Get the free Art of InfoJacking
Show details
This document contains a presentation on detecting and testing web network devices with a focus on vulnerabilities, HTTP cloaking, information gathering techniques, and the effectiveness of security
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign art of infojacking
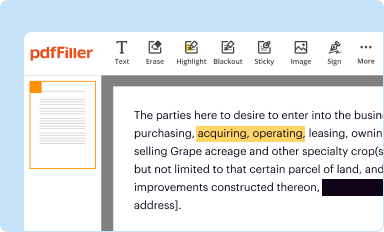
Edit your art of infojacking form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
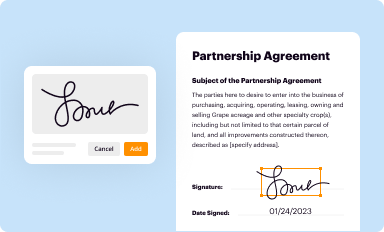
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
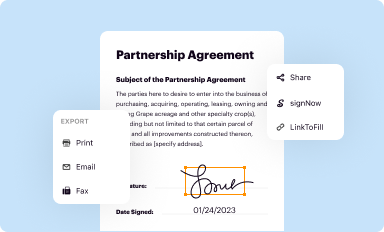
Share your form instantly
Email, fax, or share your art of infojacking form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit art of infojacking online
In order to make advantage of the professional PDF editor, follow these steps below:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
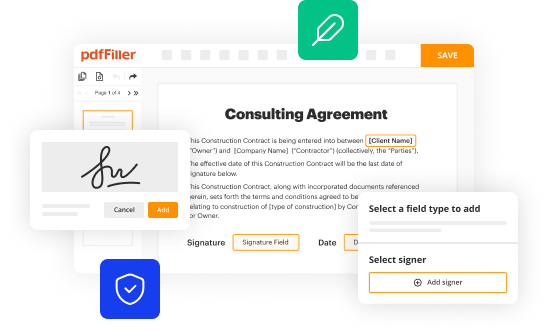
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit art of infojacking. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Try it now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out art of infojacking
How to fill out Art of InfoJacking
01
Identify the target audience for your InfoJacking.
02
Research trending topics and relevant information in your niche.
03
Create an engaging headline that captures attention.
04
Use a content format that best suits the information, such as articles, videos, or infographics.
05
Integrate high-quality sources and data to support your claims.
06
Optimize your content for SEO to increase visibility.
07
Share your content on relevant platforms and social media channels.
08
Monitor engagement and feedback to refine future InfoJacking efforts.
Who needs Art of InfoJacking?
01
Digital marketers looking to boost their content strategy.
02
Content creators aiming to attract more audience engagement.
03
Businesses wanting to leverage current trends for promotion.
04
Bloggers seeking innovative ways to repurpose existing information.
05
Influencers looking to align with trending topics in their niche.
Fill
form
: Try Risk Free






People Also Ask about
What is the meaning of deceptive art?
Deceptive art, as described in the Purana, involves cunning techniques that create delusions among beings. In the Theravada tradition, Deceptive art refers to the illusions or temptations that can divert individuals from their spiritual journey.
What is the main idea of deception?
Deception can be defined broadly as the manipulation of appearances such that they convey a false reality.
What is the meaning of the art of deception?
The Art of Deception is about gaining someone's trust by lying to them and then abusing that trust for fun and profit. Hackers use the euphemism "social engineering" and hacker-guru Kevin Mitnick examines many example scenarios.
What is the deep meaning of deception?
Deception is the act of convincing of one or many recipients of untrue information. The person creating the deception knows it to be false while the receiver of the information does not. It is often done for personal gain or advantage.
What is the art of writing called in English?
calligraphy, the art of beautiful handwriting.
What is the meaning of art of deception?
The Art of Deception is about gaining someone's trust by lying to them and then abusing that trust for fun and profit. Hackers use the euphemism "social engineering" and hacker-guru Kevin Mitnick examines many example scenarios.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Art of InfoJacking?
Art of InfoJacking refers to the strategic gathering and utilization of publicly available information to achieve specific advantages or outcomes, typically in a business or competitive context.
Who is required to file Art of InfoJacking?
Individuals or organizations engaged in competitive analysis, market research, or data mining activities may be required to file Art of InfoJacking, particularly if it involves regulated information.
How to fill out Art of InfoJacking?
To fill out Art of InfoJacking, you should collect necessary information, categorize it appropriately, and complete any required forms or documents, ensuring compliance with relevant guidelines.
What is the purpose of Art of InfoJacking?
The purpose of Art of InfoJacking is to leverage available information for informed decision-making, competitive advantage, and enhancing strategic planning in various sectors.
What information must be reported on Art of InfoJacking?
Information that must be reported typically includes the source of the information, the context of its use, and any compliance with legal or ethical standards relevant to the data.
Fill out your art of infojacking online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Art Of Infojacking is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.