Get the free Restricted Data Security Plan Checklist - hrsonline isr umich
Show details
This document outlines the necessary security measures and requirements for handling HRS restricted data in various computing environments, including physical enclave, virtual desktop infrastructure,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign restricted data security plan
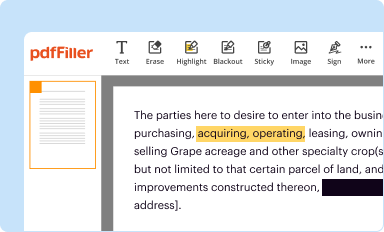
Edit your restricted data security plan form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
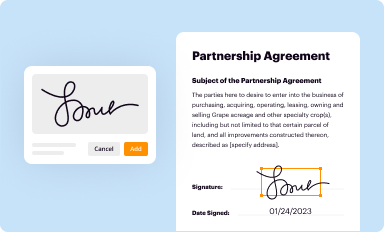
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your restricted data security plan form via URL. You can also download, print, or export forms to your preferred cloud storage service.
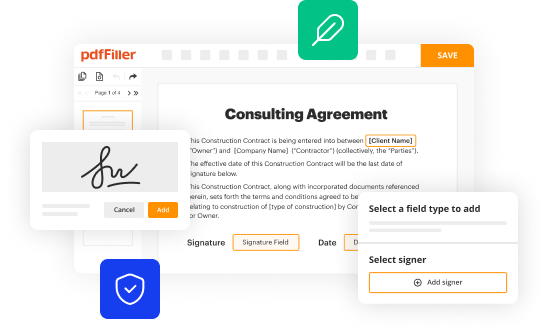
How to edit restricted data security plan online
To use the professional PDF editor, follow these steps below:
1
Log in to your account. Click Start Free Trial and sign up a profile if you don't have one yet.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit restricted data security plan. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out restricted data security plan
How to fill out Restricted Data Security Plan Checklist
01
Obtain the Restricted Data Security Plan Checklist template.
02
Review the definition and scope of restricted data relevant to your organization.
03
Identify all types of restricted data you handle during your operations.
04
Assess and document the current security measures in place for protecting restricted data.
05
Evaluate existing policies and procedures related to restricted data management.
06
Fill out each section of the checklist, providing detailed answers to indicate compliance or areas needing improvement.
07
Assign responsibility for each item in the checklist to specific personnel.
08
Set deadlines for completing any required actions noted on the checklist.
09
Review the completed checklist for accuracy and completeness.
10
Submit the finalized checklist to the relevant oversight body for approval.
Who needs Restricted Data Security Plan Checklist?
01
Organizations that handle restricted data, including educational institutions, healthcare providers, and businesses dealing with sensitive information.
02
Employees responsible for data security and compliance within organizations.
03
Compliance officers and security teams that need to ensure adherence to data protection regulations.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Restricted Data Security Plan Checklist?
The Restricted Data Security Plan Checklist is a document designed to ensure that organizations have comprehensive measures in place to protect sensitive data from unauthorized access and breaches.
Who is required to file Restricted Data Security Plan Checklist?
Organizations that handle or process restricted data, such as personally identifiable information (PII), health records, or financial information, are typically required to file the Restricted Data Security Plan Checklist.
How to fill out Restricted Data Security Plan Checklist?
To fill out the Restricted Data Security Plan Checklist, organizations should assess their current data security measures, identify potential risks, and provide detailed descriptions of their security protocols and practices in the designated sections of the checklist.
What is the purpose of Restricted Data Security Plan Checklist?
The purpose of the Restricted Data Security Plan Checklist is to guide organizations in implementing effective security measures, ensuring compliance with data protection regulations, and safeguarding sensitive information.
What information must be reported on Restricted Data Security Plan Checklist?
The Restricted Data Security Plan Checklist must report information such as data classification, security measures in place, incident response plans, employee training programs, and any identified vulnerabilities and mitigation strategies.
Fill out your restricted data security plan online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Restricted Data Security Plan is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.