
Get the free BCM Report - Security Management
Show details
A Risk-Focused Review of Business Continuity Management In Major Financial Groups Post September 11, 2001, Mark Bruce Deposit Takers Division Risk & Operational Support September 2002 A Risk-Focused
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign bcm report - security
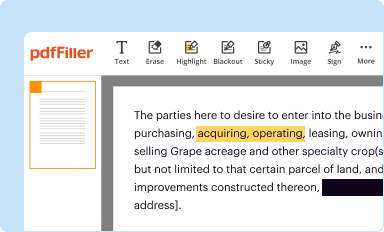
Edit your bcm report - security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
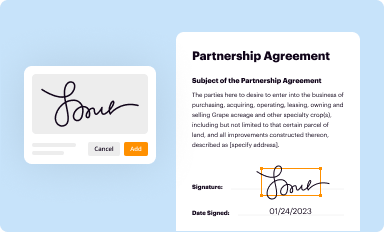
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
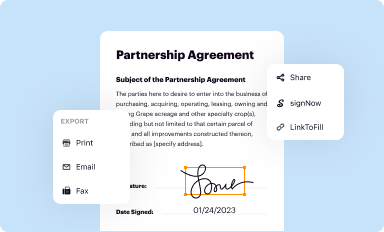
Share your form instantly
Email, fax, or share your bcm report - security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
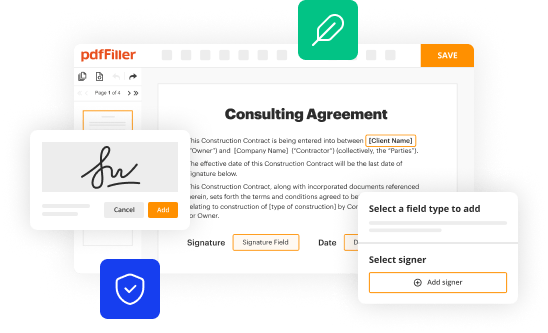
How to edit bcm report - security online
To use the professional PDF editor, follow these steps below:
1
Log into your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit bcm report - security. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, it's always easy to deal with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out bcm report - security
How to fill out bcm report - security:
01
Start by gathering all relevant information related to the security incidents or breaches that occurred within the organization. This could include incident details, date and time, affected systems or assets, and any other crucial information.
02
Use a standardized template or form provided by your organization to ensure consistency and uniformity in reporting. If such a template is not available, create a document with clear sections for each aspect of the report.
03
Begin the report with an executive summary, providing a brief overview of the security incident. Summarize the impact, severity, and potential risks associated with the incident.
04
Next, provide a detailed description of the security incident. Include information about the nature of the breach or incident, how it was detected, and any initial actions taken to mitigate the impact.
05
Document the root causes of the security incident. Identify any vulnerabilities or weaknesses in the organization's security controls or practices that enabled the breach to occur. This helps in identifying areas for improvement and preventing future incidents.
06
Describe the actions taken to contain and resolve the security incident. Include details about the steps taken to restore normal operations, restore affected systems, and address any immediate impact on the organization's security posture.
07
Provide a timeline of events, noting the sequence of actions and important milestones during the incident response process. This helps in understanding the overall incident timeline and aids in identifying areas where the response could have been improved.
08
Document any lessons learned from the incident. Identify the strengths and weaknesses of the organization's security response and highlight opportunities for improvement in future incident management processes.
09
Finally, include any recommendations for improving security controls or practices based on the incident. These recommendations should be actionable and prioritize areas that require immediate attention to prevent similar incidents from occurring again.
Who needs bcm report - security?
01
Organizations of all sizes and industries can benefit from a bcm report - security. It is crucial for businesses to have a clear understanding of their security incidents, breaches, and response processes to mitigate risks and make informed decisions.
02
Security teams and incident response teams within the organization are primary audiences for the bcm report - security. These teams use the report to analyze incidents, identify patterns, and develop strategies to improve security postures.
03
Internal stakeholders, such as senior management, executives, and board members, also need access to bcm reports - security. This helps them understand the organization's security posture, evaluate the effectiveness of security controls, and make informed decisions about resource allocation for future security measures.
04
External stakeholders, including regulators, auditors, and clients, may also require access to bcm reports - security. Compliance with regulatory requirements and client expectations often necessitate detailed reporting on security incidents to demonstrate the organization's commitment to safeguarding sensitive information and maintaining a secure environment.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is bcm report - security?
The bcm report - security is a report that focuses on the security aspects of a business continuity management system (BCMS). It provides an assessment of security measures and controls in place to mitigate risks.
Who is required to file bcm report - security?
Organizations that have implemented a business continuity management system (BCMS) and want to ensure the security of their operations are required to file the bcm report - security.
How to fill out bcm report - security?
To fill out the bcm report - security, organizations should gather and analyze relevant security data, evaluate the effectiveness of security controls, and document their findings and recommendations.
What is the purpose of bcm report - security?
The purpose of the bcm report - security is to assess the security measures and controls implemented in a business continuity management system (BCMS) and identify any gaps or areas for improvement.
What information must be reported on bcm report - security?
The bcm report - security should include information on the security controls, vulnerabilities, threats, and risks identified during the assessment, as well as recommendations for enhancing security.
How can I manage my bcm report - security directly from Gmail?
pdfFiller’s add-on for Gmail enables you to create, edit, fill out and eSign your bcm report - security and any other documents you receive right in your inbox. Visit Google Workspace Marketplace and install pdfFiller for Gmail. Get rid of time-consuming steps and manage your documents and eSignatures effortlessly.
How can I send bcm report - security to be eSigned by others?
When your bcm report - security is finished, send it to recipients securely and gather eSignatures with pdfFiller. You may email, text, fax, mail, or notarize a PDF straight from your account. Create an account today to test it.
Can I create an electronic signature for signing my bcm report - security in Gmail?
Upload, type, or draw a signature in Gmail with the help of pdfFiller’s add-on. pdfFiller enables you to eSign your bcm report - security and other documents right in your inbox. Register your account in order to save signed documents and your personal signatures.
Fill out your bcm report - security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Bcm Report - Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















