Get the free Information Security Summit 2 Day Event 15-16 January 2014
Show details
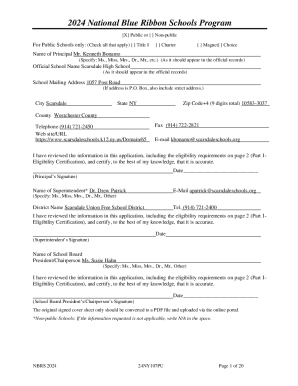
Information Security Summit 4401 Dockside Road, Suite 300, Independence, OH 44131 2-Day Event 1516 January 2014 The IT Governance Network is accredited by APM Gas a CUBIT 5 trainer. Assessing the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign information security summit 2

Edit your information security summit 2 form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your information security summit 2 form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing information security summit 2 online
Use the instructions below to start using our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit information security summit 2. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out information security summit 2

How to fill out information security summit 2:
01
Start by visiting the official website of the information security summit 2.
02
Look for the registration or signup button/link on the website.
03
Click on the registration/sign up button/link to begin the process.
04
Fill in the required personal information such as your name, email address, and phone number.
05
Provide any additional information that may be requested, such as your job title or company name.
06
Select the appropriate ticket type or registration option, if applicable.
07
Choose any additional add-ons or packages that you may be interested in.
08
Review your entered information to ensure correctness and make any necessary changes.
09
Proceed to the payment section and provide the required payment details, if applicable.
10
Confirm your registration by clicking on the submit or register button.
11
Wait for a confirmation email or receipt to be sent to the email address provided during registration.
Who needs information security summit 2:
01
IT professionals: Information security summit 2 is specifically designed for IT professionals who are responsible for ensuring the security and protection of data and information within their organizations.
02
Cybersecurity experts: This summit is highly beneficial for cybersecurity experts who want to stay updated with the latest trends, tools, and techniques in the field of information security.
03
Business owners and managers: Information security summit 2 provides valuable insights and knowledge to business owners and managers who are concerned about the security of their company's digital assets and want to implement effective security measures.
04
Government officials: Information security is a critical aspect of national security, and government officials responsible for cybersecurity policies and protocols can benefit from attending this summit to enhance their knowledge and stay updated on emerging threats and best practices.
05
Students and aspiring professionals: Students pursuing a career in information security or individuals looking to enter the cybersecurity industry can gain valuable knowledge and network with professionals in the field by attending this summit.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send information security summit 2 for eSignature?
When you're ready to share your information security summit 2, you can swiftly email it to others and receive the eSigned document back. You may send your PDF through email, fax, text message, or USPS mail, or you can notarize it online. All of this may be done without ever leaving your account.
How do I edit information security summit 2 in Chrome?
Install the pdfFiller Google Chrome Extension to edit information security summit 2 and other documents straight from Google search results. When reading documents in Chrome, you may edit them. Create fillable PDFs and update existing PDFs using pdfFiller.
Can I edit information security summit 2 on an iOS device?
Create, edit, and share information security summit 2 from your iOS smartphone with the pdfFiller mobile app. Installing it from the Apple Store takes only a few seconds. You may take advantage of a free trial and select a subscription that meets your needs.
What is information security summit 2?
Information Security Summit 2 is a conference or event focused on discussing and addressing issues related to information security.
Who is required to file information security summit 2?
Organizations or individuals involved in the field of information security may be required to file Information Security Summit 2, depending on the specific requirements of the event.
How to fill out information security summit 2?
Information Security Summit 2 can usually be filled out online or by submitting a form provided by the organizers of the event. Specific instructions for filling out the form will be provided by the event organizers.
What is the purpose of information security summit 2?
The purpose of Information Security Summit 2 is to bring together experts and professionals in the field of information security to discuss and collaborate on various information security issues and challenges.
What information must be reported on information security summit 2?
The specific information that must be reported on Information Security Summit 2 will vary depending on the requirements set by the event organizers. This may include details about the organization, presentation topics, and participant information.
Fill out your information security summit 2 online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Information Security Summit 2 is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.