
Get the free BSecurity Access Requestb for EMACS - sbcounty
Show details
Ensure that the most current form is submitted. Refer to EMACS Forms×Procedures website. SECURITY ACCESS REQUEST FOR EMACS Effective Date Access may be granted by individual and×or ranges of department
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign bsecurity access requestb for
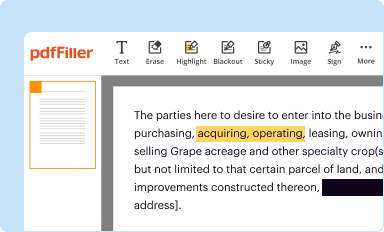
Edit your bsecurity access requestb for form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
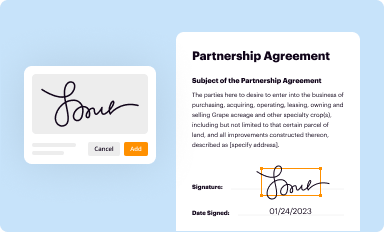
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
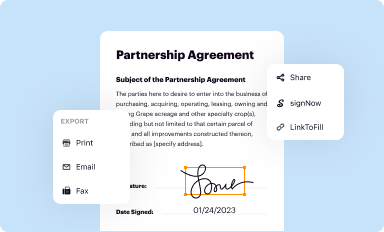
Share your form instantly
Email, fax, or share your bsecurity access requestb for form via URL. You can also download, print, or export forms to your preferred cloud storage service.
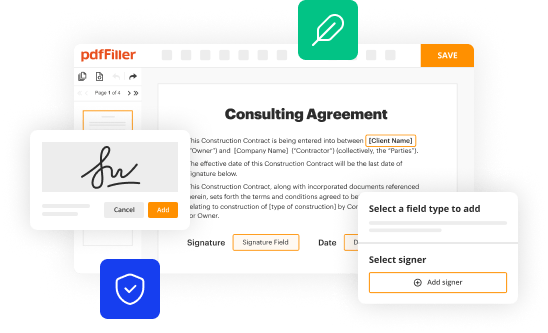
Editing bsecurity access requestb for online
To use the services of a skilled PDF editor, follow these steps:
1
Log in to account. Start Free Trial and register a profile if you don't have one.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit bsecurity access requestb for. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, it's always easy to deal with documents. Try it right now
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out bsecurity access requestb for
How to fill out a security access request form:
01
Start by gathering all the necessary information required for the form, such as your name, contact details, and employee identification number.
02
Identify the specific systems, areas, or resources that you need access to and make sure to clearly specify them on the form. This can include computer networks, physical locations, databases, or files.
03
Indicate the type of access you are requesting, whether it is full access, read-only access, or limited access to certain functions.
04
Provide a valid reason or justification for your access request. Explain why you need access to the requested systems or resources and how it would contribute to your work or responsibilities.
05
If applicable, include any relevant certifications, trainings, or qualifications that support your request for access.
06
Review the form to ensure that all information provided is accurate and complete. Double-check for any errors or missing details.
07
Sign and date the form to certify that the information provided is true and accurate.
08
Submit the completed form according to the specified procedure, whether it is through an online portal, email submission, or physical submission to the appropriate department or authority.
Who needs a security access request form:
01
Employees who are new to an organization and require access to various systems, resources, or areas.
02
Existing employees who have changed roles or responsibilities and need access to additional or different systems and resources.
03
Contractors, consultants, or temporary staff who need temporary access to specific systems or areas to perform their duties.
04
Individuals who are transferring to a different department or location and need new access privileges.
05
Anyone who needs to modify or revoke existing access rights due to changes in job roles, responsibilities, or project assignments.
Note: The specific requirements and processes for filling out a security access request form may vary depending on the organization and its policies. It is important to consult the relevant department or authority for any specific guidelines or instructions.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my bsecurity access requestb for in Gmail?
It's easy to use pdfFiller's Gmail add-on to make and edit your bsecurity access requestb for and any other documents you get right in your email. You can also eSign them. Take a look at the Google Workspace Marketplace and get pdfFiller for Gmail. Get rid of the time-consuming steps and easily manage your documents and eSignatures with the help of an app.
How do I edit bsecurity access requestb for in Chrome?
Download and install the pdfFiller Google Chrome Extension to your browser to edit, fill out, and eSign your bsecurity access requestb for, which you can open in the editor with a single click from a Google search page. Fillable documents may be executed from any internet-connected device without leaving Chrome.
How do I edit bsecurity access requestb for on an iOS device?
Use the pdfFiller mobile app to create, edit, and share bsecurity access requestb for from your iOS device. Install it from the Apple Store in seconds. You can benefit from a free trial and choose a subscription that suits your needs.
What is bsecurity access requestb for?
The security access request is for requesting access to secure systems or resources.
Who is required to file bsecurity access requestb for?
Employees who need access to security systems or resources are required to file a security access request.
How to fill out bsecurity access requestb for?
To fill out a security access request, one must provide necessary information such as personal details, reason for access, and required permissions.
What is the purpose of bsecurity access requestb for?
The purpose of the security access request is to ensure that only authorized individuals have access to sensitive information or resources.
What information must be reported on bsecurity access requestb for?
The security access request must include personal details, reason for access, required permissions, and any additional relevant information.
Fill out your bsecurity access requestb for online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Bsecurity Access Requestb For is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.


















