Get the free 網路攻擊及防範實務 - gsn nat gov
Show details
本文件提供關於網際網路安全的詳細分析,包括駭客入侵、惡意程式和社交工程攻擊的類型、手法和防範措施。
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign gsn nat gov

Edit your gsn nat gov form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your gsn nat gov form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing gsn nat gov online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit gsn nat gov. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
pdfFiller makes working with documents easier than you could ever imagine. Try it for yourself by creating an account!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out gsn nat gov

How to fill out 網路攻擊及防範實務
01
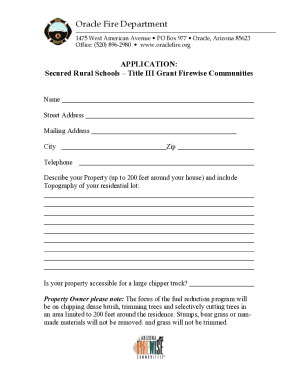
Begin with the title page, including the document's title '網路攻擊及防範實務'.
02
Provide an introduction that outlines the purpose and scope of the document.
03
Fill out the section on types of network attacks, detailing each type with examples.
04
Include a part on preventive measures, explaining how to safeguard networks against the mentioned attacks.
05
Add a section on monitoring and response strategies for when attacks occur.
06
Conclude with a summary of key points and recommendations for best practices.
07
Cite any references or resources used in compiling the information in a bibliography section.
Who needs 網路攻擊及防範實務?
01
IT professionals responsible for network security.
02
Business owners looking to protect their company's data.
03
Organizations that manage sensitive information and require a secure network.
04
Cybersecurity students and educators seeking practical knowledge.
05
Government agencies involved in national security and information protection.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is 網路攻擊及防範實務?
網路攻擊及防範實務 refers to the practices and strategies employed to prevent and mitigate cyber attacks on networks. It involves a comprehensive approach to understanding potential threats, implementing security measures, and responding to incidents.
Who is required to file 網路攻擊及防範實務?
Organizations and entities that manage sensitive data or critical infrastructure are typically required to file 網路攻擊及防範實務. This includes businesses in sectors such as finance, healthcare, and government.
How to fill out 網路攻擊及防範實務?
Filling out 網路攻擊及防範實務 involves providing detailed information about the organization's cybersecurity measures, risk assessments, incident response plans, and any previous security breaches.
What is the purpose of 網路攻擊及防範實務?
The purpose of 網路攻擊及防範實務 is to ensure organizations take proactive steps to protect their network and data from cyber attacks, to foster a culture of cybersecurity awareness, and to comply with regulatory requirements.
What information must be reported on 網路攻擊及防範實務?
Information that must be reported includes the organization's security policies, details of any cyber incidents that occurred, measures taken to prevent future attacks, and an assessment of the current security posture.
Fill out your gsn nat gov online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Gsn Nat Gov is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.