Get the free Social engineering attacks: What we can
Show details
9SearchFinancialSecuritySocial engineering attacks: What we can
learn from Kevin Mitnickgzby Mark T. Edge this article provides examples of how to strengthen your organization against social
engineering.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign social engineering attacks what
Edit your social engineering attacks what form online
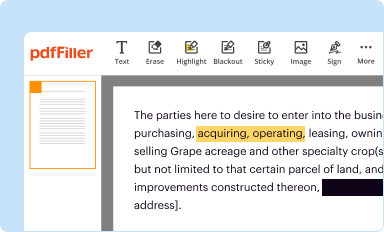
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
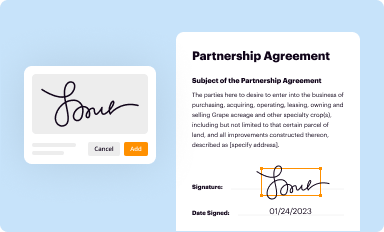
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your social engineering attacks what form via URL. You can also download, print, or export forms to your preferred cloud storage service.
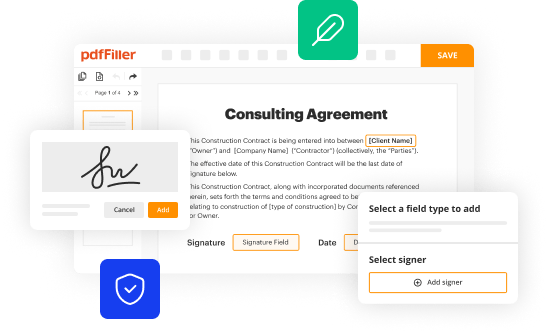
Editing social engineering attacks what online
Follow the guidelines below to use a professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit social engineering attacks what. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out social engineering attacks what
How to fill out social engineering attacks:
01
Develop a clear objective for the social engineering attack. Determine what information or action you are trying to obtain from your target.
02
Research and gather intelligence about the target. Understanding their habits, interests, and online presence can help you craft a more convincing attack.
03
Choose the right method for the attack. Social engineering attacks can take many forms, such as phishing emails, phone calls, or physical impersonation. Select the method that best aligns with your objective and target.
04
Craft a compelling story or scenario to deceive the target. This could be a sense of urgency, a tempting offer, or a request for assistance. Make sure the story aligns with the target's interests or concerns.
05
Use social engineering techniques to establish trust and rapport with the target. This could involve mimicking their language or behavior, providing personal information, or leveraging relationships or connections they may have.
06
Execute the attack by delivering the bait, whether it's through an email, phone call, or in-person interaction. Pay attention to your timing, tone, and preparation to increase the chances of success.
07
Continuously refine and adapt your social engineering tactics. Learn from each attack and improve your techniques to increase your chances of success in future attempts.
Who needs social engineering attacks:
01
Criminal hackers: These individuals may use social engineering attacks as part of their overall hacking strategies to gain unauthorized access to systems or steal sensitive information.
02
Organizations conducting security assessments: Some companies employ social engineering tactics to test the effectiveness of their security measures and identify vulnerabilities that could be exploited.
03
Intelligence agencies and law enforcement: These entities may employ social engineering attacks as part of their investigations to gather intelligence, monitor suspects, or gather evidence in criminal cases.
04
Security professionals: Individuals working in the field of cybersecurity, specifically in the area of social engineering prevention and detection, may conduct social engineering attacks to better understand the tactics used and develop effective countermeasures.
05
Ethical hackers: Also known as white hat hackers, these individuals may use social engineering attacks with the permission of organizations to identify and address vulnerabilities in their security systems.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find social engineering attacks what?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific social engineering attacks what and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
How do I make changes in social engineering attacks what?
With pdfFiller, the editing process is straightforward. Open your social engineering attacks what in the editor, which is highly intuitive and easy to use. There, you’ll be able to blackout, redact, type, and erase text, add images, draw arrows and lines, place sticky notes and text boxes, and much more.
How do I edit social engineering attacks what on an Android device?
You can make any changes to PDF files, such as social engineering attacks what, with the help of the pdfFiller mobile app for Android. Edit, sign, and send documents right from your mobile device. Install the app and streamline your document management wherever you are.
What is social engineering attacks what?
Social engineering attacks are a type of cyber attack that manipulates people into divulging confidential information or performing actions that may compromise security.
Who is required to file social engineering attacks what?
Any individual or organization that suspects they have been targeted by a social engineering attack should file a report.
How to fill out social engineering attacks what?
To fill out a report on social engineering attacks, include details of the incident, any information disclosed, and any actions taken.
What is the purpose of social engineering attacks what?
The purpose of social engineering attacks is to deceive individuals into revealing sensitive information or performing actions that may lead to a security breach.
What information must be reported on social engineering attacks what?
Reports on social engineering attacks should include details of the incident, any information disclosed or actions taken, and any potential security risks.
Fill out your social engineering attacks what online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Social Engineering Attacks What is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.