Get the free Benefits and Security Vulnerabilities of Contactless Card Payment Systems
Show details
1×7/12Benefits and Security Vulnerabilities of Contactless Card Payment SystemsIssue #12 December 2011inform. Educate. Connect. EmailShareThisBenefits and Security Vulnerabilities of Contactless
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign benefits and security vulnerabilities
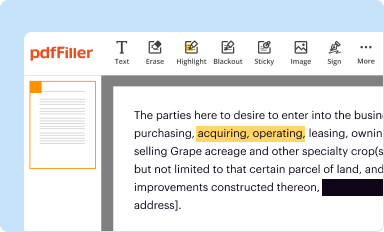
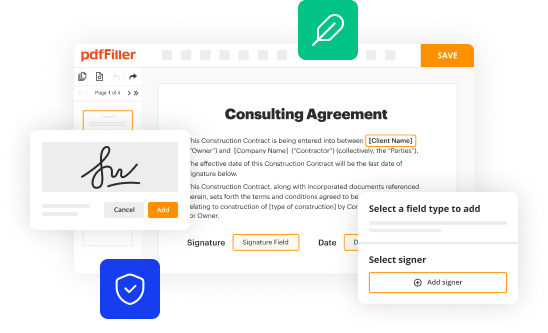
Edit your benefits and security vulnerabilities form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
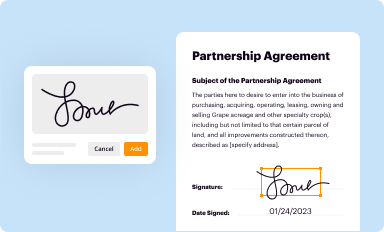
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
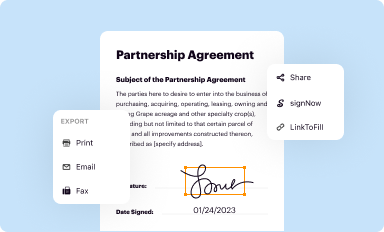
Share your form instantly
Email, fax, or share your benefits and security vulnerabilities form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing benefits and security vulnerabilities online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit benefits and security vulnerabilities. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes working with documents easier than you could ever imagine. Create an account to find out for yourself how it works!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out benefits and security vulnerabilities
How to fill out benefits and security vulnerabilities:
01
Start by conducting a thorough assessment of your organization's benefits and security vulnerabilities. This can involve reviewing existing policies, procedures, and systems, as well as identifying potential gaps or areas of improvement.
02
Identify the specific benefits that your organization offers to employees or stakeholders. These could include health insurance, retirement plans, paid time off, or other perks. Make sure to gather all relevant information and documentation related to each benefit.
03
Assess the security vulnerabilities within your organization. This may involve evaluating your IT infrastructure, data storage systems, and network security. Look for potential weaknesses and areas that may be prone to security breaches or unauthorized access.
04
Analyze the potential risks associated with each security vulnerability. This could include data breaches, financial losses, reputation damage, or legal implications. Identify the level of risk for each vulnerability and prioritize them based on their potential impact on your organization.
05
Develop a strategic plan to address and mitigate these vulnerabilities. This could involve implementing robust security measures such as firewalls, encryption software, employee training on cybersecurity best practices, and regular system updates. Additionally, establish protocols and procedures to ensure prompt response to any potential security incidents.
06
Regularly monitor and update your benefits and security vulnerabilities. As technology evolves and new risks emerge, it is crucial to stay up-to-date with the latest trends and best practices in both areas. Conduct periodic reviews and assessments to identify any new vulnerabilities or changes in benefits that may be required.
Who needs benefits and security vulnerabilities?
01
Organizations of all sizes and industries can benefit from having a comprehensive benefits package for their employees. Providing benefits helps attract and retain talent, boost employee morale and productivity, and comply with legal requirements. Therefore, any organization that values their workforce and wants to create a positive work environment should consider offering benefits.
02
Similarly, all organizations, regardless of their size or industry, need to address their security vulnerabilities. Cyberattacks and data breaches are becoming increasingly common and can have severe consequences for businesses, including financial losses, reputational damage, and legal liabilities. Prioritizing security measures and regularly assessing vulnerabilities is essential for protecting sensitive data, maintaining business continuity, and safeguarding the organization's reputation.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my benefits and security vulnerabilities in Gmail?
You may use pdfFiller's Gmail add-on to change, fill out, and eSign your benefits and security vulnerabilities as well as other documents directly in your inbox by using the pdfFiller add-on for Gmail. pdfFiller for Gmail may be found on the Google Workspace Marketplace. Use the time you would have spent dealing with your papers and eSignatures for more vital tasks instead.
Where do I find benefits and security vulnerabilities?
With pdfFiller, an all-in-one online tool for professional document management, it's easy to fill out documents. Over 25 million fillable forms are available on our website, and you can find the benefits and security vulnerabilities in a matter of seconds. Open it right away and start making it your own with help from advanced editing tools.
How do I fill out the benefits and security vulnerabilities form on my smartphone?
You can quickly make and fill out legal forms with the help of the pdfFiller app on your phone. Complete and sign benefits and security vulnerabilities and other documents on your mobile device using the application. If you want to learn more about how the PDF editor works, go to pdfFiller.com.
What is benefits and security vulnerabilities?
Benefits and security vulnerabilities refer to the advantages and weaknesses of a system or program in terms of protecting sensitive information and preventing unauthorized access.
Who is required to file benefits and security vulnerabilities?
Anyone responsible for managing or overseeing the security of a system or program, such as IT professionals or security analysts, may be required to report on benefits and security vulnerabilities.
How to fill out benefits and security vulnerabilities?
To fill out benefits and security vulnerabilities, one must assess the strengths and weaknesses of the system or program in terms of security measures, potential threats, and vulnerabilities.
What is the purpose of benefits and security vulnerabilities?
The purpose of benefits and security vulnerabilities is to identify areas of strength and weakness in a system or program's security measures, allowing for proactive measures to improve overall security.
What information must be reported on benefits and security vulnerabilities?
Information such as identified vulnerabilities, security measures in place, potential risks, and recommendations for improvements must be reported on benefits and security vulnerabilities.
Fill out your benefits and security vulnerabilities online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Benefits And Security Vulnerabilities is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.