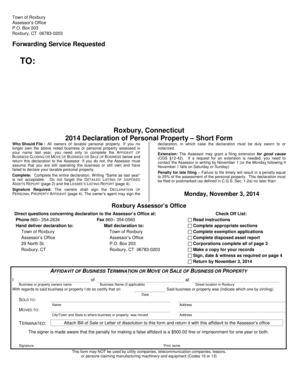
Get the free Security Threat Report Mid-year 2010 - Bitpipe
Show details
Security Threat Report: Midyear 2010 Contents Cybercrime. .......................................................................................................2. Cyberwar and cyberterrorism.....................................................................................4
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign security threat report mid-year

Edit your security threat report mid-year form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your security threat report mid-year form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit security threat report mid-year online
Use the instructions below to start using our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit security threat report mid-year. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out security threat report mid-year

How to fill out a security threat report mid-year:
01
Start by gathering all the relevant information: Before filling out the report, make sure you have all the necessary details about the security threats experienced during the mid-year. Collect any incident reports, logs, or testimonies related to the threats.
02
Provide a detailed description of each security threat: When filling out the report, include specific information about each threat, such as the date, time, location, and a thorough description of what occurred. This will help in accurately documenting the incidents.
03
Assess the impact and severity of each threat: Determine the level of impact caused by each security threat and classify it accordingly. Assign a severity rating based on the consequences, potential harm, and vulnerability.
04
Identify the potential causes and contributing factors: Investigate the root causes or contributing factors that led to the security threats. This may include system vulnerabilities, human error, lack of training, or external factors. Be as detailed as possible in your analysis.
05
Evaluate the existing security measures: Assess the effectiveness of the current security measures in place and whether they were adequate in preventing or mitigating the threats. Identify any gaps or weaknesses that need to be addressed.
06
Propose recommendations for improvement: Based on your analysis, propose actionable recommendations to enhance security measures and prevent future threats. These recommendations may include technology upgrades, policy changes, additional training, or increased security personnel.
Who needs a security threat report mid-year?
01
Organizations/businesses: Any organization or business that has experienced security threats during the mid-year should fill out a security threat report. This helps in documenting and analyzing the incidents, as well as developing strategies for prevention and response.
02
Security teams/IT departments: Security teams or IT departments within organizations are responsible for handling and addressing security threats. They need the mid-year security threat report to assess the situation, identify patterns or trends, and implement appropriate security measures.
03
Regulatory bodies/compliance agencies: Regulatory bodies or compliance agencies may require organizations to report security threats as part of compliance requirements. Providing the mid-year security threat report helps ensure that the organization is meeting its obligations and maintaining security standards.
Note: The specific individuals or departments within an organization who require the report may vary depending on the internal policies and procedures. It is essential to consult with relevant stakeholders to determine the appropriate recipients of the security threat report.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I make changes in security threat report mid-year?
pdfFiller not only allows you to edit the content of your files but fully rearrange them by changing the number and sequence of pages. Upload your security threat report mid-year to the editor and make any required adjustments in a couple of clicks. The editor enables you to blackout, type, and erase text in PDFs, add images, sticky notes and text boxes, and much more.
How do I edit security threat report mid-year straight from my smartphone?
You can easily do so with pdfFiller's apps for iOS and Android devices, which can be found at the Apple Store and the Google Play Store, respectively. You can use them to fill out PDFs. We have a website where you can get the app, but you can also get it there. When you install the app, log in, and start editing security threat report mid-year, you can start right away.
How do I fill out the security threat report mid-year form on my smartphone?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign security threat report mid-year and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
What is security threat report mid-year?
The security threat report mid-year is a report that provides an update on the current state of security threats within an organization or industry during the middle of the year.
Who is required to file security threat report mid-year?
Organizations that are at risk of security threats or are mandated by regulations to report on security threats are required to file the security threat report mid-year.
How to fill out security threat report mid-year?
The security threat report mid-year can be filled out by collecting relevant information on security incidents, vulnerabilities, and countermeasures taken by the organization, and reporting them in the designated format.
What is the purpose of security threat report mid-year?
The purpose of the security threat report mid-year is to provide stakeholders with an overview of the security landscape, raise awareness of potential threats, and enable proactive measures to mitigate risks.
What information must be reported on security threat report mid-year?
Information such as security incidents, vulnerabilities identified, remediation steps taken, security controls in place, and any new threats detected must be reported on the security threat report mid-year.
Fill out your security threat report mid-year online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Security Threat Report Mid-Year is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.