
Get the free Request for Device Encryption bExemptionb Form - Weill Cornell bb - its weill cornell
Show details
Request for Device Encryption Exemption Form ITS Incident Number: Request Date: Requestors Name: Requestors CID: Requestors Title: Requestors Division: Requestors Department: Department Administrator:
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign request for device encryption
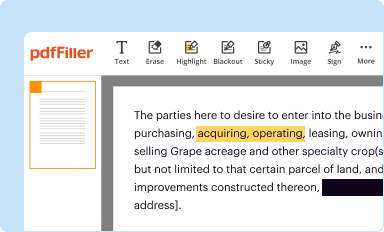
Edit your request for device encryption form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
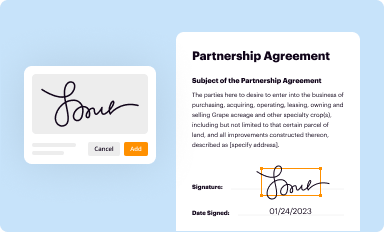
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
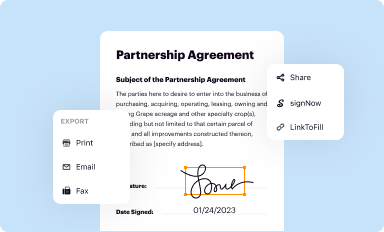
Share your form instantly
Email, fax, or share your request for device encryption form via URL. You can also download, print, or export forms to your preferred cloud storage service.
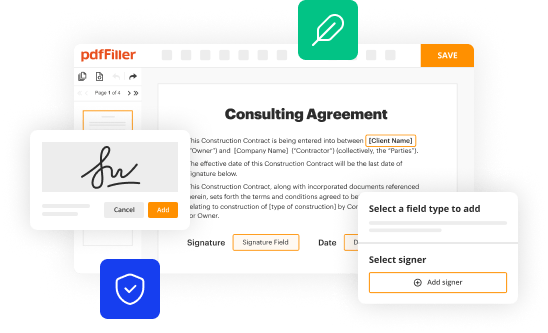
How to edit request for device encryption online
Follow the steps down below to use a professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit request for device encryption. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
It's easier to work with documents with pdfFiller than you could have believed. Sign up for a free account to view.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out request for device encryption
How to fill out a request for device encryption:
01
Start by downloading the request form for device encryption from your organization's IT department or security team.
02
Fill in your personal information, such as your full name, employee ID or student ID, and department or organization name. Make sure to provide accurate and up-to-date contact information.
03
Clearly state the reason why you are requesting device encryption. This could be due to the sensitivity of the data you handle, industry regulations, or organizational policies.
04
Identify the device(s) that require encryption. Include the make, model, and serial number of each device. If you are unsure, consult your IT department or refer to your organization's guidelines.
05
Indicate the type of encryption you would like to implement. This could be full disk encryption, file level encryption, or any other approved encryption method that aligns with your organization's security standards.
06
Provide a brief explanation of why you believe encryption is necessary for the specified device(s). This can include the potential risks associated with unauthorized access or loss of data.
07
If applicable, mention any additional security measures you have already taken to protect the device(s) and the data they contain.
08
Sign and date the request form to acknowledge that the information provided is accurate and complete.
Who needs a request for device encryption?
01
Organizations or institutions that handle sensitive information, such as healthcare providers, financial institutions, or government agencies, may require employees or members to submit a request for device encryption.
02
Individuals who work remotely or frequently handle sensitive data on their devices, even if they are not mandated to do so by their organization, may also opt to submit a request for device encryption as an added layer of protection.
03
Students or faculty members in educational institutions who handle confidential research data or personal information may be required or encouraged to request device encryption.
04
Any individual or organization concerned about the security and integrity of their data and the potential consequences of a data breach may choose to request device encryption as a proactive security measure.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify request for device encryption without leaving Google Drive?
You can quickly improve your document management and form preparation by integrating pdfFiller with Google Docs so that you can create, edit and sign documents directly from your Google Drive. The add-on enables you to transform your request for device encryption into a dynamic fillable form that you can manage and eSign from any internet-connected device.
Can I create an electronic signature for signing my request for device encryption in Gmail?
Create your eSignature using pdfFiller and then eSign your request for device encryption immediately from your email with pdfFiller's Gmail add-on. To keep your signatures and signed papers, you must create an account.
How do I edit request for device encryption on an Android device?
Yes, you can. With the pdfFiller mobile app for Android, you can edit, sign, and share request for device encryption on your mobile device from any location; only an internet connection is needed. Get the app and start to streamline your document workflow from anywhere.
What is request for device encryption?
Request for device encryption is a formal application to encrypt data on a device to protect it from unauthorized access.
Who is required to file request for device encryption?
Any individual or organization that wants to secure their device data is required to file a request for device encryption.
How to fill out request for device encryption?
To fill out a request for device encryption, one must provide necessary information such as device details, encryption method preference, and contact information.
What is the purpose of request for device encryption?
The purpose of request for device encryption is to enhance the security of data stored on a device and prevent unauthorized access.
What information must be reported on request for device encryption?
Information such as device details, encryption method preference, and contact information must be reported on request for device encryption.
Fill out your request for device encryption online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Request For Device Encryption is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.


















