Get the free Checklist for HITECH Breach Readiness - ecfirst
Show details
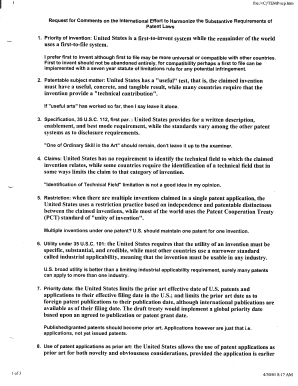
Checklist for HITCH Breach Readiness Checklist for HITCH Breach Readiness Checklist for HITCH Breach Readiness Figure 1 describes a checklist that may be used to assess for breach preparedness for
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign checklist for hitech breach

Edit your checklist for hitech breach form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your checklist for hitech breach form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing checklist for hitech breach online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit checklist for hitech breach. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, it's always easy to work with documents. Check it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out checklist for hitech breach

How to fill out checklist for hitech breach:
01
Determine the scope and impact of the breach: Assess the extent of the breach, including the affected systems, data, and potential risks.
02
Notify relevant parties: Inform key stakeholders such as management, legal teams, and IT departments about the breach.
03
Activate incident response plan: Follow the established protocol outlined in the incident response plan to handle the breach effectively.
04
Identify and isolate affected systems: Isolate the affected systems to prevent further damage and contain the breach.
05
Conduct forensic analysis: Investigate the breach to determine the cause, identify vulnerabilities, and gather evidence for potential legal actions.
06
Report the breach: Comply with legal and regulatory requirements by promptly reporting the breach to the appropriate authorities, such as government agencies or industry-specific organizations.
07
Notify affected individuals: Inform individuals whose personal information may have been compromised as a result of the breach, providing them with necessary guidance or support.
08
Implement mitigation measures: Take immediate steps to mitigate the impact of the breach, such as patching vulnerabilities, strengthening security controls, or implementing additional safeguards.
09
Assess and improve security measures: Evaluate existing security measures and policies to identify areas for improvement and enhance overall cybersecurity posture.
10
Learn from the incident: Perform a thorough post-incident analysis to identify lessons learned and adjust future breach response strategies accordingly.
Who needs checklist for hitech breach?
01
Organizations handling sensitive data: Any entity that deals with personal health information or electronic health records, such as healthcare providers, insurers, or business associates, should have a checklist for hitech breach.
02
IT and security teams: Checklists provide guidance to IT and security professionals responsible for maintaining the security of systems and data, enabling them to respond effectively in the event of a breach.
03
Compliance officers and legal teams: These professionals ensure that organizations adhere to relevant laws and regulations concerning data breaches, making checklists essential for ensuring compliance and appropriate breach response.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify checklist for hitech breach without leaving Google Drive?
It is possible to significantly enhance your document management and form preparation by combining pdfFiller with Google Docs. This will allow you to generate papers, amend them, and sign them straight from your Google Drive. Use the add-on to convert your checklist for hitech breach into a dynamic fillable form that can be managed and signed using any internet-connected device.
How can I get checklist for hitech breach?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific checklist for hitech breach and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
Can I create an electronic signature for the checklist for hitech breach in Chrome?
You certainly can. You get not just a feature-rich PDF editor and fillable form builder with pdfFiller, but also a robust e-signature solution that you can add right to your Chrome browser. You may use our addon to produce a legally enforceable eSignature by typing, sketching, or photographing your signature with your webcam. Choose your preferred method and eSign your checklist for hitech breach in minutes.
What is checklist for hitech breach?
The checklist for hitech breach is a tool used to ensure that all necessary steps are taken to address and report a breach of protected health information (PHI) in compliance with the Health Information Technology for Economic and Clinical Health (HITECH) Act.
Who is required to file checklist for hitech breach?
Covered entities and business associates are required to file the checklist for hitech breach in the event of a security breach involving PHI.
How to fill out checklist for hitech breach?
The checklist for hitech breach can be filled out by documenting the details of the breach, conducting a risk assessment, notifying affected individuals and the Department of Health and Human Services (HHS), and implementing remediation measures.
What is the purpose of checklist for hitech breach?
The purpose of the checklist for hitech breach is to ensure that breaches of PHI are properly handled, reported, and mitigated in accordance with HITECH regulations to protect individuals' sensitive health information.
What information must be reported on checklist for hitech breach?
The checklist for hitech breach should include details of the breach, steps taken to investigate the breach, risk assessment findings, notifications sent to individuals and HHS, and measures implemented to prevent future breaches.
Fill out your checklist for hitech breach online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Checklist For Hitech Breach is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.