Get the free Application for Security Assessment - mines industry qld gov
Show details
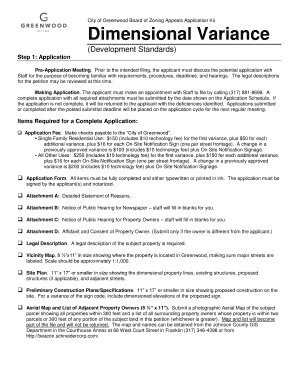
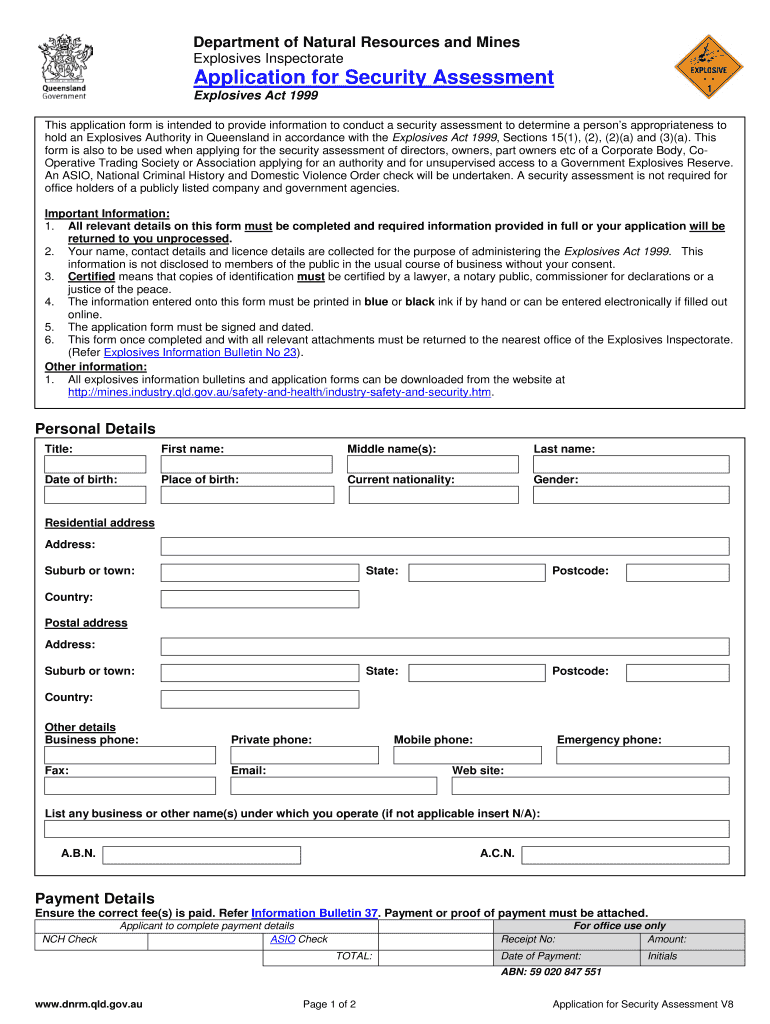
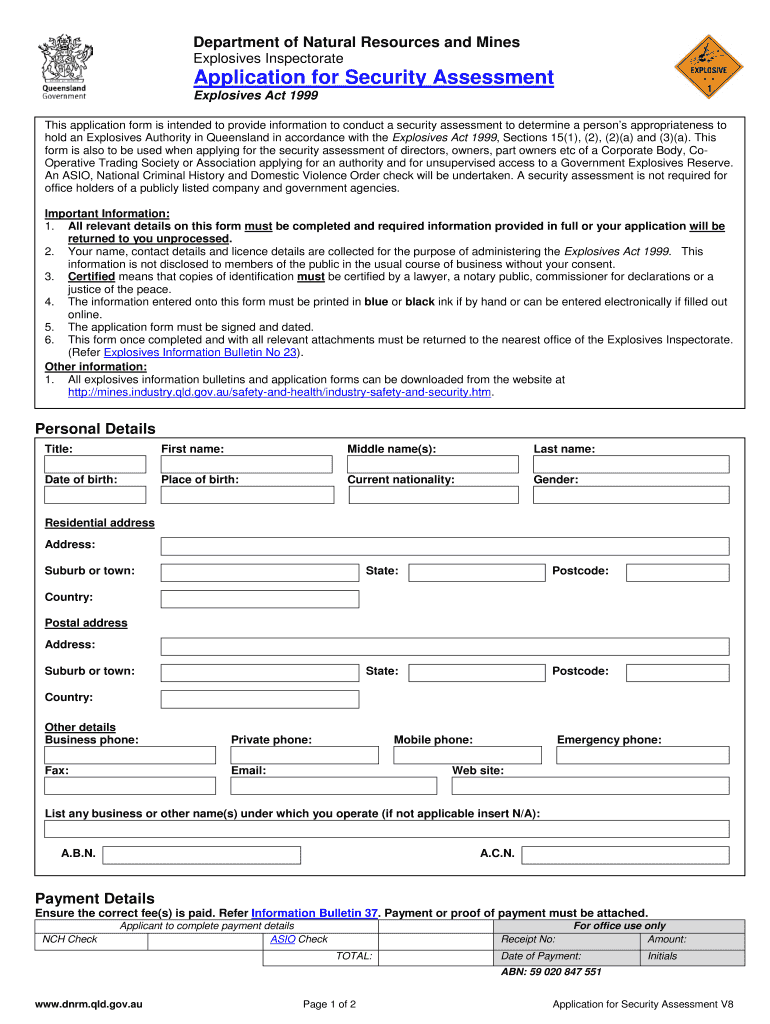
This application form is intended to provide information to conduct a security assessment for holding an Explosives Authority in Queensland as per the Explosives Act 1999. It includes provisions for
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign application for security assessment

Edit your application for security assessment form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your application for security assessment form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing application for security assessment online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in to your account. Click on Start Free Trial and sign up a profile if you don't have one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit application for security assessment. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
With pdfFiller, it's always easy to deal with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out application for security assessment

How to fill out Application for Security Assessment
01
Start by obtaining the Application for Security Assessment form from the appropriate authority or website.
02
Read the instructions carefully to understand the required information and supporting documents.
03
Fill out your personal information in the designated sections, including your name, contact details, and organization details.
04
Provide a detailed description of the security assessment you are requesting, including the scope and purpose.
05
Include any relevant background information or previous assessments related to your request.
06
Attach any necessary supporting documents, such as identification, organizational policies, or previous security assessments.
07
Review the completed application for accuracy and completeness.
08
Sign and date the application where required.
09
Submit the application form through the specified method, either online or via mail.
Who needs Application for Security Assessment?
01
Organizations seeking to assess their security measures and vulnerabilities.
02
Businesses requiring compliance with regulatory security standards.
03
Government agencies that need to ensure the safety and security of their operations.
04
Individuals wanting to evaluate personal security measures in certain circumstances.
05
Third-party vendors or service providers involved in sensitive information handling.
Fill
form
: Try Risk Free






People Also Ask about
How to write a security assessment?
The Security Risk Assessment Process Step 1: Map Your Assets. Step 2: Identify Security Threats & Vulnerabilities. Step 3: Determine & Prioritize Risks. Step 4: Analyze & Develop Security Controls. Step 5: Document Results From Risk Assessment Report. Step 6: Create A Remediation Plan To Reduce Risks.
What are examples of application security?
Firewalls, antivirus systems, and data encryption are just a few examples to prevent unauthorized users from entering a system. If an organization wishes to predict specific, sensitive data sets, they can establish unique application security policies for those resources.
How do you write a security assessment report?
Preparing a Security Assessment Report: 5 Steps Select a Template. The right template sets the foundation for a comprehensive vulnerability assessment report. Assess Existing Assets and Control Mechanisms. Evaluate Potential Threats. Analyze Vulnerabilities. Create a Mitigation Plan.
How to perform a security assessment?
Security assessments typically include two main components: security review and security testing.
What is application security assessment?
Application security assessments are a critical component of any effective cybersecurity strategy, providing the visibility needed to identify and address vulnerabilities before they can be exploited.
How to test the security of an application?
10 Essential Steps for Web Application Security Testing Implement SSDLC. Perform a risk assessment. Provide security training for developers. Use various security layers. Automate security tasks. Patch and update regularly. Adopt Continuous Security Monitoring tools. Document your results.
What are the two main components of security assessment?
A suggested outline of an assessment report is as follows: Critical demographic information (e.g. client name, age, gender etc.,) Referral question. Background information. Sources of information. Behavioural observations. Test results. Impressions and interpretations. Recommendations.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Application for Security Assessment?
The Application for Security Assessment is a formal request submitted to evaluate the security measures and practices of an organization or system to ensure compliance with relevant standards and regulations.
Who is required to file Application for Security Assessment?
Organizations or entities that handle sensitive information, manage critical infrastructure, or are subject to regulatory requirements related to security must file an Application for Security Assessment.
How to fill out Application for Security Assessment?
To fill out the Application for Security Assessment, provide detailed information about the organization's security policies, identify potential vulnerabilities, and include necessary documentation regarding security practices and measures implemented.
What is the purpose of Application for Security Assessment?
The purpose of the Application for Security Assessment is to ensure that an organization has adequate security measures in place to protect sensitive information and comply with regulatory standards.
What information must be reported on Application for Security Assessment?
The Application for Security Assessment must report information including organizational details, security policies, risk assessments, incident response plans, and documentation of compliance with applicable security standards.
Fill out your application for security assessment online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Application For Security Assessment is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.