policy name information security refers to the specific policy established to protect sensitive information and data from unauthorized access or disclosure.
Who is required to file policy name information security?
All employees and contractors who have access to sensitive information are required to adhere to the policy name information security.
How to fill out policy name information security?
Policy name information security can be filled out by reviewing and understanding the guidelines outlined in the policy document, and ensuring compliance with its requirements.
What is the purpose of policy name information security?
The purpose of policy name information security is to safeguard confidential data and information from security breaches, ensuring the protection of sensitive assets.
What information must be reported on policy name information security?
Information such as access controls, data encryption methods, security protocols, and incident response procedures must be reported in policy name information security.
Fill out your policy name information security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Policy Name Information Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.