Get the free alt.computer.security: Excert from the Book
Show details
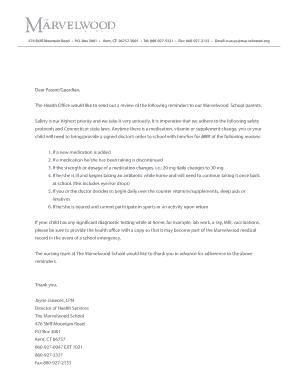
This document contains thank you letters from individuals and businesses acknowledging assistance in identifying and resolving computer security issues such as hacking and open ports.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign altcomputersecurity excert from form

Edit your altcomputersecurity excert from form form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your altcomputersecurity excert from form form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing altcomputersecurity excert from form online
To use our professional PDF editor, follow these steps:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit altcomputersecurity excert from form. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Now is the time to try it!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out altcomputersecurity excert from form

How to fill out alt.computer.security: Excert from the Book
01
Open your preferred newsreader application.
02
Subscribe to the alt.computer.security newsgroup.
03
Familiarize yourself with the newsgroup guidelines and etiquette.
04
Browse the existing threads and topics related to computer security.
05
If you have questions or need advice, create a new post with a clear subject line.
06
Include relevant details to help others understand your question.
07
Respond to others' posts respectfully and constructively.
Who needs alt.computer.security: Excert from the Book?
01
IT professionals seeking to enhance their knowledge of computer security.
02
Individuals interested in cybersecurity trends and best practices.
03
Students studying information technology or cybersecurity.
04
Hobbyists wanting to stay informed about the latest security threats.
05
Anyone looking for guidance on computer security issues.
Fill
form
: Try Risk Free






People Also Ask about
Which line from the book best supports his analysis of the code book?
The line that best supports Adam's analysis is option D: "The Trojan horse is a brand-new piece of encryption software that seems secure." This line includes specialized terms such as 'Trojan horse' and 'encryption software,' which are relevant to the themes of The Code Book.
What is the purpose of the quote from Zimmermann in the Code Book?
What is the purpose of the quote from Zimmermann? It shows how easily digital mail can be monitored by outsiders. It proves that e-mail is better for the health of democracy than regular mail.
What is the central idea in the code book is the concern?
A central idea in The Code Book is the concern that much of the world's information is not secure. Which lines from the passage best support this central idea? Check all that apply. One of the author's purposes in The Code Book is to explain different types of codebreaking to his readers.
What is the central idea of the code book?
A central idea in The Code Book is the concern that much of the world's information is not secure. Which lines from the passage best support this central idea? Check all that apply. Fortify is a verb that means "to protect and strengthen." A fortification is a that means "something that protects."
What is the purpose of the quote from Zimmerman?
What is the purpose of the quote from Zimmermann? It shows how easily digital mail can be monitored by outsiders. It proves that e-mail is better for the health of democracy than regular mail.
What is the central idea of this paragraph despite the enormous strength?
What is the central idea of this paragraph? Despite the enormous strength of RSA and other modern ciphers, cryptanalysts are still able to play a Many math experts work for the National Security valuable role in intelligence gathering. Their success is Agency.
Which reason best supports Zimmermann's claim in the Code Book?
Explanation. The reason that best supports Zimmermann's claim in The Code Book that "cryptography is about political power" is that governments use cryptography to protect classified information from being leaked to the public.
What is the Trojan horse another software trick?
"The Trojan horse, another software trick, involves Eve designing a program that appears to act like a genuine encryption product, but which actually betrays the user."
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is alt.computer.security: Excert from the Book?
alt.computer.security is a discussion forum focused on computer security topics, where participants share insights, ask questions, and discuss various security practices and issues.
Who is required to file alt.computer.security: Excert from the Book?
Individuals and organizations concerned with computer security, including IT professionals, cybersecurity experts, and anyone seeking to address security vulnerabilities are typically encouraged to engage in discussions relevant to alt.computer.security.
How to fill out alt.computer.security: Excert from the Book?
To participate in alt.computer.security, users should provide clear, concise posts related to security topics, follow community guidelines, and respect others' opinions while contributing their own knowledge.
What is the purpose of alt.computer.security: Excert from the Book?
The purpose of alt.computer.security is to facilitate the exchange of knowledge, experiences, and advice regarding computer security issues, enabling users to improve their understanding and practices in cybersecurity.
What information must be reported on alt.computer.security: Excert from the Book?
Users should report incidents, ask for help regarding specific security problems, share security updates and news, and discuss best practices in securing computer systems.
Fill out your altcomputersecurity excert from form online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Altcomputersecurity Excert From Form is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.