Get the free behind the scenes attack at sea scholastics answers form
Show details
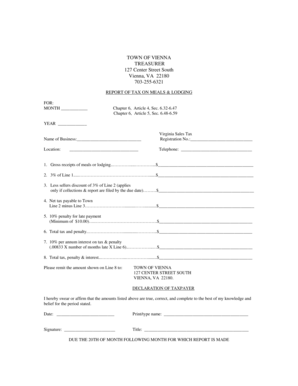
Video Activity Name: Date: Attack at Sea February×March 2016 Video Discussion Questions Directions: Watch the video Behind the Scenes: Attack at Sea. Then answer the questions below. 1. What research
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign behind form scenes attack

Edit your behind form scenes attack form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your behind form scenes attack form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing behind form scenes attack online
In order to make advantage of the professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit behind form scenes attack. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out behind form scenes attack

How to fill out behind form scenes attack?
01
Understand the concept: Before diving into the process of filling out behind form scenes attack, it is crucial to have a clear understanding of what it entails. Behind form scenes attack refers to a malicious act where an attacker exploits vulnerabilities in web forms to gain unauthorized access or gather sensitive information. Familiarize yourself with the various techniques used in such attacks, such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF).
02
Identify potential targets: As a defender, it is essential to identify potential targets vulnerable to behind form scenes attacks. This includes websites or web applications that have not implemented proper security measures or have poorly designed form validation processes. Conduct a thorough analysis of the target system to identify vulnerabilities that can be exploited by an attacker.
03
Harden your defenses: Implement robust security measures to protect against behind form scenes attacks. This includes ensuring that all web forms have proper input validation and sanitization techniques in place. Apply security patches and updates to the underlying software and frameworks used in the web application. Implement secure coding practices and adhere to industry-standard security guidelines.
04
Educate users and developers: Behind form scenes attacks can be significantly mitigated by educating both end-users and developers. Users should be cautioned against clicking on suspicious links or submitting sensitive information on untrusted websites. Developers should stay updated with the latest security best practices and receive training on secure coding methodologies to ensure that vulnerabilities are minimized during the development phase.
Who needs behind form scenes attack?
01
Web developers: Understanding behind form scenes attacks is crucial for developers responsible for designing and implementing web forms. By comprehending the techniques used in these attacks, developers can build robust defenses and ensure that their applications are resistant to such exploits. Implementing secure coding practices and staying updated with the latest security trends will help developers create more secure web forms.
02
System administrators: System administrators play a vital role in managing the infrastructure on which web applications or websites are hosted. By understanding behind form scenes attacks, administrators can take appropriate measures to protect the underlying systems. This includes implementing Intrusion Detection Systems (IDS), firewalls, and regular system updates to prevent unauthorized access and ensure the security of the infrastructure.
03
Security professionals: Behind form scenes attacks are a significant concern for security professionals responsible for protecting organizations' assets. By understanding the tactics and techniques employed by attackers, security professionals can devise comprehensive mitigation strategies. This includes conducting regular vulnerability assessments, penetration testing, and implementing security controls to safeguard against behind form scenes attacks.
It is important to note that behind form scenes attacks are illegal and unethical. The information provided here should only be used for educational purposes and to enhance the security of web applications.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is behind form scenes attack?
Behind Form Scenes Attack refers to a type of cyber attack where hackers gain unauthorized access to an organization's systems or networks by using malicious software or techniques.
Who is required to file behind form scenes attack?
Any organization that has been a victim of a Behind Form Scenes Attack is required to file a report with the appropriate authorities.
How to fill out behind form scenes attack?
To fill out a report on Behind Form Scenes Attack, organizations should provide detailed information about the incident, including the date and time of the attack, the type of malware used, and any damages or losses incurred.
What is the purpose of behind form scenes attack?
The purpose of a Behind Form Scenes Attack can vary, but it is typically done to steal sensitive information, disrupt operations, or extort money from the victim.
What information must be reported on behind form scenes attack?
Information that must be reported on Behind Form Scenes Attack includes details about the attack itself, any data that was compromised, and the steps taken to mitigate the damage.
Can I create an electronic signature for the behind form scenes attack in Chrome?
Yes. By adding the solution to your Chrome browser, you can use pdfFiller to eSign documents and enjoy all of the features of the PDF editor in one place. Use the extension to create a legally-binding eSignature by drawing it, typing it, or uploading a picture of your handwritten signature. Whatever you choose, you will be able to eSign your behind form scenes attack in seconds.
Can I create an eSignature for the behind form scenes attack in Gmail?
When you use pdfFiller's add-on for Gmail, you can add or type a signature. You can also draw a signature. pdfFiller lets you eSign your behind form scenes attack and other documents right from your email. In order to keep signed documents and your own signatures, you need to sign up for an account.
How do I edit behind form scenes attack on an Android device?
With the pdfFiller mobile app for Android, you may make modifications to PDF files such as behind form scenes attack. Documents may be edited, signed, and sent directly from your mobile device. Install the app and you'll be able to manage your documents from anywhere.
Fill out your behind form scenes attack online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Behind Form Scenes Attack is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.