
Get the free multi layered threat monitoring form - airccse
Show details
International Journal on Cloud Computing: Services and Architecture (ICCA), Vol. 1, No. 1, May 2011 A MULTI-LAYER REAL TIME REMOTE MONITORING & CORPORATE NETWORK SYSTEM FOR VIRULENT THREATS Majid
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign multi layered threat monitoring
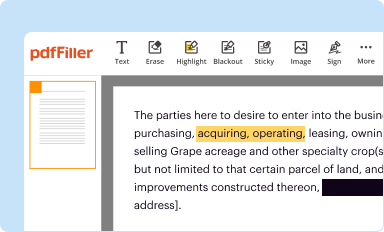
Edit your multi layered threat monitoring form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
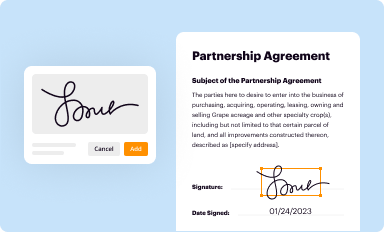
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your multi layered threat monitoring form via URL. You can also download, print, or export forms to your preferred cloud storage service.
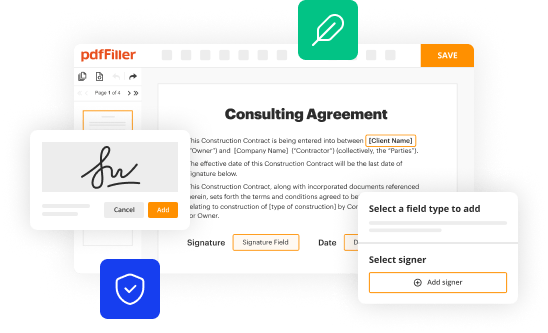
Editing multi layered threat monitoring online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit multi layered threat monitoring. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, it's always easy to work with documents. Try it!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out multi layered threat monitoring
How to fill out multi layered threat monitoring:
01
Identify the different layers of your organization's threat monitoring system. This may include network security, application security, device security, data security, and personnel security.
02
Evaluate the current security measures in place for each layer. Determine if there are any gaps or vulnerabilities that need to be addressed.
03
Research and select appropriate security solutions for each layer of the threat monitoring system. This may involve investing in tools such as firewalls, antivirus software, intrusion detection systems, encryption software, and security awareness training for employees.
04
Implement the selected security solutions and configure them correctly to ensure they effectively monitor and protect each layer of the organization's infrastructure.
05
Regularly review and update the security measures in place as new threats and vulnerabilities emerge. Stay informed about the latest security best practices and technologies to ensure the organization's threat monitoring system remains effective.
Who needs multi layered threat monitoring:
01
Organizations of all sizes and industries need multi layered threat monitoring. This includes companies in sectors such as finance, healthcare, technology, and government, as well as small businesses and non-profit organizations.
02
Organizations that handle sensitive or valuable data, such as customer information, intellectual property, or financial records, have a greater need for multi layered threat monitoring. This is because they are more likely to be targeted by cybercriminals seeking to steal or exploit that data.
03
Compliance regulations and industry standards may require certain organizations to implement multi layered threat monitoring. For example, companies in the healthcare industry may need to comply with the Health Insurance Portability and Accountability Act (HIPAA), which mandates certain security measures to protect patient data.
In conclusion, any organization that wants to protect its infrastructure and data from cyber threats should consider implementing multi layered threat monitoring. This involves identifying the different layers of threat monitoring, evaluating and selecting appropriate security solutions, implementing and configuring them correctly, and regularly reviewing and updating the security measures in place.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my multi layered threat monitoring in Gmail?
It's easy to use pdfFiller's Gmail add-on to make and edit your multi layered threat monitoring and any other documents you get right in your email. You can also eSign them. Take a look at the Google Workspace Marketplace and get pdfFiller for Gmail. Get rid of the time-consuming steps and easily manage your documents and eSignatures with the help of an app.
How can I send multi layered threat monitoring to be eSigned by others?
Once your multi layered threat monitoring is complete, you can securely share it with recipients and gather eSignatures with pdfFiller in just a few clicks. You may transmit a PDF by email, text message, fax, USPS mail, or online notarization directly from your account. Make an account right now and give it a go.
How do I edit multi layered threat monitoring on an Android device?
You can make any changes to PDF files, like multi layered threat monitoring, with the help of the pdfFiller Android app. Edit, sign, and send documents right from your phone or tablet. You can use the app to make document management easier wherever you are.
What is multi layered threat monitoring?
Multi layered threat monitoring is a security approach that involves utilizing multiple layers of defense systems to detect and mitigate potential threats and attacks on a network or system.
Who is required to file multi layered threat monitoring?
There is no specific requirement for filing multi layered threat monitoring as it is more of a security practice than a filing requirement.
How to fill out multi layered threat monitoring?
Multi layered threat monitoring cannot be filled out as it is a security practice rather than a form or document.
What is the purpose of multi layered threat monitoring?
The purpose of multi layered threat monitoring is to enhance the security of networks and systems by implementing multiple layers of defense mechanisms to detect and prevent threats and attacks.
What information must be reported on multi layered threat monitoring?
There is no specific information that needs to be reported on multi layered threat monitoring as it is not a reporting requirement.
Fill out your multi layered threat monitoring online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Multi Layered Threat Monitoring is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















