
Get the free Information IT Risk Assessment and Management - isaca
Show details
This document provides information about an ISACA Pittsburgh Chapter luncheon focused on IT Risk Assessment and Management, including event details, program highlights, presenters, registration information,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign information it risk assessment
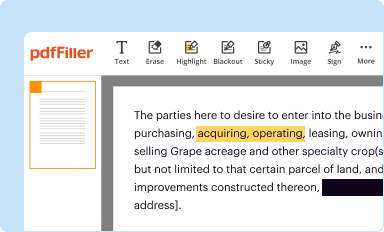
Edit your information it risk assessment form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
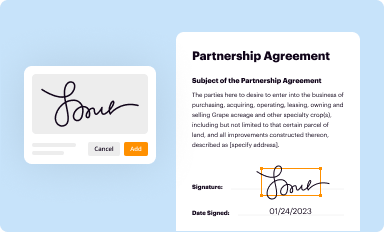
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
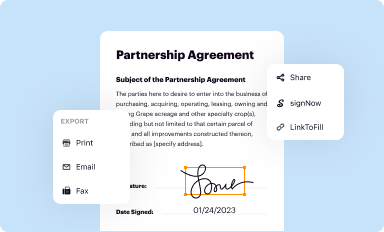
Share your form instantly
Email, fax, or share your information it risk assessment form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit information it risk assessment online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in to account. Click on Start Free Trial and register a profile if you don't have one.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit information it risk assessment. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out information it risk assessment
How to fill out information IT risk assessment:
01
Identify the scope and objectives of the risk assessment: Determine what areas and systems will be included in the assessment and establish clear objectives for identifying and mitigating IT risks.
02
Gather information: Collect all relevant data and documentation related to the IT systems, processes, and controls being assessed. This may include network diagrams, system configurations, security policies, incident reports, and previous risk assessments.
03
Identify and assess risks: Analyze the collected information to identify potential vulnerabilities, threats, and risks to the IT environment. This can be done through interviews, workshops, reviewing documentation, and using risk assessment frameworks and methodologies.
04
Assess likelihood and impact: Evaluate the likelihood and potential impact of each identified risk. Consider factors such as the probability of occurrence, potential business impact, and existing controls or safeguards in place.
05
Define risk tolerance: Determine acceptable levels of risk for the organization. This involves considering factors such as regulatory requirements, strategic objectives, and the organization's risk appetite.
06
Mitigate risks: Develop and implement risk treatments or mitigation strategies to reduce the identified risks to an acceptable level. These strategies may include implementing additional security controls, improving existing controls, transferring or accepting the risk, or avoiding the risk altogether.
07
Document findings: Record the assessment findings, including identified risks, their likelihood and impact ratings, and the recommended mitigation actions. This documentation should be clear, concise, and easily understandable by all stakeholders.
08
Review and update: Regularly review and update the IT risk assessment to ensure it remains current and reflective of the evolving IT environment. Risks can change due to new technologies, threats, or changes in business operations.
Who needs information IT risk assessment?
Information IT risk assessments are crucial for various stakeholders within an organization. These include:
01
IT Managers and Technicians: IT professionals need an IT risk assessment to understand the potential vulnerabilities and risks associated with the organization's IT systems. This allows them to implement appropriate safeguards and controls to mitigate these risks.
02
Management and Executives: Senior management and executives require IT risk assessments to make informed decisions about resource allocation, budgeting, and strategic planning. Understanding the organization's IT risks helps them prioritize investments, allocate resources, and establish risk management policies.
03
Auditors and Compliance Officers: Internal and external auditors and compliance officers rely on IT risk assessments to evaluate the effectiveness of the organization's IT controls and ensure compliance with regulatory requirements. These assessments help identify any deficiencies or weaknesses in controls that need to be addressed.
04
Stakeholders and Business Partners: Information IT risk assessments can provide reassurance to stakeholders, such as customers, suppliers, and business partners, that the organization is actively managing its IT risks. This helps build trust and confidence in the organization's ability to protect sensitive information and maintain operational continuity.
In summary, filling out an information IT risk assessment involves identifying, assessing, and mitigating risks related to an organization's IT systems. This process is essential for IT professionals, management, auditors, and stakeholders to effectively manage and mitigate IT risks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
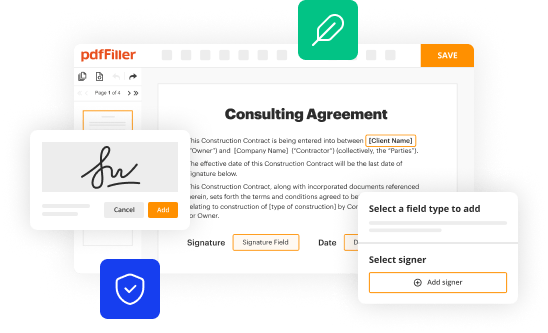
How can I send information it risk assessment for eSignature?
When your information it risk assessment is finished, send it to recipients securely and gather eSignatures with pdfFiller. You may email, text, fax, mail, or notarize a PDF straight from your account. Create an account today to test it.
How do I complete information it risk assessment online?
Easy online information it risk assessment completion using pdfFiller. Also, it allows you to legally eSign your form and change original PDF material. Create a free account and manage documents online.
Can I sign the information it risk assessment electronically in Chrome?
Yes, you can. With pdfFiller, you not only get a feature-rich PDF editor and fillable form builder but a powerful e-signature solution that you can add directly to your Chrome browser. Using our extension, you can create your legally-binding eSignature by typing, drawing, or capturing a photo of your signature using your webcam. Choose whichever method you prefer and eSign your information it risk assessment in minutes.
What is information it risk assessment?
Information security risk assessment is the process of identifying, assessing, and mitigating potential risks to the confidentiality, integrity, and availability of information and information systems.
Who is required to file information it risk assessment?
The specific requirements for filing an information security risk assessment vary depending on the jurisdiction, industry, and organization. Generally, it is the responsibility of organizations that handle sensitive or confidential information, such as government agencies, financial institutions, healthcare organizations, and large corporations.
How to fill out information it risk assessment?
The process of filling out an information security risk assessment involves identifying and documenting potential risks, evaluating the likelihood and impact of those risks, implementing controls and mitigation strategies, and regularly reviewing and updating the assessment as necessary.
What is the purpose of information it risk assessment?
The purpose of an information security risk assessment is to identify potential vulnerabilities, threats, and risks related to information and information systems, and to determine appropriate controls and mitigation strategies to manage those risks effectively.
What information must be reported on information it risk assessment?
The specific information that must be reported on an information security risk assessment can vary depending on the organization and industry. However, it typically includes an overview of the organization's information assets, identification of potential threats and vulnerabilities, assessment of the likelihood and impact of those risks, and a summary of the controls and mitigation strategies in place.
Fill out your information it risk assessment online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Information It Risk Assessment is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















