
Get the free Email Security Annual Review & Threat Report 2005 - home ku edu
Show details
The Postini Email Security Annual Review & Threat Report provides a summary of how spam and other email threats have evolved over the course of the past year; changes in the regulatory climate that
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign email security annual review
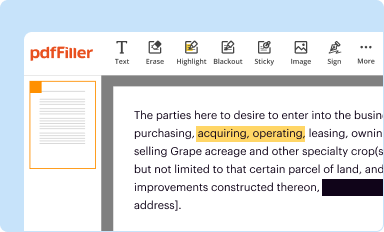
Edit your email security annual review form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
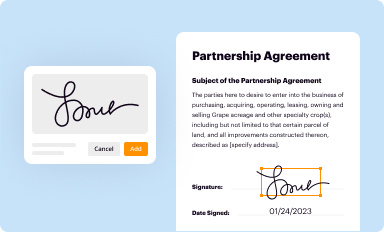
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
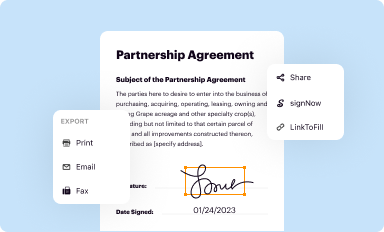
Share your form instantly
Email, fax, or share your email security annual review form via URL. You can also download, print, or export forms to your preferred cloud storage service.
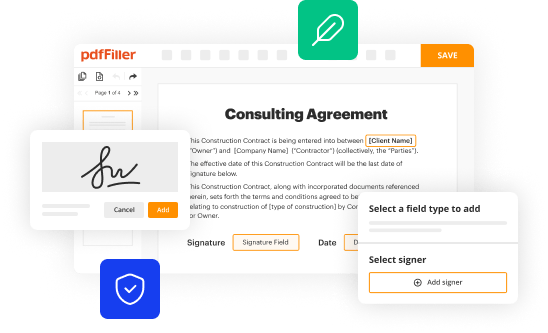
Editing email security annual review online
To use the services of a skilled PDF editor, follow these steps below:
1
Log in to account. Click Start Free Trial and sign up a profile if you don't have one yet.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit email security annual review. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Try it right now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out email security annual review
How to fill out Email Security Annual Review & Threat Report 2005
01
Begin by gathering all relevant email security data from the past year.
02
Review the current email security policies and procedures in place.
03
Analyze email security incidents and breaches that occurred during the year.
04
Compile statistics on spam, phishing attempts, and malware related to email.
05
Evaluate the effectiveness of existing security measures and tools used.
06
Prepare a summary of findings and outline recommended improvements.
07
Complete the report form, ensuring all sections are filled out accurately.
08
Review the completed document for accuracy and completeness before submission.
Who needs Email Security Annual Review & Threat Report 2005?
01
IT security teams responsible for maintaining email security.
02
Compliance officers ensuring adherence to regulations.
03
Management and executive teams needing an overview of email threats.
04
Auditors assessing the effectiveness of security protocols.
05
Employees in organizations wanting to understand their email security posture.
Fill
form
: Try Risk Free






People Also Ask about
What are the major security threats through email?
Protect against all 13 email threat types Spam. Spam costs businesses about $20 billion per year. Malware. 94 percent of malware is delivered via email. Data Exfiltration. URL Phishing. Scamming. Spear Phishing. Domain Impersonation. Brand Impersonation.
How to check your email security?
In Gmail, open a message. In the window, next to 'security', check the encryption type: Standard encryption (TLS) Enhanced encryption (S/MIME)
What is the email security score?
The Email Security Score is a metric used to evaluate the strength of your email's defenses against potential security threats. It takes into account factors like sender authentication protocols (SPF, DKIM, DMARC) and domain reputation.
How to write an email security policy?
A comprehensive email security policy should include the following elements. Purpose. Ownership. Privacy. Usage. Responsibilities. Restrictions. Consequences. Reporting.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Email Security Annual Review & Threat Report 2005?
The Email Security Annual Review & Threat Report 2005 is a comprehensive document that analyzes the email security landscape, including threats, vulnerabilities, and trends observed during the year 2005.
Who is required to file Email Security Annual Review & Threat Report 2005?
Organizations that manage email systems and handle sensitive information are typically required to file the Email Security Annual Review & Threat Report 2005 to ensure compliance with regulatory standards and improve their email security posture.
How to fill out Email Security Annual Review & Threat Report 2005?
To fill out the Email Security Annual Review & Threat Report 2005, organizations should gather data on email system performance, security incidents, and compliance metrics, and then enter them into the designated sections of the report template.
What is the purpose of Email Security Annual Review & Threat Report 2005?
The purpose of the Email Security Annual Review & Threat Report 2005 is to provide organizations with insights into email security risks, facilitate strategic planning for security improvements, and promote awareness of current email threats.
What information must be reported on Email Security Annual Review & Threat Report 2005?
The report must include information on security incidents, vulnerabilities identified, measures taken to mitigate risks, effectiveness of existing security protocols, compliance with relevant regulations, and overall email security posture.
Fill out your email security annual review online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Email Security Annual Review is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















