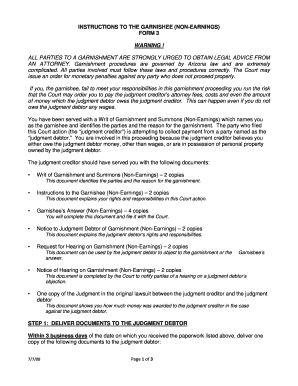
Get the free "Hacker Tools, Techniques, Exploits and Incident Handling (SEC504)" - pen-...
Show details
Use offense to inform defense. Find flaws before the bad guys do. Copyright SANS Institute Author Retains Full Rights This paper is from the SANS Penetration Testing site. Reposting is not permitted
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign quothacker tools techniques exploits

Edit your quothacker tools techniques exploits form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your quothacker tools techniques exploits form via URL. You can also download, print, or export forms to your preferred cloud storage service.
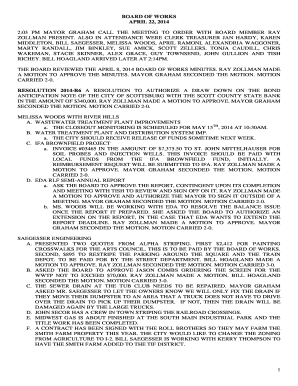
Editing quothacker tools techniques exploits online
Follow the guidelines below to benefit from the PDF editor's expertise:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit quothacker tools techniques exploits. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Try it for yourself by creating an account!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out quothacker tools techniques exploits

How to fill out quothacker tools techniques exploits:
01
First, familiarize yourself with the various types of quothacker tools, techniques, and exploits available. This can include learning about different hacking tools, such as network scanners, password crackers, and vulnerability scanners, as well as understanding common hacking techniques and exploits, such as SQL injection, cross-site scripting, and buffer overflow attacks.
02
Next, assess the specific needs and goals of your organization or project. Determine why you require quothacker tools, techniques, and exploits. Are you looking to test the security of your own systems, identify vulnerabilities, or understand potential threats? Understanding your objectives will help guide your selection and usage of quothacker tools.
03
Research and select the appropriate quothacker tools, techniques, and exploits for your needs. There are numerous resources available online, including open-source tools, commercial software, and educational materials. Consider factors such as compatibility with your systems, ease of use, and availability of support or documentation.
04
Once you have selected the tools and techniques you plan to use, familiarize yourself with their specific functionalities and features. Take the time to read the user manuals, tutorials, and guides provided by the tool creators or the broader hacking community. This will help you fully understand how to use each tool effectively and avoid any potential pitfalls or mistakes.
05
Before utilizing quothacker tools, techniques, and exploits, it is crucial to obtain proper authorization and legal permission. Hacking without permission is illegal and unethical. Ensure that you have the necessary consent from the relevant stakeholders, such as system owners or management, to conduct any hacking activities. This step is essential in maintaining legal and ethical boundaries.
06
Begin applying the quothacker tools, techniques, and exploits based on your objectives. Start with a controlled environment or a testing environment to minimize the risks associated with hacking activities. Conducting tests on your own systems or authorized targets can help identify vulnerabilities and strengthen security measures.
Who needs quothacker tools techniques exploits:
01
Organizations and businesses aiming to assess the security of their systems and networks can benefit from quothacker tools, techniques, and exploits. By using these tools, they can identify vulnerabilities and potential weaknesses in their infrastructure, allowing them to mitigate risks and enhance their security posture.
02
Security professionals, such as ethical hackers or penetration testers, require quothacker tools, techniques, and exploits to perform their job effectively. These professionals are responsible for proactively identifying and addressing vulnerabilities in their clients' systems. Quothacker tools provide them with the necessary means to simulate real-world attacks and evaluate the resilience of their clients' defenses.
03
Researchers and developers in the field of cybersecurity often utilize quothacker tools, techniques, and exploits to better understand emerging threats and develop countermeasures. By studying and analyzing these tools, they can stay ahead of potential attackers and contribute to the overall improvement of security in the digital landscape.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is quothacker tools techniques exploits?
Quothacker tools techniques exploits refer to a collection of tools and techniques used by hackers to exploit vulnerabilities in computer systems.
Who is required to file quothacker tools techniques exploits?
Anyone who discovers or uses quothacker tools techniques exploits is required to report it to the appropriate authorities.
How to fill out quothacker tools techniques exploits?
To fill out quothacker tools techniques exploits, one must document the details of the exploit, including the vulnerabilities exploited and the potential impact.
What is the purpose of quothacker tools techniques exploits?
The purpose of quothacker tools techniques exploits is to identify and address security vulnerabilities in computer systems before they can be exploited by malicious actors.
What information must be reported on quothacker tools techniques exploits?
The report on quothacker tools techniques exploits must include details of the exploit, the vulnerabilities exploited, and any potential impact on the affected systems.
How can I send quothacker tools techniques exploits to be eSigned by others?
When your quothacker tools techniques exploits is finished, send it to recipients securely and gather eSignatures with pdfFiller. You may email, text, fax, mail, or notarize a PDF straight from your account. Create an account today to test it.
Where do I find quothacker tools techniques exploits?
It's simple with pdfFiller, a full online document management tool. Access our huge online form collection (over 25M fillable forms are accessible) and find the quothacker tools techniques exploits in seconds. Open it immediately and begin modifying it with powerful editing options.
How do I make edits in quothacker tools techniques exploits without leaving Chrome?
Add pdfFiller Google Chrome Extension to your web browser to start editing quothacker tools techniques exploits and other documents directly from a Google search page. The service allows you to make changes in your documents when viewing them in Chrome. Create fillable documents and edit existing PDFs from any internet-connected device with pdfFiller.
Fill out your quothacker tools techniques exploits online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Quothacker Tools Techniques Exploits is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.