Get the free Identity and Access Management Assessment and Grouper
Show details
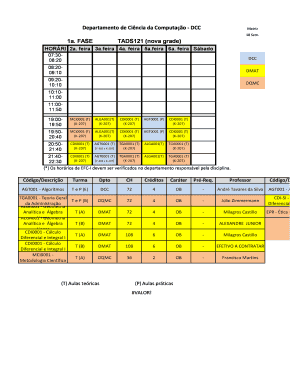
INFORMAL REQUEST FOR PROPOSAL No. DL169399P Identity and Access Management Assessment and Grouper Implementation PROPOSAL DUE DATE AND TIME: April 3, 2014 (3:00 PM, PT) OSU Procurement, Contracts
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign identity and access management

Edit your identity and access management form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your identity and access management form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit identity and access management online
To use our professional PDF editor, follow these steps:
1
Log in to account. Click on Start Free Trial and sign up a profile if you don't have one yet.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit identity and access management. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out identity and access management

How to fill out identity and access management:
01
Start by conducting a thorough assessment of your organization's needs and requirements regarding identity and access management (IAM). This includes identifying the types of users you have, the resources they need access to, and any regulatory or compliance requirements that must be considered.
02
Determine the appropriate IAM framework or solution that aligns with your organization's goals and objectives. This may involve evaluating various IAM systems or consulting with IAM providers to find the best fit for your needs.
03
Establish clear policies and guidelines for user access within your organization. This includes defining roles and responsibilities, setting up appropriate authorization levels, and implementing strong password policies to ensure the security of your systems.
04
Implement the chosen IAM solution and configure it according to your organization's requirements. This involves setting up user accounts, assigning appropriate access privileges, and integrating the IAM system with existing applications and systems.
05
Train your users and administrators on how to effectively use the IAM system. This includes educating them on the importance of maintaining strong passwords, regularly reviewing access privileges, and reporting any suspicious or unauthorized activities.
Who needs identity and access management:
01
Organizations of all sizes and industries can benefit from implementing identity and access management (IAM) systems.
02
Businesses that deal with sensitive customer data, intellectual property, or financial information require IAM to ensure proper user authentication and authorization, reducing the risk of data breaches and unauthorized access.
03
Government agencies and organizations that handle classified information or have stringent compliance requirements often rely on IAM solutions to ensure secure access to sensitive resources.
04
Healthcare providers and organizations that handle patient data must comply with strict regulations such as HIPAA, making IAM essential to safeguard patient information.
05
Educational institutions, with their diverse user base and need for secure access to various resources, can greatly benefit from IAM to manage user identities and control access to sensitive data.
In conclusion, anyone who values data security, wants to streamline user access management, and maintain regulatory compliance can benefit from implementing identity and access management systems.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is identity and access management?
Identity and access management (IAM) is a framework for business processes that facilitates the management of electronic or digital identities.
Who is required to file identity and access management?
Organizations or companies that have digital systems or networks and need to ensure secure access to their resources are required to file identity and access management.
How to fill out identity and access management?
To fill out identity and access management, organizations must assess their access control policies, define roles and permissions, and implement tools and processes for managing user identities and access.
What is the purpose of identity and access management?
The purpose of identity and access management is to ensure that only authorized individuals have access to resources, while also improving security, compliance, and efficiency.
What information must be reported on identity and access management?
Identity and access management reports typically include details on user profiles, access privileges, authentication methods, and activity logs.
How can I edit identity and access management from Google Drive?
By integrating pdfFiller with Google Docs, you can streamline your document workflows and produce fillable forms that can be stored directly in Google Drive. Using the connection, you will be able to create, change, and eSign documents, including identity and access management, all without having to leave Google Drive. Add pdfFiller's features to Google Drive and you'll be able to handle your documents more effectively from any device with an internet connection.
Can I create an electronic signature for signing my identity and access management in Gmail?
Upload, type, or draw a signature in Gmail with the help of pdfFiller’s add-on. pdfFiller enables you to eSign your identity and access management and other documents right in your inbox. Register your account in order to save signed documents and your personal signatures.
Can I edit identity and access management on an iOS device?
You certainly can. You can quickly edit, distribute, and sign identity and access management on your iOS device with the pdfFiller mobile app. Purchase it from the Apple Store and install it in seconds. The program is free, but in order to purchase a subscription or activate a free trial, you must first establish an account.
Fill out your identity and access management online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Identity And Access Management is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.