Get the free Multiple Vulnerabilities in Wind River VxWorks Could Allow for ...
Show details
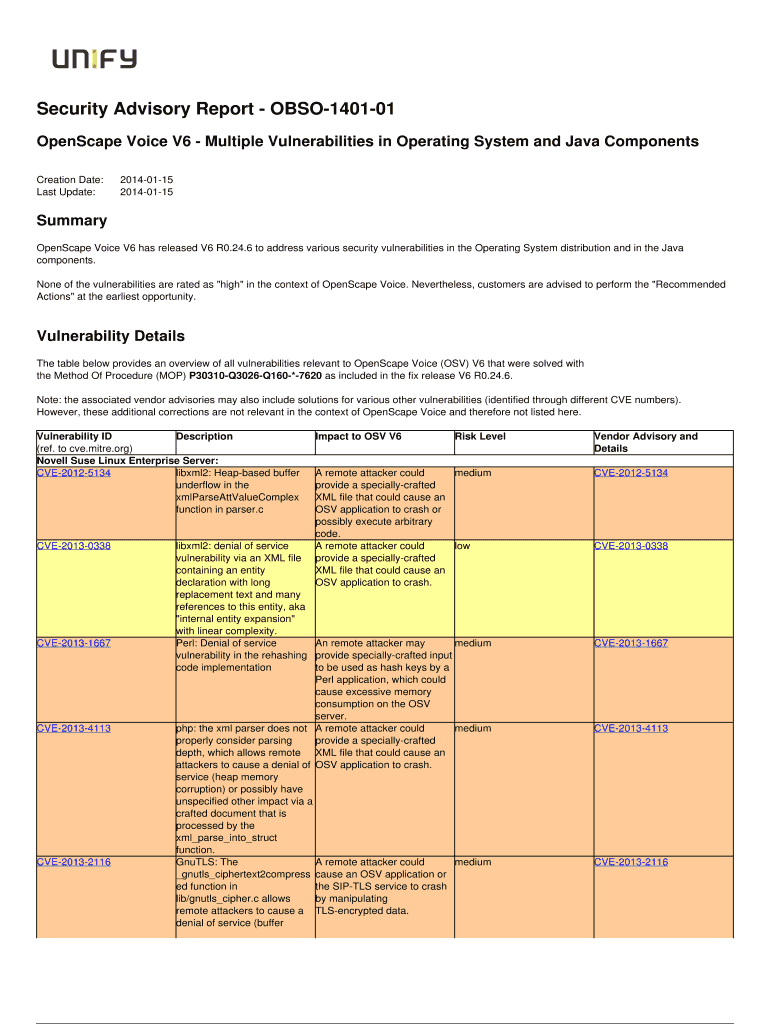
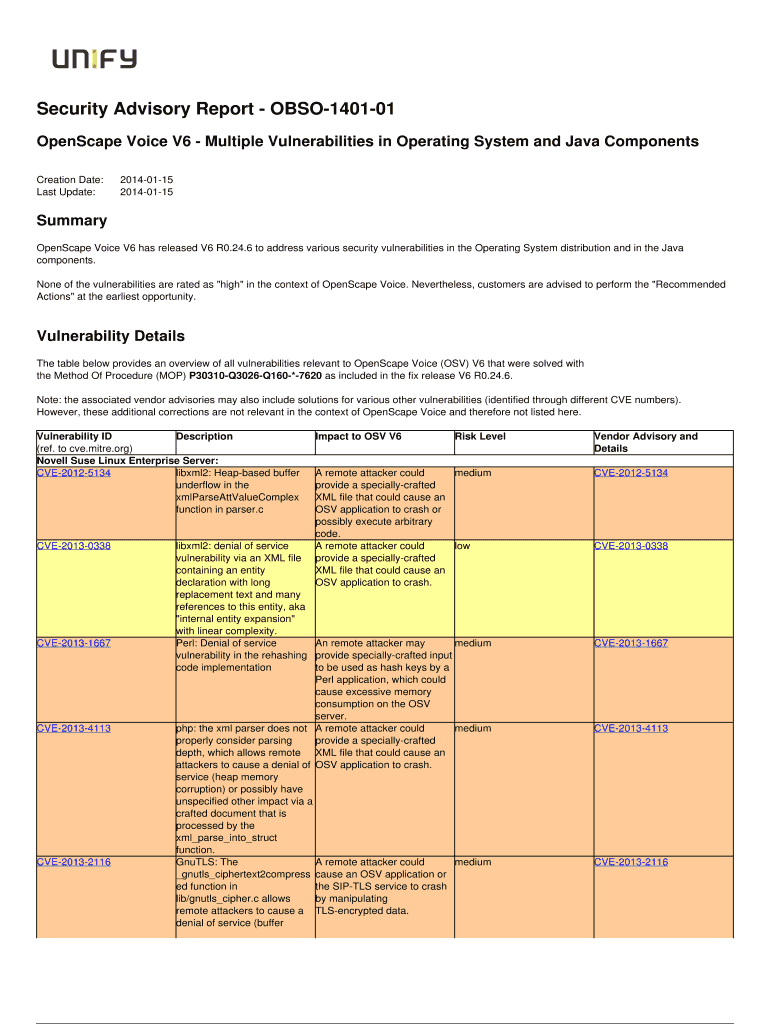
Security Advisory Report OBSO140101 Opens cape Voice V6 Multiple Vulnerabilities in Operating System and Java Components Creation Date: Last Update:20140115 20140115Summary Opens cape Voice V6 has
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign multiple vulnerabilities in wind

Edit your multiple vulnerabilities in wind form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your multiple vulnerabilities in wind form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit multiple vulnerabilities in wind online
Use the instructions below to start using our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit multiple vulnerabilities in wind. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out multiple vulnerabilities in wind

How to fill out multiple vulnerabilities in wind:
01
Identify the vulnerabilities: Begin by conducting a comprehensive assessment of the wind system to identify the multiple vulnerabilities present. This could involve inspecting the physical infrastructure, analyzing network connections, or assessing software vulnerabilities.
02
Prioritize the vulnerabilities: Once the vulnerabilities have been identified, categorize them based on their severity and potential impact. This will help in prioritizing the mitigation efforts and addressing the most critical vulnerabilities first.
03
Develop a mitigation strategy: Create a detailed plan to address the vulnerabilities. This may involve implementing security patches or updates, enhancing physical security measures, or implementing network security protocols.
04
Allocate resources: Determine the resources required to address the multiple vulnerabilities effectively. This could include personnel, budget, technology solutions, or any other necessary resources to mitigate the identified risks.
05
Implement the mitigation plan: Execute the mitigation strategy by implementing the necessary measures to address the vulnerabilities. This could involve installing security patches, improving access control, conducting employee awareness training, or any other actions required based on the specific vulnerabilities.
Who needs multiple vulnerabilities in wind:
01
Wind energy companies: Any organization involved in the wind energy sector, such as wind turbine manufacturers, operators, or maintenance companies, may encounter multiple vulnerabilities in their wind systems. It is crucial for these organizations to address these vulnerabilities to ensure the safe and reliable operation of their wind turbines.
02
Energy regulators and authorities: Regulators and authorities responsible for overseeing the wind energy industry need to be aware of the vulnerabilities present in wind systems. By understanding these vulnerabilities, they can develop regulations and guidelines to ensure the security and resilience of the wind energy infrastructure.
03
Cybersecurity professionals: Professionals specializing in cybersecurity consulting or services may be engaged by wind energy companies to identify and address multiple vulnerabilities in wind systems. These experts help in assessing risks, developing mitigation strategies, and implementing necessary security measures.
04
Researchers and academics: Researchers and academics studying renewable energy or wind energy specifically may be interested in exploring the vulnerabilities present in wind systems. By understanding these vulnerabilities, they can contribute to the development of improved security measures and practices in the industry.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is multiple vulnerabilities in wind?
Multiple vulnerabilities in wind refer to the identification of more than one weaknesses or susceptibilities in the wind energy system that could potentially be exploited by malicious actors or lead to system failures.
Who is required to file multiple vulnerabilities in wind?
Any organization or individual involved in the operation, maintenance, or development of wind energy systems is required to file multiple vulnerabilities in wind.
How to fill out multiple vulnerabilities in wind?
Multiple vulnerabilities in wind can be filled out by documenting the identified weaknesses or susceptibilities, their potential impacts, and any mitigation measures that have been or will be implemented.
What is the purpose of multiple vulnerabilities in wind?
The purpose of multiple vulnerabilities in wind is to ensure the security and reliability of wind energy systems by proactively identifying and addressing potential weaknesses or susceptibilities.
What information must be reported on multiple vulnerabilities in wind?
The information that must be reported on multiple vulnerabilities in wind includes the identified weaknesses or susceptibilities, their potential impacts, and any mitigation measures that have been or will be implemented.
How can I manage my multiple vulnerabilities in wind directly from Gmail?
Using pdfFiller's Gmail add-on, you can edit, fill out, and sign your multiple vulnerabilities in wind and other papers directly in your email. You may get it through Google Workspace Marketplace. Make better use of your time by handling your papers and eSignatures.
How can I send multiple vulnerabilities in wind to be eSigned by others?
Once your multiple vulnerabilities in wind is complete, you can securely share it with recipients and gather eSignatures with pdfFiller in just a few clicks. You may transmit a PDF by email, text message, fax, USPS mail, or online notarization directly from your account. Make an account right now and give it a go.
How do I execute multiple vulnerabilities in wind online?
Easy online multiple vulnerabilities in wind completion using pdfFiller. Also, it allows you to legally eSign your form and change original PDF material. Create a free account and manage documents online.
Fill out your multiple vulnerabilities in wind online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Multiple Vulnerabilities In Wind is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.