Get the free Ransomware Threat Demands
Show details
INSIDE THIS Issue Benet Customers! Scam Alert Ransomware Threat Demands PC Users Pay Or Elsewhere's a lot to love about February. It's the month of Valentine's Day with all those heart filled expressions
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign ransomware threat demands

Edit your ransomware threat demands form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your ransomware threat demands form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit ransomware threat demands online
Use the instructions below to start using our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit ransomware threat demands. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes working with documents easier than you could ever imagine. Try it for yourself by creating an account!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
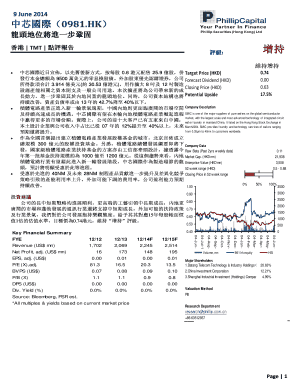
How to fill out ransomware threat demands

How to fill out ransomware threat demands?
01
Gather all the necessary information: Before filling out ransomware threat demands, it is important to gather all the necessary information. This includes understanding the specific demands made by the hackers and any instructions they have provided.
02
Evaluate the risks and consequences: Consider the potential risks and consequences of complying with the ransomware threat demands. It is important to weigh the potential damage that could occur if the demands are not met against the potential negative ramifications of giving in to the hackers' demands.
03
Communicate with law enforcement: It is crucial to involve law enforcement agencies when dealing with ransomware threat demands. They can help guide you through the process and potentially assist in tracking down the hackers responsible.
04
Consult with cybersecurity professionals: Seek advice from cybersecurity professionals who specialize in dealing with ransomware attacks. They can provide insights on best practices and strategies for addressing the threat demands.
05
Determine the best course of action: Based on the gathered information, the evaluated risks, and the advice from experts, determine the best course of action to address the ransomware threat demands. This may include deciding whether to pay the ransom, negotiate with the hackers, or pursue other alternatives.
Who needs ransomware threat demands?
01
Individuals and organizations victimized by ransomware attacks: Ransomware threat demands are primarily relevant to individuals and organizations that have fallen victim to ransomware attacks. These demands usually come from hackers who have encrypted the victim's data and demand payment in exchange for decrypting it.
02
Cybersecurity professionals and IT teams: Professionals working in cybersecurity and IT departments need to understand the nature of ransomware threat demands to devise effective countermeasures and strategies. They play an essential role in developing security protocols to prevent such attacks and responding promptly if they occur.
03
Law enforcement agencies: Ransomware threat demands also concern law enforcement agencies as they handle cases related to cybercrime and data breaches. They need to be aware of the tactics and trends used by cybercriminals to address the issue effectively and protect victims.
04
Government bodies and policymakers: Ransomware attacks and threat demands can have significant implications for governments and policymakers. They need to stay informed about the evolving nature of these threats to develop appropriate regulations, legislation, and response plans to protect citizens and critical infrastructure.
In conclusion, understanding how to fill out ransomware threat demands involves gathering information, evaluating risks, involving law enforcement and cybersecurity professionals, and determining the best course of action. These demands primarily concern individuals and organizations affected by ransomware attacks, cybersecurity professionals, law enforcement agencies, and government bodies.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
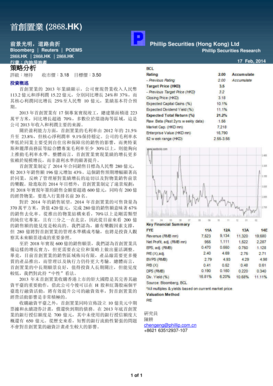
What is ransomware threat demands?
Ransomware threat demands are requests made by cybercriminals to pay a ransom in exchange for releasing encrypted data or systems.
Who is required to file ransomware threat demands?
Individuals or organizations who have been targeted by ransomware attacks are required to file ransomware threat demands.
How to fill out ransomware threat demands?
Ransomware threat demands can be filled out by providing detailed information about the attack, ransom amount demanded, and contact information for communication.
What is the purpose of ransomware threat demands?
The purpose of ransomware threat demands is to extort money from the victims in exchange for decrypting data or restoring access to systems.
What information must be reported on ransomware threat demands?
Information such as the date and time of the attack, method of infiltration, ransom amount demanded, and any communication received from the cybercriminals must be reported on ransomware threat demands.
Can I create an eSignature for the ransomware threat demands in Gmail?
You can easily create your eSignature with pdfFiller and then eSign your ransomware threat demands directly from your inbox with the help of pdfFiller’s add-on for Gmail. Please note that you must register for an account in order to save your signatures and signed documents.
Can I edit ransomware threat demands on an iOS device?
Use the pdfFiller app for iOS to make, edit, and share ransomware threat demands from your phone. Apple's store will have it up and running in no time. It's possible to get a free trial and choose a subscription plan that fits your needs.
How do I complete ransomware threat demands on an Android device?
Use the pdfFiller app for Android to finish your ransomware threat demands. The application lets you do all the things you need to do with documents, like add, edit, and remove text, sign, annotate, and more. There is nothing else you need except your smartphone and an internet connection to do this.
Fill out your ransomware threat demands online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Ransomware Threat Demands is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.