Get the free RFP # 23246 – Information Technology Security Assessment ADDENDUM #1
Show details
This document serves as an addendum to the RFP for an Information Technology Security Assessment, providing corrections, responses to questions, and specifications for the assessment phases.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign rfp 23246 information technology

Edit your rfp 23246 information technology form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your rfp 23246 information technology form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit rfp 23246 information technology online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit rfp 23246 information technology. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
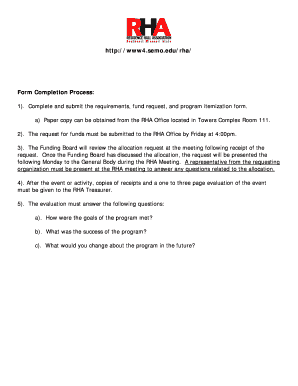
How to fill out rfp 23246 information technology

How to fill out RFP # 23246 – Information Technology Security Assessment ADDENDUM #1
01
Review the RFP document thoroughly to understand the scope and requirements.
02
Gather all necessary documentation and information required to respond.
03
Fill out the cover page with your company's information.
04
Address each section of the RFP, ensuring all questions are answered succinctly.
05
Include relevant experience and examples of previous work in information technology security.
06
Outline your proposed methodology for assessing security measures.
07
Provide a detailed timeline for project completion.
08
Include a budget breakdown with clear justification for costs.
09
Review the completed RFP for clarity, accuracy, and compliance with submission guidelines.
10
Submit the RFP by the specified deadline through the required submission method.
Who needs RFP # 23246 – Information Technology Security Assessment ADDENDUM #1?
01
Organizations or agencies seeking to evaluate their information technology security measures.
02
Companies looking to improve their cybersecurity posture.
03
Consultants and firms specializing in information technology security assessments.
Fill
form
: Try Risk Free






People Also Ask about
What is the RFP for cyber security assessment?
A Cybersecurity RFP is a document that outlines the requirements, expectations, and evaluation criteria for selecting a cybersecurity vendor. It serves as a roadmap for organizations to communicate their specific cybersecurity needs and find the most suitable vendor to address them.
What is included in a cybersecurity assessment?
A cybersecurity risk assessment evaluates the organization's vulnerabilities and threats to identify the risks it faces. It also includes recommendations for mitigating those risks. A risk estimation and evaluation are usually performed, followed by the selection of controls to treat the identified risks.
How to write a security assessment?
Completing a security assessment (and preparing a SAR) typically follows a 6-step process: Select a SAR template. Identify assets and current control systems. Identify potential threats to these assets. Compare potential threats to the control systems in place. Determine control recommendations.
What is RFP in cyber security?
A Cybersecurity RFP, or Request for Proposal, is a formal document that organizations use to outline their specific cybersecurity needs and invite vendors to submit proposals to meet those needs.
How to write a cyber security proposal?
Step-by-Step Guide to Writing a Cybersecurity Proposal Start with an Executive Summary. Define the Client's Security Challenges. Present Your Cybersecurity Solutions. Outline the Implementation Strategy. Discuss Costs and Budget. Highlight Your Team's Expertise. Include Case Studies and Testimonials.
What is an RFP in security?
A Security Assessment Request for Proposal (RFP) serves as a crucial document in the process of selecting a vendor to conduct a comprehensive security assessment for your organization.
What are the 5 steps to a cyber security risk assessment?
5-Step Risk Assessment Process Determine the Scope of the Risk Assessment. The first step is determining the cope of the risk assessment. Threat and Vulnerability Identification. Analyze Risks and Determine Potential Impact. Prioritize Risks. Document All Risks.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is RFP # 23246 – Information Technology Security Assessment ADDENDUM #1?
RFP # 23246 – Information Technology Security Assessment ADDENDUM #1 is an amendment to the original Request for Proposals that provides additional information, clarifications, or changes related to the IT security assessment project.
Who is required to file RFP # 23246 – Information Technology Security Assessment ADDENDUM #1?
Those vendors or organizations interested in submitting a bid or proposal for the Information Technology Security Assessment project are required to file RFP # 23246 – Information Technology Security Assessment ADDENDUM #1.
How to fill out RFP # 23246 – Information Technology Security Assessment ADDENDUM #1?
To fill out RFP # 23246 – Information Technology Security Assessment ADDENDUM #1, respondents should follow the instructions provided in the addendum, ensuring all required fields are completed accurately and all relevant information is included.
What is the purpose of RFP # 23246 – Information Technology Security Assessment ADDENDUM #1?
The purpose of RFP # 23246 – Information Technology Security Assessment ADDENDUM #1 is to enhance the clarity and completeness of the original RFP, ensuring that all potential respondents have the necessary information to prepare a compliant proposal.
What information must be reported on RFP # 23246 – Information Technology Security Assessment ADDENDUM #1?
The information that must be reported includes any updates, clarifications, or additional requirements specified in the addendum, as well as responses to the original RFP questions and any relevant documentation.
Fill out your rfp 23246 information technology online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Rfp 23246 Information Technology is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.