Get the free Information Assurance Checklist - Home Page 409th
Show details
Information Assurance Checklist Name: Date: System Authorization Access Request DoD IA Awareness Training and Exam ACTS User Account Acceptable Use Policy (AUP) Thumb Drive Awareness3 Safe Home Computing3
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign information assurance checklist

Edit your information assurance checklist form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your information assurance checklist form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing information assurance checklist online
Follow the steps down below to benefit from the PDF editor's expertise:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit information assurance checklist. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
It's easier to work with documents with pdfFiller than you can have believed. Sign up for a free account to view.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out information assurance checklist

How to fill out an information assurance checklist:
01
Gather all relevant information: Before starting to fill out the checklist, make sure you have all the necessary information and documentation at hand. This may include security policies, risk assessments, system details, and any other relevant documentation.
02
Review the checklist: Familiarize yourself with the format and structure of the information assurance checklist. Understand the different sections, categories, and questions that need to be addressed. This will help you navigate through the checklist more efficiently.
03
Complete each section: Start filling out the checklist by addressing each section one by one. Provide accurate and detailed information for each requirement or question. If a particular section does not apply to your specific situation, indicate that it is not applicable or provide a brief explanation.
04
Consult with relevant experts: If you encounter any uncertainties or have questions while filling out the checklist, reach out to the appropriate experts or personnel within your organization. They can provide guidance and clarification on specific requirements or areas that may be complex.
05
Double-check for accuracy: Once you have completed the checklist, review your responses to ensure accuracy and completeness. Check for any inconsistencies or errors that may require correction. It is crucial to provide accurate information to ensure the efficiency and effectiveness of the information assurance process.
06
Submit the checklist: After confirming the accuracy of your responses, submit the completed checklist to the designated authority or department responsible for information assurance. Follow any instructions or procedures provided for submission.
Who needs an information assurance checklist?
01
Organizations handling sensitive data: Any organization that deals with sensitive or confidential data, such as financial institutions, healthcare providers, government agencies, or businesses with proprietary information, can benefit from an information assurance checklist. This checklist helps ensure that proper security measures are in place to protect valuable data from unauthorized access, breaches, or misuse.
02
IT and cybersecurity professionals: Information assurance checklists are particularly relevant for IT and cybersecurity professionals responsible for managing and securing information systems. These professionals can use the checklist as a comprehensive guide to identify potential vulnerabilities or weaknesses in their systems and implement appropriate safeguards.
03
Regulatory compliance requirements: Depending on the industry and geographical location, certain regulatory frameworks and standards may mandate organizations to maintain information assurance checklists. Compliance with these requirements enables organizations to adhere to legal and industry-specific regulations, ensuring data privacy, security, and integrity.
In conclusion, filling out an information assurance checklist involves gathering information, reviewing the checklist, completing each section accurately, consulting with experts when needed, double-checking for accuracy, and submitting the checklist. The checklist is necessary for organizations handling sensitive data, IT professionals, and those complying with regulatory requirements.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify information assurance checklist without leaving Google Drive?
By combining pdfFiller with Google Docs, you can generate fillable forms directly in Google Drive. No need to leave Google Drive to make edits or sign documents, including information assurance checklist. Use pdfFiller's features in Google Drive to handle documents on any internet-connected device.
How can I send information assurance checklist to be eSigned by others?
To distribute your information assurance checklist, simply send it to others and receive the eSigned document back instantly. Post or email a PDF that you've notarized online. Doing so requires never leaving your account.
How do I make changes in information assurance checklist?
pdfFiller not only allows you to edit the content of your files but fully rearrange them by changing the number and sequence of pages. Upload your information assurance checklist to the editor and make any required adjustments in a couple of clicks. The editor enables you to blackout, type, and erase text in PDFs, add images, sticky notes and text boxes, and much more.
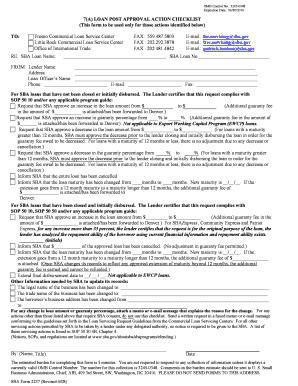
What is information assurance checklist?
The information assurance checklist is a document that outlines security measures and procedures to ensure the confidentiality, integrity, and availability of information.
Who is required to file information assurance checklist?
Organizations and individuals who handle sensitive information are required to file an information assurance checklist.
How to fill out information assurance checklist?
The information assurance checklist can be filled out by documenting security controls, policies, and procedures that are in place to protect information.
What is the purpose of information assurance checklist?
The purpose of the information assurance checklist is to ensure that proper security measures are in place to protect sensitive information from unauthorized access or disclosure.
What information must be reported on information assurance checklist?
The information assurance checklist must include details of security controls, risk assessments, incident response plans, and training programs.
Fill out your information assurance checklist online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Information Assurance Checklist is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.