Get the free Risk, CyberSecurity and Technology Conference - California ...
Show details
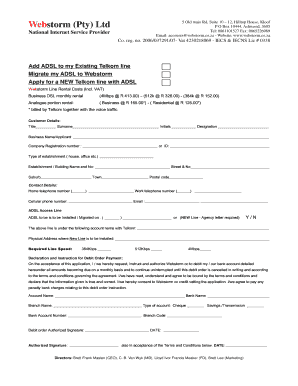
Risk, CyberSecurity and Technology Conference June 8-9, 2016 Hotel Maya Long Beach, California REGISTRATION FORM THREE WAYS TO REGISTER ONLINE! CREDIT CARD! Visit www.calbankers.com×RCT16 BY CHECK!
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign risk cybersecurity and technology

Edit your risk cybersecurity and technology form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your risk cybersecurity and technology form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing risk cybersecurity and technology online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit risk cybersecurity and technology. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, it's always easy to deal with documents. Try it right now
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out risk cybersecurity and technology

How to fill out risk cybersecurity and technology:
01
Identify the potential risks: Start by conducting a thorough risk assessment to identify the potential cybersecurity risks and threats that your organization may face. This includes assessing vulnerabilities in your technology systems, networks, and processes.
02
Define risk management strategies: Once you have identified the risks, develop a comprehensive risk management strategy. This includes creating protocols, policies, and guidelines for preventing, detecting, and responding to cybersecurity incidents. Assign responsibilities and establish clear communication channels within your organization.
03
Implement cybersecurity measures: Put in place robust cybersecurity measures to protect your organization's technology and data. This may include implementing firewalls, antivirus software, encryption, multi-factor authentication, intrusion detection systems, and regular software updates. Regularly review and update these measures to ensure they remain effective against evolving threats.
04
Train employees: Educate your employees about the importance of cybersecurity and provide training on best practices. This includes teaching them how to recognize and respond to common threats like phishing emails, social engineering scams, and malware attacks. Regularly conduct cybersecurity awareness campaigns and keep your employees informed about emerging threats.
05
Monitor and analyze: Continuously monitor your technology systems for any suspicious activities or vulnerabilities. Utilize security monitoring tools and establish a mechanism for real-time incident detection and response. Regularly analyze logs and audit trails to identify any potential security breaches or weaknesses in your cybersecurity measures.
Who needs risk cybersecurity and technology?
01
Businesses: Any organization that operates using digital technology and handles sensitive data, such as customer information, financial records, or intellectual property, needs risk cybersecurity and technology. This includes businesses of all sizes and across all industries.
02
Governments and public institutions: Governments and public institutions collect and store a vast amount of sensitive information. Protecting this data from cyber threats is crucial to maintain national security, protect citizens' privacy, and ensure public trust.
03
Individuals: In today's digital age, individuals also need to be aware of cybersecurity risks and take necessary precautions. This includes protecting personal devices, using strong passwords, being cautious while accessing online services, and staying informed about common cyber threats.
Overall, risk cybersecurity and technology are essential for anyone who relies on technology systems and handles sensitive data. It is crucial to understand the risks and implement necessary measures to mitigate those risks and protect against cyber threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is risk cybersecurity and technology?
Risk cybersecurity and technology refers to the potential threats and vulnerabilities that can impact an organization's information technology systems.
Who is required to file risk cybersecurity and technology?
Organizations in the technology sector or those that heavily rely on technology systems are generally required to file risk cybersecurity and technology.
How to fill out risk cybersecurity and technology?
Risk cybersecurity and technology assessments are typically filled out by IT professionals or cybersecurity experts within an organization.
What is the purpose of risk cybersecurity and technology?
The purpose of risk cybersecurity and technology assessments is to identify and mitigate potential cybersecurity risks that could impact an organization's technology systems.
What information must be reported on risk cybersecurity and technology?
Information such as security vulnerabilities, current cyber threats, and mitigation strategies must be reported on risk cybersecurity and technology assessments.
How do I execute risk cybersecurity and technology online?
pdfFiller has made filling out and eSigning risk cybersecurity and technology easy. The solution is equipped with a set of features that enable you to edit and rearrange PDF content, add fillable fields, and eSign the document. Start a free trial to explore all the capabilities of pdfFiller, the ultimate document editing solution.
Can I create an electronic signature for signing my risk cybersecurity and technology in Gmail?
It's easy to make your eSignature with pdfFiller, and then you can sign your risk cybersecurity and technology right from your Gmail inbox with the help of pdfFiller's add-on for Gmail. This is a very important point: You must sign up for an account so that you can save your signatures and signed documents.
How do I edit risk cybersecurity and technology on an Android device?
The pdfFiller app for Android allows you to edit PDF files like risk cybersecurity and technology. Mobile document editing, signing, and sending. Install the app to ease document management anywhere.
Fill out your risk cybersecurity and technology online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Risk Cybersecurity And Technology is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.