Get the free Japan Information Technology Security Evaluation and Certification Scheme - commoncr...
Show details
This document provides information regarding the certification details of the EUR Form Client software, including its security evaluation and certification status.
We are not affiliated with any brand or entity on this form
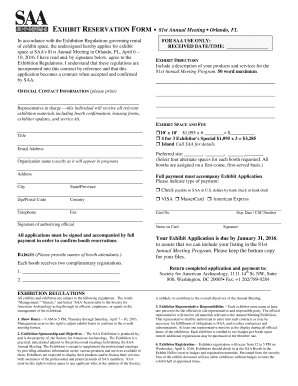
Get, Create, Make and Sign japan information technology security

Edit your japan information technology security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your japan information technology security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing japan information technology security online
Follow the steps down below to use a professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit japan information technology security. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
It's easier to work with documents with pdfFiller than you could have believed. You may try it out for yourself by signing up for an account.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out japan information technology security

How to fill out Japan Information Technology Security Evaluation and Certification Scheme
01
Gather all necessary documents related to your IT systems and security protocols.
02
Review the requirements outlined by the Japan Information Technology Security Evaluation and Certification Scheme (JISEC).
03
Conduct a self-assessment to identify any gaps in your current security measures.
04
Implement necessary security controls and measures to meet the JISEC criteria.
05
Prepare the required documentation showcasing your security practices, policies, and procedures.
06
Apply for the evaluation by submitting your documentation to an accredited evaluation body for JISEC.
07
Collaborate with evaluators during the assessment process, providing additional information as needed.
08
Address any findings or issues identified during the evaluation process.
09
Upon successful evaluation, receive the certification and ensure ongoing compliance with JISEC standards.
Who needs Japan Information Technology Security Evaluation and Certification Scheme?
01
Organizations operating in or doing business with Japan that handle information technology systems.
02
Companies seeking to demonstrate compliance with high security standards in IT.
03
Firms looking to enhance their trust and credibility in the Japanese market.
04
Government agencies and contractors that require certification for cybersecurity standards.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Japan Information Technology Security Evaluation and Certification Scheme?
The Japan Information Technology Security Evaluation and Certification Scheme (JISEC) is a framework designed to evaluate and certify the security of information technology products and systems in Japan. It aims to ensure that these products meet specific security standards and criteria.
Who is required to file Japan Information Technology Security Evaluation and Certification Scheme?
Organizations that develop, manufacture, or distribute information technology products, as well as service providers offering IT solutions, may be required to file under the JISEC. This includes both domestic and foreign entities that wish to market their products in Japan.
How to fill out Japan Information Technology Security Evaluation and Certification Scheme?
To fill out the JISEC application, organizations must complete a detailed form that includes information about the product, its design and functionality, security measures in place, and compliance with relevant standards. They may also need to provide evidence of testing and evaluation results.
What is the purpose of Japan Information Technology Security Evaluation and Certification Scheme?
The purpose of the JISEC is to enhance the information security of IT products and systems, promote trust in their use, and align with global security standards. It aims to protect against security risks and ensure the integrity and confidentiality of user data.
What information must be reported on Japan Information Technology Security Evaluation and Certification Scheme?
The information that must be reported includes product specifications, security features, risk assessment results, compliance with security criteria, and any vulnerabilities identified during the evaluation process. Organizations may also need to submit documentation supporting their claims of security.
Fill out your japan information technology security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Japan Information Technology Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.