
Get the free Email Privacy & Security The Origin of Sayings - Chadwick Financial ...
Show details
Email Privacy & Security The Origin of Sayings Email is a wonderful way to communicate for many of us if not most of us Many of the things we say commonly and take for granted have a unique today.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign email privacy amp security
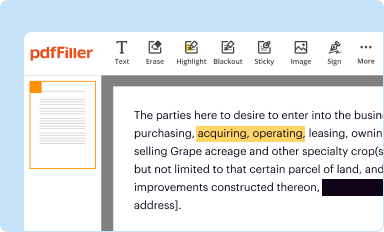
Edit your email privacy amp security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
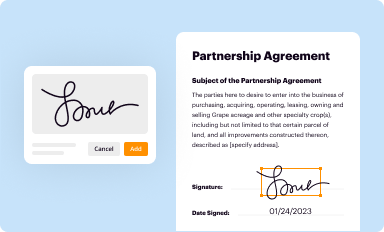
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
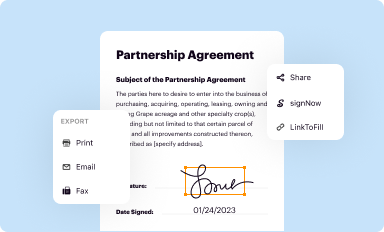
Share your form instantly
Email, fax, or share your email privacy amp security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
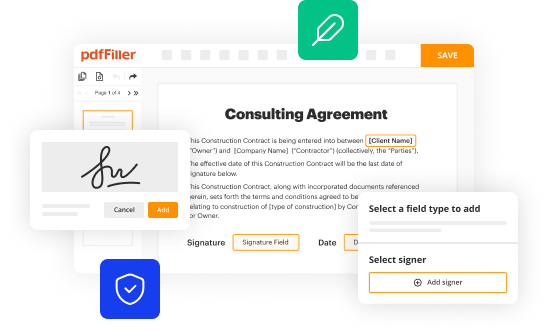
How to edit email privacy amp security online
Use the instructions below to start using our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit email privacy amp security. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out email privacy amp security
Point by point guide to filling out email privacy amp security:
01
Create a strong and unique password: Choose a password that is at least eight characters long and includes a combination of uppercase and lowercase letters, numbers, and special characters. Avoid using easily guessable information like your name or birthdate.
02
Enable two-factor authentication: Set up an additional layer of security by enabling two-factor authentication. This requires you to provide a second form of verification, such as a unique code sent to your mobile device, to access your email account.
03
Keep your software up to date: Regularly update your email software to ensure that you have the latest security patches and protection against vulnerabilities. Enable automatic updates if possible for seamless security enhancements.
04
Be cautious with attachments and links: Avoid opening email attachments or clicking on suspicious links from unknown senders. They could contain malware or phishing attempts, compromising your privacy and security.
05
Use encryption for sensitive information: If you are transmitting sensitive information through emails, consider using encryption methods like HTTPS or PGP to protect the content. This adds an extra layer of security and prevents unauthorized access.
06
Be mindful of where you access your emails: Avoid accessing your emails from public or unsecured Wi-Fi networks, as they can be vulnerable to hackers. Use a trusted and secure network when accessing your emails to protect your privacy.
07
Regularly review your privacy settings: Check and adjust your email privacy settings to ensure that you are comfortable with the level of information you are sharing. Set strict privacy options to limit data collection and sharing by the email provider.
08
Train yourself to identify phishing and scam emails: Educate yourself about common signs of phishing emails, such as spelling and grammatical errors, unusual requests for personal information, or suspicious sender addresses. Be cautious and report any suspicious emails to protect yourself and others.
09
Delete unnecessary emails and backup important ones: Regularly delete unnecessary emails to reduce the chances of a data breach. Additionally, make sure to back up important emails and attachments in a separate and secure location to prevent loss or accidental deletion.
10
Educate yourself and stay informed: Continuously educate yourself about the latest email privacy and security practices. Stay informed about new threats and techniques used by hackers to protect yourself effectively.
Who needs email privacy amp security?
01
Individuals: Anyone who uses email for personal communication should prioritize email privacy and security. Protecting personal information, preventing identity theft, and maintaining confidentiality are crucial for individuals.
02
Businesses: Businesses send and receive sensitive information through emails, including customer data, financial records, and proprietary information. Implementing strong security measures is essential to protect this valuable information from unauthorized access or data breaches.
03
Government entities: Government organizations handle a vast amount of confidential information that must be securely transmitted via email. Ensuring email privacy and security is critical to maintain national security and protect sensitive data from falling into the wrong hands.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send email privacy amp security to be eSigned by others?
To distribute your email privacy amp security, simply send it to others and receive the eSigned document back instantly. Post or email a PDF that you've notarized online. Doing so requires never leaving your account.
Where do I find email privacy amp security?
The premium pdfFiller subscription gives you access to over 25M fillable templates that you can download, fill out, print, and sign. The library has state-specific email privacy amp security and other forms. Find the template you need and change it using powerful tools.
Can I edit email privacy amp security on an iOS device?
You can. Using the pdfFiller iOS app, you can edit, distribute, and sign email privacy amp security. Install it in seconds at the Apple Store. The app is free, but you must register to buy a subscription or start a free trial.
What is email privacy amp security?
Email privacy and security refers to safeguarding the confidentiality and integrity of email communications, as well as protecting against unauthorized access and cyber threats.
Who is required to file email privacy amp security?
Any organization or individual that collects, processes, or stores email data is required to ensure email privacy and security.
How to fill out email privacy amp security?
To fill out email privacy and security requirements, organizations need to implement encryption, access controls, regular security audits, and employee training programs.
What is the purpose of email privacy amp security?
The purpose of email privacy and security is to protect sensitive information, maintain trust with customers, comply with regulations, and mitigate the risk of data breaches.
What information must be reported on email privacy amp security?
Organizations must report on their email encryption practices, security protocols, incident response procedures, and data protection measures.
Fill out your email privacy amp security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Email Privacy Amp Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















