
Get the free What is spoofing - akronlibrary
Show details
Computer Security Windows XP Privacy Issues We use computers for everything from banking and investing to shopping and communicating with others through email or chat programs. Although you may not
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign what is spoofing
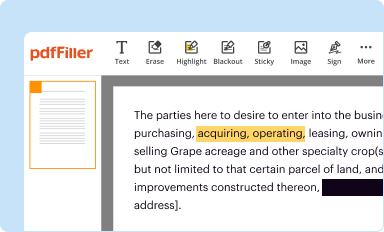
Edit your what is spoofing form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
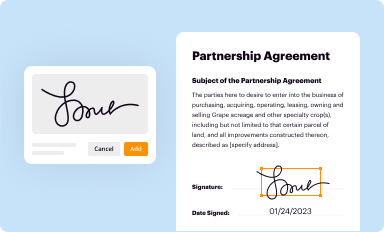
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
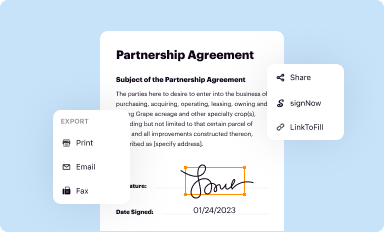
Share your form instantly
Email, fax, or share your what is spoofing form via URL. You can also download, print, or export forms to your preferred cloud storage service.
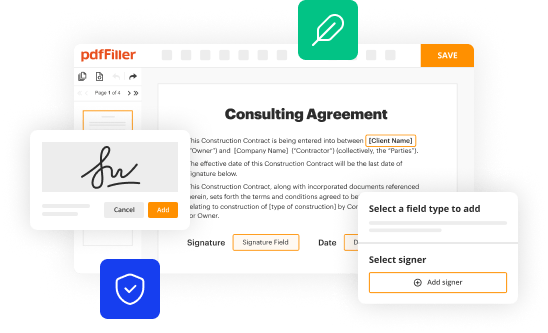
Editing what is spoofing online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit what is spoofing. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
The use of pdfFiller makes dealing with documents straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out what is spoofing
To understand what spoofing is and who needs this knowledge, you can follow the following points:
How to fill out what is spoofing:
01
Start by researching the concept of spoofing, which refers to the act of falsifying information or a false identity to deceive others.
02
Understand the different types of spoofing, such as IP spoofing, email spoofing, or caller ID spoofing, and how they can be used in unauthorized activities or cyber attacks.
03
Learn about the various techniques employed in spoofing, including DNS spoofing, ARP spoofing, or website spoofing, and the potential risks they pose to individuals and organizations.
04
Familiarize yourself with the precautions and preventive measures against spoofing, such as using strong authentication methods, implementing secure network protocols, and being cautious of suspicious emails or websites.
Who needs what is spoofing:
01
IT professionals and network administrators should understand spoofing to enhance network security and develop effective countermeasures against spoofing attacks.
02
Individuals who use online services or engage in online transactions can benefit from knowing about spoofing to protect their personal information and avoid falling victim to scams or fraudulent activities.
03
Cybersecurity experts, including ethical hackers and penetration testers, need to grasp the concepts of spoofing to identify vulnerabilities, conduct security assessments, and propose remediation strategies.
04
Businesses and organizations should educate their employees about spoofing to promote a strong security culture and prevent potential data breaches or unauthorized access to their systems.
In summary, learning about spoofing and its various aspects is essential for IT professionals, individuals using online services, cybersecurity experts, and businesses aiming to maintain robust security measures.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit what is spoofing in Chrome?
what is spoofing can be edited, filled out, and signed with the pdfFiller Google Chrome Extension. You can open the editor right from a Google search page with just one click. Fillable documents can be done on any web-connected device without leaving Chrome.
How do I edit what is spoofing straight from my smartphone?
The easiest way to edit documents on a mobile device is using pdfFiller’s mobile-native apps for iOS and Android. You can download those from the Apple Store and Google Play, respectively. You can learn more about the apps here. Install and log in to the application to start editing what is spoofing.
How do I fill out what is spoofing using my mobile device?
You can quickly make and fill out legal forms with the help of the pdfFiller app on your phone. Complete and sign what is spoofing and other documents on your mobile device using the application. If you want to learn more about how the PDF editor works, go to pdfFiller.com.
What is spoofing?
Spoofing is a fraudulent practice where an individual or a computer program disguises their identity or manipulates data in order to deceive others or gain unauthorized access to information.
Who is required to file what is spoofing?
There is no specific requirement to file what is spoofing as it is not a document or form that needs to be filed.
How to fill out what is spoofing?
Since what is spoofing is not a document or form, there is no process to fill it out.
What is the purpose of what is spoofing?
The purpose of spoofing can vary, but it is often used to deceive individuals or systems for personal gain or to gain unauthorized access to sensitive information.
What information must be reported on what is spoofing?
As mentioned earlier, there is no information that needs to be reported on what is spoofing as it is not a document or form.
Fill out your what is spoofing online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

What Is Spoofing is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















