Get the free Fragmentation and Encryption to Enforce
Show details
Fragmentation and Encryption to Enforce Privacy in Data Storage Valentina Ciriani1, Sabrina De Capitani di Vimercati1, Sara Foresti1, Sushi Jajodia2, Stefano Paraboschi3, and Pharyngeal Samarati1
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign fragmentation and encryption to
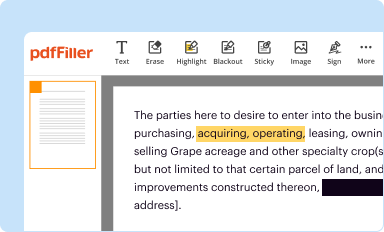
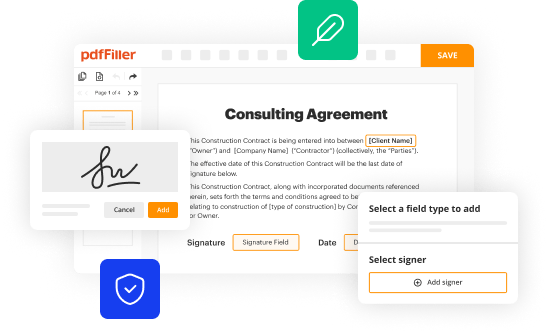
Edit your fragmentation and encryption to form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
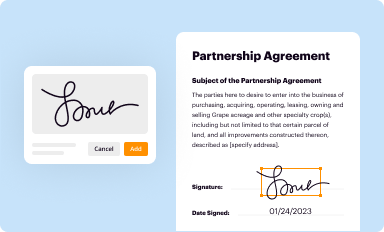
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your fragmentation and encryption to form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing fragmentation and encryption to online
Follow the guidelines below to use a professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit fragmentation and encryption to. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out fragmentation and encryption to
Fragmentation and encryption are important techniques used in the field of computer security. Here's a point-by-point guide on how to handle these practices and who can benefit from them:
How to Fill Out Fragmentation and Encryption:
Fragmentation: To fill out fragmentation, follow these steps:
01
Identify the data that needs to be fragmented. This could be a large file or message.
02
Determine the appropriate size for each fragment. This depends on the network or storage device's limitations.
03
Divide the data into equally sized fragments based on the determined size.
04
Assign a unique identifier to each fragment for easy reassembly.
05
Transmit or store the fragments accordingly, ensuring they reach the intended destination.
06
To reassemble the fragments, use the assigned identifiers to put the pieces back together.
Encryption: To fill out encryption, consider the following guidelines:
01
Choose a suitable encryption algorithm based on your security requirements. Common choices include AES, RSA, and DES.
02
Generate strong encryption keys that are hard to guess or crack.
03
Implement the encryption algorithm and apply it to the data you wish to protect.
04
Securely distribute the encryption keys to authorized parties.
05
Store the encrypted data or transmit it via secure channels to maintain confidentiality.
06
To decrypt the data, use the corresponding encryption key and apply the reverse process of the encryption algorithm.
Who Needs Fragmentation and Encryption:
01
Individuals: Individuals can benefit from fragmentation and encryption in various ways. For example:
1.1
Fragmentation can be useful when sending large files over email or uploading them on cloud storage platforms with file size limitations.
1.2
Encryption provides privacy and confidentiality for personal documents, sensitive information, and online communications.
02
Businesses: Fragmentation and encryption are crucial for organizations to ensure the security of their data. Consider the following scenarios:
2.1
Fragmentation can help optimize network traffic by dividing data into smaller packets, improving efficiency and reliability.
2.2
Encryption is vital when handling customers' personally identifiable information (PII), financial data, or trade secrets, safeguarding them from unauthorized access or data breaches.
03
Government Agencies: Fragmentation and encryption are essential for ensuring the security and integrity of sensitive government information. This includes protecting classified documents, secure communications, and confidential data stored or transmitted within government networks.
In summary, fragmentation and encryption play significant roles in enhancing data security. By following the proper procedures for filling out fragmentation and implementing encryption, individuals, businesses, and government agencies can protect their information from unauthorized access and maintain confidentiality.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send fragmentation and encryption to to be eSigned by others?
When your fragmentation and encryption to is finished, send it to recipients securely and gather eSignatures with pdfFiller. You may email, text, fax, mail, or notarize a PDF straight from your account. Create an account today to test it.
How can I get fragmentation and encryption to?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific fragmentation and encryption to and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
How do I fill out the fragmentation and encryption to form on my smartphone?
On your mobile device, use the pdfFiller mobile app to complete and sign fragmentation and encryption to. Visit our website (https://edit-pdf-ios-android.pdffiller.com/) to discover more about our mobile applications, the features you'll have access to, and how to get started.
What is fragmentation and encryption to?
Fragmentation is the process of breaking data into smaller pieces for transmission, while encryption is the method of converting data into a code to prevent unauthorized access.
Who is required to file fragmentation and encryption to?
Any organization or individual that handles sensitive data and wants to ensure its security.
How to fill out fragmentation and encryption to?
Fragmentation can be done using software or network protocols, and encryption can be implemented using encryption algorithms and keys.
What is the purpose of fragmentation and encryption to?
The purpose is to protect data during transmission and storage, ensuring confidentiality and integrity.
What information must be reported on fragmentation and encryption to?
Details of the data being fragmented, the encryption method used, and any key management processes.
Fill out your fragmentation and encryption to online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Fragmentation And Encryption To is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.