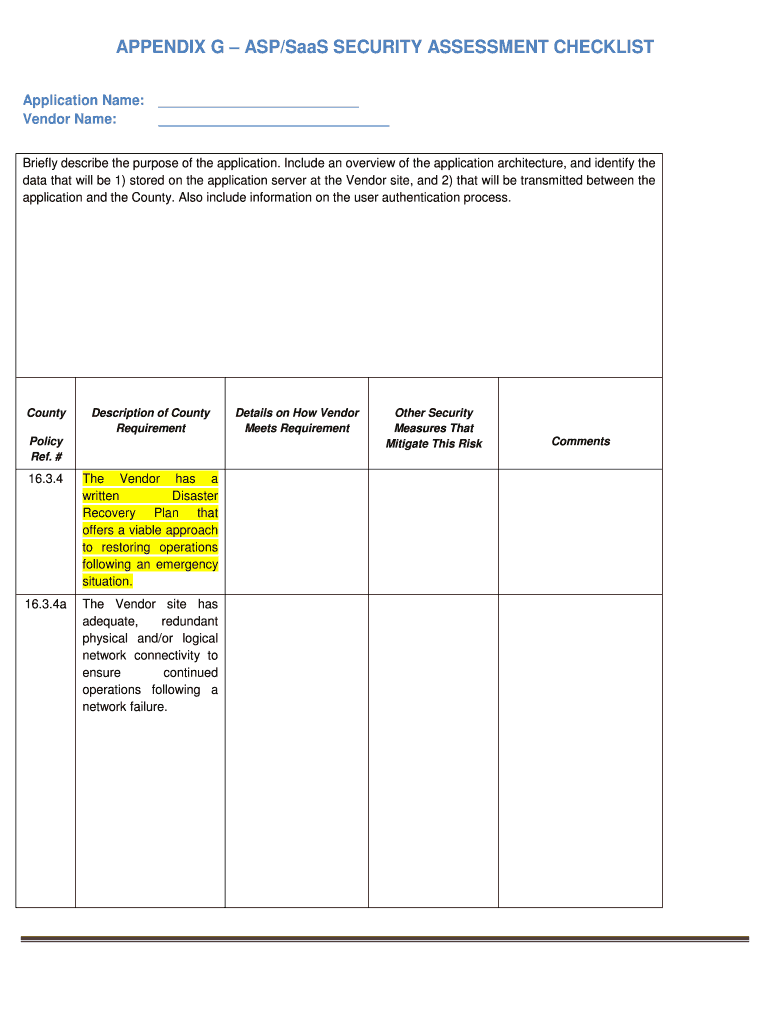
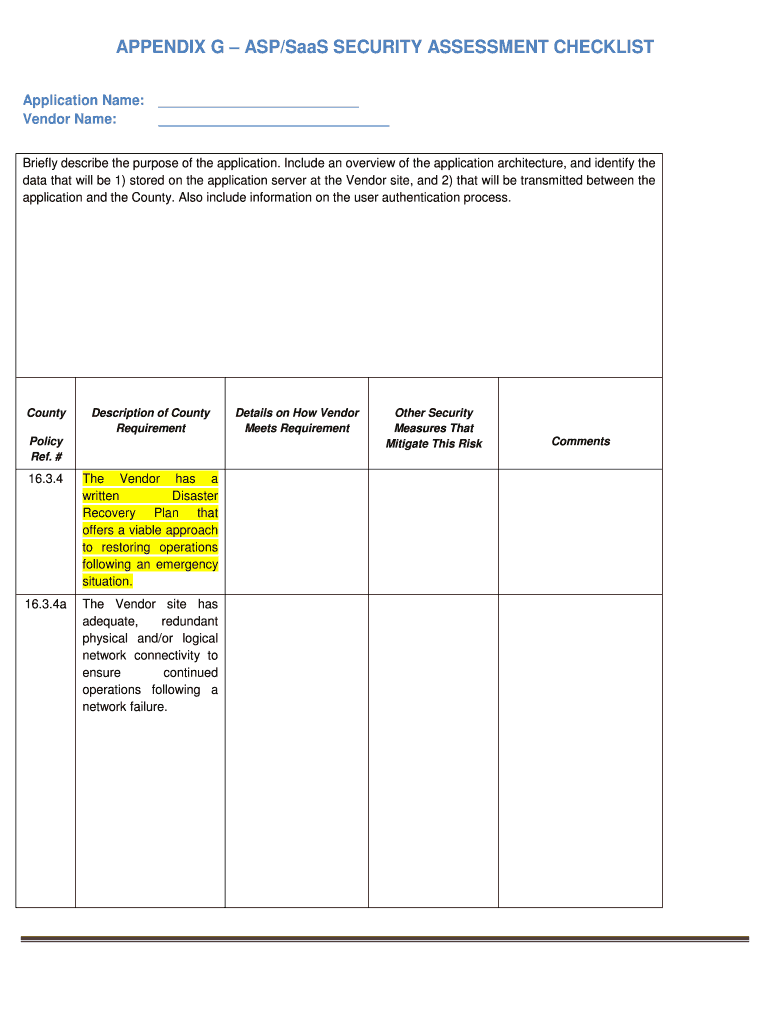
Get the free APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST
Show details
The document serves as a checklist to assess the security measures and disaster recovery plans of a vendor providing an ASP/SaaS application to the County, including policies regarding data protection,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign appendix g aspsaas security

Edit your appendix g aspsaas security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your appendix g aspsaas security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit appendix g aspsaas security online
To use the professional PDF editor, follow these steps below:
1
Check your account. It's time to start your free trial.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit appendix g aspsaas security. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out appendix g aspsaas security

How to fill out APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST
01
Begin by identifying the application or service being assessed.
02
Gather relevant documentation related to the application or service to ensure you have the necessary information.
03
Review each section of APPENDIX G carefully to understand what information is required.
04
For each item in the checklist, determine if the security controls are in place.
05
Provide evidence or documentation for each security control, as necessary.
06
Answer each question with a clear indication of compliance status (e.g., Yes, No, N/A).
07
Include any notes or comments that may provide additional context to your answers.
08
Once completed, review the checklist for accuracy and completeness.
09
Submit the checklist to the relevant stakeholders for review.
Who needs APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST?
01
Organizations that are evaluating or using ASP/SaaS solutions.
02
Security and compliance teams tasked with assessing the security of outsourced services.
03
Contract managers or procurement teams responsible for vendor assessments.
04
Auditors conducting compliance reviews for IT security practices.
Fill
form
: Try Risk Free






People Also Ask about
What are the 5 key security elements of the SaaS model?
What are the components of SaaS security? Data security. Identity and access management (IAM) Compliance. Threat detection and response. Configuration management. Secure integrations.
What is the SaaS security checklist NIST?
The NIST SaaS security checklist is a comprehensive framework for securing cloud-based software services. Key components include access control, data protection, vendor management, incident response & compliance considerations.
What are the 5 elements of security?
Five Pillars Of Information Assurance Framework The U.S. Department of Defense has promulgated the Five Pillars of Information Assurance model that includes the protection of confidentiality, integrity, availability, authenticity, and non-repudiation of user data.
How to assess SaaS security?
To conduct a SaaS security audit you must assess all areas of the platform, including employee security habits and compliance with industry best practices and standards. This can be done through the successful completion of a SaaS security evaluation.
What are the 5 key elements of a security policy?
The 5 Essential Elements of an Information Security Policy Purpose and Scope. Roles and Responsibilities. Information Classification and Control. Data Protection and Privacy. Incident Response and Management.
What is a SaaS questionnaire?
A SaaS questionnaire is a structured document designed to gather crucial information about a potential Software as a Service (SaaS) application. It acts as a vital tool for organizations to assess the suitability, functionality, and security posture of various SaaS solutions before making a critical decision.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST?
APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST is a document used to evaluate and assess the security measures and protocols implemented by Application Service Providers (ASPs) or Software as a Service (SaaS) providers to ensure data protection and compliance with security standards.
Who is required to file APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST?
Organizations that engage with ASP/SaaS providers for hosting or managing sensitive data are typically required to file APPENDIX G to ensure that their service providers meet necessary security standards.
How to fill out APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST?
To fill out APPENDIX G, an organization must gather information about the security practices of their ASP/SaaS provider, including policies, procedures, and compliance measures. Each section of the checklist should be answered based on the provider's current security posture.
What is the purpose of APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST?
The purpose of APPENDIX G is to provide a standardized approach to assessing the security capabilities of ASP/SaaS providers, enabling organizations to make informed decisions and ensure that their data is adequately protected.
What information must be reported on APPENDIX G – ASP/SaaS SECURITY ASSESSMENT CHECKLIST?
APPENDIX G requires reporting information regarding security policies, data encryption standards, access controls, incident response procedures, third-party audits, and compliance with regulatory requirements among other security measures.
Fill out your appendix g aspsaas security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Appendix G Aspsaas Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.