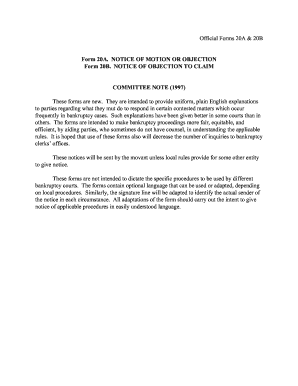
Get the free How To PRoTEcT youR aDulT chilDREn - Senior News
Show details
The Senior News Focus for People Aged 50 and Better! VOLUME 28 ISSUE 9 SEPTEMBER 2014 the power of positive thinking how to protect your adult children Dads Priceless estate MARS IS POPULATED BY ROBOTS!
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign how to protect your

Edit your how to protect your form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your how to protect your form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit how to protect your online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit how to protect your. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Try it now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out how to protect your

How to fill out "how to protect your"?
01
Research: Start by gathering information on what exactly you need to protect and what potential threats or risks it may face. This could include personal information, digital assets, physical property, or financial resources. Understanding the specific areas of vulnerability will help you create a comprehensive protection plan.
02
Assess Risks: Once you have identified the areas that need protection, analyze the risks associated with each. Evaluate the probability and potential impact of different threats to prioritize your protective measures effectively. This step ensures that you allocate your resources wisely and focus on the most critical aspects.
03
Develop a plan: Create a detailed plan that outlines the protective measures you will employ for each identified risk. This plan should include both preventive strategies and reactive measures to ensure comprehensive protection. For example, you might consider installing security systems, creating strong passwords and encryption methods, practicing safe online behavior, and establishing regular backups for data.
04
Implement precautions: Put your plan into action by implementing the protective measures you have outlined. This could involve installing security software, setting up physical barriers, updating privacy settings, or training employees on security protocols. It is crucial to consistently apply and enforce these precautions to maintain sufficient protection.
05
Monitor and adapt: Protection is an ongoing process. Regularly monitor the effectiveness of your protective measures and update them as needed. Stay informed about emerging threats and potential vulnerabilities, as the landscape of risks continuously evolves. Regular maintenance and adaptation are essential to ensure the adequacy of your protection efforts.
Who needs "how to protect your"?
01
Individuals: Everyone, from individuals who want to safeguard their personal information and digital identities to those aiming to protect their physical assets, can benefit from learning how to protect themselves. Online privacy, home security, and personal safety are concerns for people of all backgrounds.
02
Businesses: Protecting sensitive customer data, intellectual property, and financial information is crucial for businesses of all sizes and industries. Implementing effective security measures can help prevent data breaches, cyberattacks, and theft, ensuring business continuity and mitigating potential legal and financial repercussions.
03
Organizations: Non-profit organizations, government agencies, educational institutions, and other entities often handle large amounts of sensitive data and have a responsibility to protect it. Safeguarding employee and customer information, as well as maintaining the confidentiality of critical data, is essential to maintain the trust and reputation of such organizations.
In summary, learning how to fill out and implement a comprehensive protection plan is essential for individuals, businesses, and organizations across various sectors to safeguard their assets, data, and identities from potential threats and risks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I get how to protect your?
It’s easy with pdfFiller, a comprehensive online solution for professional document management. Access our extensive library of online forms (over 25M fillable forms are available) and locate the how to protect your in a matter of seconds. Open it right away and start customizing it using advanced editing features.
Can I create an electronic signature for the how to protect your in Chrome?
Yes. By adding the solution to your Chrome browser, you can use pdfFiller to eSign documents and enjoy all of the features of the PDF editor in one place. Use the extension to create a legally-binding eSignature by drawing it, typing it, or uploading a picture of your handwritten signature. Whatever you choose, you will be able to eSign your how to protect your in seconds.
How do I fill out how to protect your using my mobile device?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign how to protect your and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
What is how to protect your?
How to protect your refers to taking necessary steps to ensure the safety and security of your personal information and belongings.
Who is required to file how to protect your?
Everyone is responsible for protecting their personal information and belongings.
How to fill out how to protect your?
You can fill out how to protect your by implementing password protection, using encryption, and being cautious with sharing personal information.
What is the purpose of how to protect your?
The purpose of how to protect your is to prevent identity theft, fraud, and unauthorized access to your personal information.
What information must be reported on how to protect your?
You must report your personal identification information, financial information, and any sensitive data.
Fill out your how to protect your online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

How To Protect Your is not the form you're looking for?Search for another form here.
Relevant keywords
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.