
Get the free Static Application Security Testing Market in the APAC Region 2010 ...
Show details
Static Application Security Testing Market in the APAC Region 2010-2014 Phone: +44 20 8123 2220 Fax: +44 207 900 3970 office marketpublishers.com http://marketpublishers.com Phone: +44 20 8123 2220
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign static application security testing
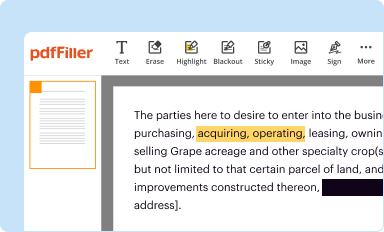
Edit your static application security testing form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
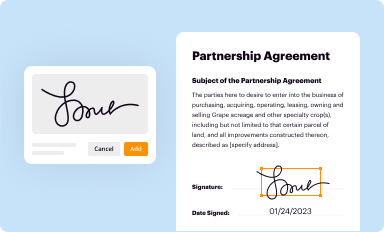
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
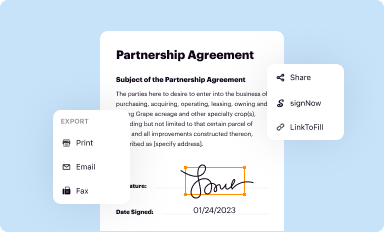
Share your form instantly
Email, fax, or share your static application security testing form via URL. You can also download, print, or export forms to your preferred cloud storage service.
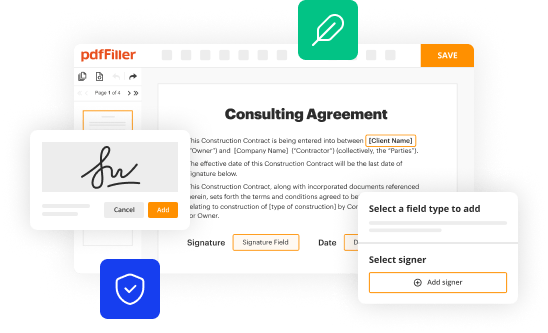
Editing static application security testing online
To use the professional PDF editor, follow these steps below:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit static application security testing. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
pdfFiller makes working with documents easier than you could ever imagine. Try it for yourself by creating an account!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out static application security testing
How to fill out static application security testing:
01
Research and select a static application security testing (SAST) tool that best fits your needs. There are various tools available in the market, such as Veracode, Checkmarx, Fortify, and many more. Consider factors like the programming languages supported, ease of use, and reporting capabilities.
02
Install and set up the SAST tool on your development environment. Follow the instructions provided by the tool vendor to install the necessary dependencies and configure any required settings. This may include integrating the tool with your code repository, build systems, or IDEs.
03
Understand the scope of your application. Identify the codebases and applications that you want to test using the SAST tool. This may include web applications, mobile applications, APIs, or any other software that requires security testing.
04
Configure the SAST tool to scan the identified codebases. Define the scan settings based on your requirements, such as the programming languages used, specific rules or vulnerabilities to focus on, and scan depth. This ensures that the tool performs an accurate and targeted analysis of your application's code.
05
Start the SAST scan and wait for it to complete. The scanning process may take some time depending on the size and complexity of your codebase. Utilize any progress indicators or status updates provided by the tool to monitor the scan's progress.
06
Analyze the scan results generated by the SAST tool. Review the identified vulnerabilities, code flaws, and security weaknesses. Categorize the findings based on their severity level, and prioritize them for remediation. Consult with your development team or security experts to better understand the impact and potential risks associated with each finding.
07
Take necessary actions to address the identified vulnerabilities. This may involve fixing the code directly, implementing security best practices, using secure coding libraries, or seeking assistance from external resources. Aim to remediate the vulnerabilities in a timely manner to reduce the risk of exploitation.
08
Re-scan the codebase after implementing the fixes and improvements. This step ensures that the vulnerabilities have been successfully addressed and that no new vulnerabilities have been introduced. Validate that the SAST tool reports a reduced number of findings or ideally, zero vulnerabilities.
Who needs static application security testing?
01
Organizations and businesses that develop software applications need static application security testing (SAST) to ensure the security and integrity of their codebase. It is particularly crucial for industries dealing with sensitive data, such as finance, healthcare, government, and e-commerce.
02
Developers and development teams can benefit from SAST as it helps identify potential vulnerabilities and code flaws during the development process itself. By incorporating SAST into their workflow, developers can proactively address security concerns and adopt secure coding practices.
03
Security professionals responsible for application security in an organization can leverage SAST to assess the overall security posture of their applications. SAST provides insights into potential security weaknesses and helps prioritize remediation efforts based on the severity and impact of the identified vulnerabilities.
04
Compliance and audit teams can utilize SAST to ensure that applications meet the required security standards and regulatory requirements. By conducting regular SAST scans, organizations can demonstrate their commitment to security and compliance to auditors, regulatory bodies, and customers.
05
Third-party security vendors or consultants may also offer SAST services to organizations that lack the in-house expertise or resources to perform comprehensive security testing. These vendors can perform SAST scans, analyze the results, and provide recommendations for improving the security of the application.
In conclusion, static application security testing is crucial for organizations, developers, security professionals, compliance teams, and third-party vendors who want to ensure the security and integrity of their software applications. By following the step-by-step process outlined above, you can effectively fill out static application security testing and mitigate potential security risks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit static application security testing from Google Drive?
By integrating pdfFiller with Google Docs, you can streamline your document workflows and produce fillable forms that can be stored directly in Google Drive. Using the connection, you will be able to create, change, and eSign documents, including static application security testing, all without having to leave Google Drive. Add pdfFiller's features to Google Drive and you'll be able to handle your documents more effectively from any device with an internet connection.
How can I send static application security testing for eSignature?
When you're ready to share your static application security testing, you can swiftly email it to others and receive the eSigned document back. You may send your PDF through email, fax, text message, or USPS mail, or you can notarize it online. All of this may be done without ever leaving your account.
How do I fill out static application security testing using my mobile device?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign static application security testing and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
What is static application security testing?
Static Application Security Testing (SAST) is a type of security testing that analyzes the source code or the binary of an application to identify potential security vulnerabilities or weaknesses.
Who is required to file static application security testing?
The requirement to file static application security testing may vary depending on the specific regulations or industry standards applicable. Generally, organizations or developers responsible for developing and deploying software applications should perform and document static application security testing.
How to fill out static application security testing?
Filling out static application security testing involves the following steps:
1. Identify the target application to be tested.
2. Select a suitable static application security testing tool.
3. Configure the tool with necessary settings and parameters.
4. Run the security testing tool against the application's source code or binary.
5. Analyze the generated security report and identify potential vulnerabilities.
6. Document the findings and implement necessary remediation measures.
What is the purpose of static application security testing?
The purpose of static application security testing is to identify security vulnerabilities or weaknesses in software applications at an early stage of development. By conducting static application security testing, organizations can identify and address potential security flaws before deployment, reducing the risk of cyber attacks and data breaches.
What information must be reported on static application security testing?
The specific information to be reported on static application security testing may vary depending on the organization's requirements and relevant regulations. Generally, the report should include details about the tested application, identified vulnerabilities, severity levels, recommendations for remediation, and any other relevant findings.
Fill out your static application security testing online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Static Application Security Testing is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















