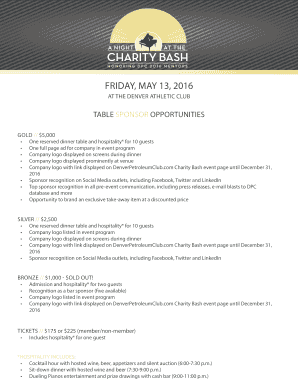
Get the free FireEye Advanced Threat Report: 2H 2012
Show details
This white paper provides an in-depth analysis of advanced cyber threats specifically targeting various industries, highlighting malware trends, attack patterns, and the impact of these attacks on
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign fireeye advanced threat report

Edit your fireeye advanced threat report form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your fireeye advanced threat report form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit fireeye advanced threat report online
Follow the guidelines below to benefit from a competent PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit fireeye advanced threat report. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Try it now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out fireeye advanced threat report

How to fill out FireEye Advanced Threat Report: 2H 2012
01
Obtain a copy of the FireEye Advanced Threat Report: 2H 2012 from the FireEye website or authorized sources.
02
Read the executive summary to understand the key findings and objectives of the report.
03
Go through each section systematically, focusing on the trends, case studies, and analysis provided.
04
Take notes on significant threats and recommended actions as described in the report.
05
Utilize the data in the report to compare with your organization's threat landscape.
06
Implement any suggested best practices or security measures to enhance your organization's cybersecurity posture.
Who needs FireEye Advanced Threat Report: 2H 2012?
01
Cybersecurity professionals looking to enhance their knowledge of advanced threats.
02
Organizations wanting to improve their threat detection and response capabilities.
03
IT managers and executives seeking insights to inform security investment decisions.
04
Threat intelligence analysts who require contextual information on emerging threats.
05
Compliance officers needing to understand industry trends related to cybersecurity.
Fill
form
: Try Risk Free






People Also Ask about
Who FireEye?
The hackers, widely believed to be affiliated with Russian intelligence agencies, stole FireEye's own tool kit consisting of roughly 300 proprietary software tools.
Does FireEye still exist?
In December 2013, Mandiant was acquired by FireEye for $1 billion, who eventually sold the FireEye product line, name, and its employees to Symphony Technology Group for $1.2 billion in June 2021.
Who bought out FireEye?
In June 2021, FireEye sold its name and products business to STG for $1.2bn. Symphony Technology Group (STG) acquired McAfee Enterprise in an all-cash transaction for US$4.0 billion in July 2021. STG combined FireEye with McAfee's enterprise business to launch Trellix, an extended detection and response (XDR) company.
How does FireEye detect?
FireEye uses behavior-based analysis instead of signature-based identification, which relies on finding known threats. This advanced method closely studies what files and programs that seem fishy do, finding strange things that haven't been seen before.
What is FireEye threat intelligence?
In conclusion, FireEye provides innovative solutions that help organisations detect, prevent, and respond to cybersecurity threats. Its advanced threat intelligence platform, combined with its team of experts, enables it to identify and address even the most sophisticated cyber threats.
What is a FireEye device?
FireEye Network Security is an effective cyber threat protection solution that helps organizations minimize the risk of costly breaches by accurately detecting and immediately stopping advanced, targeted and other evasive attacks hiding in Internet traffic.
Is FireEye still around?
In December 2013, Mandiant was acquired by FireEye for $1 billion, who eventually sold the FireEye product line, name, and its employees to Symphony Technology Group for $1.2 billion in June 2021.
What is the new name for FireEye?
A consortium led by Symphony Technology Group (STG) is the buyer. On Oct. 4, FireEye will change its corporate name and relaunch as Mandiant. That's during its annual Cyber Defense Summit (CDS) 2021.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is FireEye Advanced Threat Report: 2H 2012?
The FireEye Advanced Threat Report: 2H 2012 is a comprehensive analysis that outlines the evolving nature of cyber threats, detailing specific attacks, techniques, and trends observed during the second half of 2012.
Who is required to file FireEye Advanced Threat Report: 2H 2012?
There are typically no formal filing requirements for the FireEye Advanced Threat Report as it is produced by FireEye for informational and educational purposes. However, organizations concerned about cybersecurity may refer to it for insights.
How to fill out FireEye Advanced Threat Report: 2H 2012?
The FireEye Advanced Threat Report is not a document that individuals fill out; rather, it is a published report that provides analysis and findings related to cyber threats. Readers are encouraged to review and analyze the contents.
What is the purpose of FireEye Advanced Threat Report: 2H 2012?
The purpose of the FireEye Advanced Threat Report: 2H 2012 is to inform organizations about the state of cyber threats, offering insights, data, and recommendations to enhance their cybersecurity posture.
What information must be reported on FireEye Advanced Threat Report: 2H 2012?
The report contains information on specific cyber attack trends, threat actor profiles, attack methods, and recommendations for improving security measures within organizations.
Fill out your fireeye advanced threat report online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Fireeye Advanced Threat Report is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.