Get the free Email Encryption End-to-End - Express Press Release Distribution
Show details
This document provides information on how to prevent unauthorized access to confidential email messages using the Email Encryption End-to-End software from Hermetic Systems. It discusses the NSA's
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign email encryption end-to-end
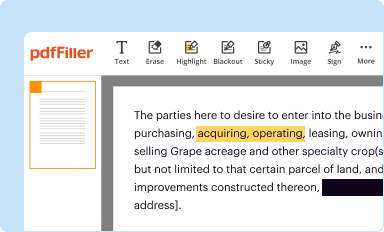
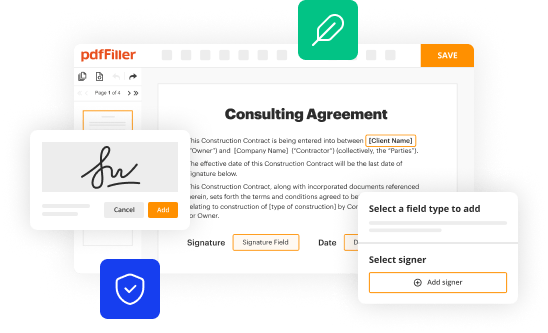
Edit your email encryption end-to-end form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
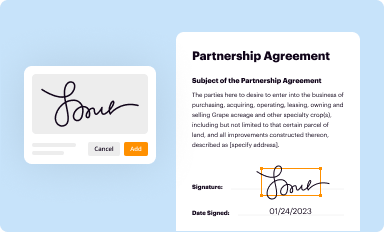
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
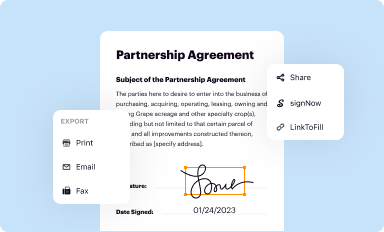
Share your form instantly
Email, fax, or share your email encryption end-to-end form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit email encryption end-to-end online
In order to make advantage of the professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit email encryption end-to-end. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out email encryption end-to-end
How to fill out email encryption end-to-end:
01
Choose a secure email provider: Look for an email service that offers end-to-end encryption as a feature. Popular options include ProtonMail and Tutanota.
02
Create an account: Sign up for the chosen email service and follow the registration process to create a new account. Make sure to select a strong and unique password.
03
Set up encryption keys: Enable encryption and generate an encryption key pair. This will involve creating a public key to share with others and a private key to keep secure on your device.
04
Share your public key: Distribute your public key to contacts you want to communicate with securely. This can be done via email, messaging apps, or through a key directory.
05
Import contacts' public keys: Obtain your contacts' public keys and import them into your email client. This will allow your client to encrypt outgoing messages to each recipient.
06
Encrypt and decrypt messages: When composing a new email, enable encryption before sending it. The email client will encrypt the message using the recipient's public key. Upon receiving an encrypted email, the recipient can decrypt it using their private key.
07
Implement additional security measures: Consider enabling two-factor authentication and regularly updating your device's software and email client to protect against potential vulnerabilities.
Who needs email encryption end-to-end?
01
Individuals concerned about privacy: Email encryption end-to-end is crucial for individuals who prioritize the confidentiality of their communications, such as journalists, activists, lawyers, or anyone dealing with sensitive information.
02
Businesses and organizations: Organizations handling sensitive data or confidential business communications should implement email encryption end-to-end to protect against unauthorized access or data breaches.
03
Anyone who values secure communication: In an era of increasing online threats, email encryption end-to-end can benefit anyone who wants to ensure their messages cannot be intercepted or tampered with.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my email encryption end-to-end in Gmail?
email encryption end-to-end and other documents can be changed, filled out, and signed right in your Gmail inbox. You can use pdfFiller's add-on to do this, as well as other things. When you go to Google Workspace, you can find pdfFiller for Gmail. You should use the time you spend dealing with your documents and eSignatures for more important things, like going to the gym or going to the dentist.
How do I make edits in email encryption end-to-end without leaving Chrome?
email encryption end-to-end can be edited, filled out, and signed with the pdfFiller Google Chrome Extension. You can open the editor right from a Google search page with just one click. Fillable documents can be done on any web-connected device without leaving Chrome.
How do I fill out the email encryption end-to-end form on my smartphone?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign email encryption end-to-end and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
What is email encryption end-to-end?
Email encryption end-to-end is a security measure that ensures the confidentiality and integrity of email messages by encrypting them at the sender's end and decrypting them only at the intended recipient's end. This prevents unauthorized access or interception of the email content during transit.
Who is required to file email encryption end-to-end?
There is no requirement to file email encryption end-to-end as it is a security measure implemented by individuals or organizations to protect the privacy of their email communication.
How to fill out email encryption end-to-end?
There is no specific form or process to fill out email encryption end-to-end as it involves implementing encryption technologies or using email client applications that support end-to-end encryption. Users can choose from various encryption methods and tools available.
What is the purpose of email encryption end-to-end?
The purpose of email encryption end-to-end is to ensure the privacy and security of email communication. It prevents unauthorized access, interception, or tampering of email content during transmission, protecting sensitive or confidential information from being accessed by third parties.
What information must be reported on email encryption end-to-end?
There is no requirement to report any information about the implementation of email encryption end-to-end as it is a security measure implemented by individuals or organizations for their own privacy and protection.
Fill out your email encryption end-to-end online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Email Encryption End-To-End is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.