Get the free Hazard Identification and Vulnerability Analysis - Thurston County - co thurston wa
Show details
Thurston County Emergency Management Phone 360 754 3360 2703 Pacific Avenue SE, Suite B Fax 360 704 2775 Olympia, WA 98501-2036 Hazard Identification and Vulnerability Analysis February 2004 EXECUTIVE
We are not affiliated with any brand or entity on this form
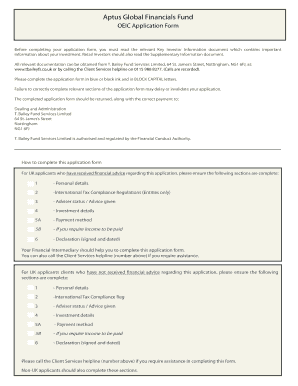
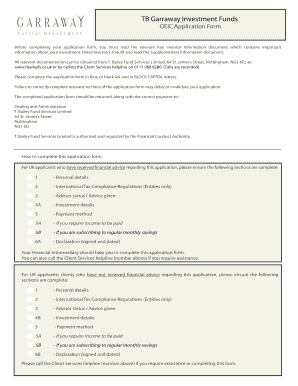
Get, Create, Make and Sign hazard identification and vulnerability

Edit your hazard identification and vulnerability form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your hazard identification and vulnerability form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing hazard identification and vulnerability online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit hazard identification and vulnerability. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out hazard identification and vulnerability

How to fill out hazard identification and vulnerability:
01
Start by conducting a thorough inventory and assessment of potential hazards in your environment. This may include natural disasters like earthquakes, floods, or wildfires, as well as human-made hazards such as chemical spills or terrorist attacks.
02
Identify the specific vulnerabilities in your organization or community that make you more susceptible to these hazards. Consider factors such as geographical location, infrastructure, population density, and the presence of critical facilities or resources.
03
Analyze the potential consequences of each identified hazard and vulnerability combination. This involves assessing the impact on people, the economy, the environment, and essential services or infrastructure.
04
Prioritize the hazards and vulnerabilities based on their likelihood and potential severity. This will help determine where to allocate resources and develop mitigation strategies.
05
Develop strategies and mitigation measures to minimize the impact of identified hazards and vulnerabilities. This may include implementing engineering controls, emergency response plans, public education campaigns, or investments in resiliency measures.
06
Regularly review and update the hazard identification and vulnerability assessment as new information or changes in the environment occur. This ensures that your organization or community remains prepared and resilient to emerging threats.
Who needs hazard identification and vulnerability:
01
Emergency managers: Hazard identification and vulnerability assessments are crucial tools for emergency managers who are responsible for planning, preparing, and responding to potential disasters or emergencies. These assessments help them understand the risks in their jurisdiction and develop effective response plans.
02
Government agencies: Local, state, and federal government agencies use hazard identification and vulnerability assessments to inform policy decisions, allocate resources, and implement preventative measures. It enables them to prioritize their efforts and better protect the communities they serve.
03
Businesses and organizations: Private businesses and organizations conduct hazard identification and vulnerability assessments to safeguard their employees, customers, and assets. It helps them identify potential risks and implement measures to reduce vulnerabilities, ensuring business continuity and minimizing potential losses.
04
Community members: Individuals and households can benefit from understanding the hazards and vulnerabilities present in their area. This knowledge allows them to make informed decisions about their safety, take necessary precautions, and support community-wide preparedness efforts.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is hazard identification and vulnerability?
Hazard identification and vulnerability is the process of identifying potential hazards and assessing the vulnerability of a system or organization to those hazards.
Who is required to file hazard identification and vulnerability?
The requirement to file hazard identification and vulnerability can vary depending on the jurisdiction and industry. It is typically the responsibility of the organization or entity that is subject to regulations or standards related to hazard identification and vulnerability.
How to fill out hazard identification and vulnerability?
Filling out hazard identification and vulnerability typically involves conducting risk assessments, collecting relevant data and information, and documenting the findings. It may also involve implementing mitigation measures and developing emergency response plans.
What is the purpose of hazard identification and vulnerability?
The purpose of hazard identification and vulnerability is to assess and manage risks, enhance preparedness, and minimize the potential impact of hazards on individuals, systems, and organizations.
What information must be reported on hazard identification and vulnerability?
The specific information required for hazard identification and vulnerability reporting can vary, but it often includes details about identified hazards, vulnerability assessments, risk mitigation strategies, and emergency response plans.
How can I send hazard identification and vulnerability for eSignature?
Once your hazard identification and vulnerability is ready, you can securely share it with recipients and collect eSignatures in a few clicks with pdfFiller. You can send a PDF by email, text message, fax, USPS mail, or notarize it online - right from your account. Create an account now and try it yourself.
How do I edit hazard identification and vulnerability straight from my smartphone?
The pdfFiller mobile applications for iOS and Android are the easiest way to edit documents on the go. You may get them from the Apple Store and Google Play. More info about the applications here. Install and log in to edit hazard identification and vulnerability.
How do I edit hazard identification and vulnerability on an Android device?
With the pdfFiller mobile app for Android, you may make modifications to PDF files such as hazard identification and vulnerability. Documents may be edited, signed, and sent directly from your mobile device. Install the app and you'll be able to manage your documents from anywhere.
Fill out your hazard identification and vulnerability online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Hazard Identification And Vulnerability is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.