Get the free csam cybersecurity
Show details
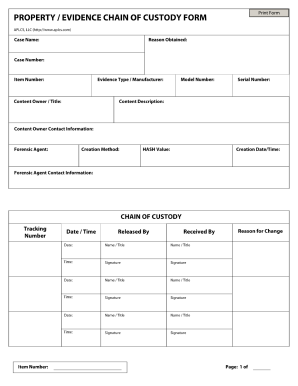
Privacy Impact Assessment PIA for the Cyber Security Assessment and Management CSAM Certification Accreditation C A Web SBU Department of Justice Information Technology Security Staff ITSS April 11 2007 Page 3 Table of Contents Approval Signature Page.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign csam cyber security form
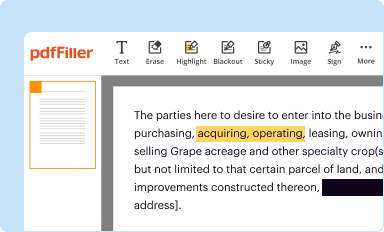
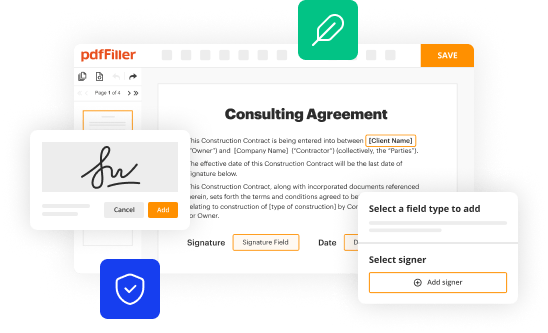
Edit your doj csam user guide form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your csam cybersecurity assessment and management form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit cyber security assessment and management csam tool online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit cyber security assessment and management csam form. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out csam tool form
How to fill out cyber security assessment:
01
Begin by reviewing the assessment questionnaire and familiarizing yourself with the different sections.
02
Gather all relevant information and documentation related to your organization's cybersecurity practices, policies, and procedures.
03
Go through each question in the assessment and provide accurate and detailed responses based on your organization's current cybersecurity measures.
04
If you are unsure about any question or require additional information, reach out to your organization's IT or cybersecurity team for clarification.
05
Make sure to address all aspects of cybersecurity, including network security, data protection, incident response, employee training, and third-party risk management.
06
Review your answers for completeness and accuracy before submitting the completed assessment.
Who needs cyber security assessment:
01
Organizations of all sizes and industries can benefit from conducting a cyber security assessment.
02
Businesses that store and handle sensitive customer data, financial information, or intellectual property are particularly vulnerable to cyber threats and should prioritize regular assessments.
03
Regulatory compliance may also require certain organizations to undergo cyber security assessments to ensure they meet specific security standards and protect customer information adequately.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I get csam cybersecurity form?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific csam cybersecurity form and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
Can I edit csam cybersecurity form on an iOS device?
Use the pdfFiller mobile app to create, edit, and share csam cybersecurity form from your iOS device. Install it from the Apple Store in seconds. You can benefit from a free trial and choose a subscription that suits your needs.
Can I edit csam cybersecurity form on an Android device?
You can. With the pdfFiller Android app, you can edit, sign, and distribute csam cybersecurity form from anywhere with an internet connection. Take use of the app's mobile capabilities.
What is csam tool?
CSAM (Children's Sexual Assault Material) tool is a system used to detect and report the presence of child sexual exploitation material in digital environments.
Who is required to file csam tool?
Entities and individuals who host, store, or manage online content that may potentially involve child sexual exploitation materials are required to file the CSAM tool.
How to fill out csam tool?
To fill out the CSAM tool, you will need to provide detailed information regarding the potentially harmful content, including identification of the material, the context in which it was found, and any actions taken to address it.
What is the purpose of csam tool?
The purpose of the CSAM tool is to facilitate the reporting and removal of child sexual exploitation material, to protect children and hold offenders accountable.
What information must be reported on csam tool?
Information that must be reported includes the type of content identified, the location of the content, relevant timestamps, and any other identifying information that can assist law enforcement or relevant authorities.
Fill out your csam cybersecurity form online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Csam Cybersecurity Form is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.