Get the free VM Auth
Show details
Confidential Communication Request (HIPPO Form)
From time to time in caring for our patients, it may become necessary to contact you by telephone.
Often our parents/caretakers are not available when
We are not affiliated with any brand or entity on this form
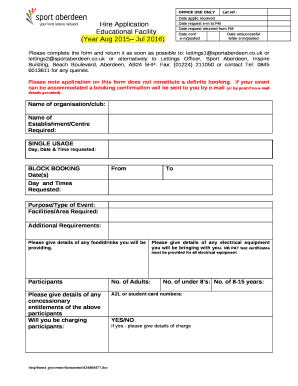
Get, Create, Make and Sign vm auth

Edit your vm auth form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your vm auth form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit vm auth online
To use the services of a skilled PDF editor, follow these steps:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit vm auth. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out vm auth

How to fill out a VM auth:
01
Gather all necessary information: Make sure you have all the required details before filling out the VM auth form. This may include your personal information, such as name, address, and contact details, as well as specific information related to the VM or virtual machine being authorized.
02
Read the instructions: Carefully go through the instructions provided with the VM auth form. This will help you understand the process and any specific requirements for filling out the form correctly.
03
Complete the personal information section: Start by filling out the personal information section of the VM auth form. Enter your name, address, phone number, and any other requested details accurately.
04
Provide VM details: In the designated section, provide all the necessary information related to the VM. This may include the VM's name, purpose, operating system, and any additional details required for identification.
05
Indicate authorization details: Specify the duration of the VM auth, whether it is a one-time authorization or for an extended period. If applicable, provide details of any restrictions or specific conditions for the VM's usage.
06
Review and double-check: Before submitting the form, take a moment to review all the information you have provided. Ensure that everything is accurate and complete. Make any necessary corrections or additions.
07
Sign and submit: If required, sign the form in the designated section to validate your authorization request. Submit the filled-out VM auth form to the relevant authority or department responsible for processing such requests.
Who needs VM auth?
01
Organizations using virtual machines: Any organization or business that utilizes virtual machines may require VM auth. This authorization ensures that authorized personnel have the necessary permissions to deploy, configure, and maintain virtual machines within the organization's infrastructure.
02
IT administrators and system administrators: IT and system administrators who manage virtual machine environments often need VM auth to gain access to specific virtual machines. This authorization helps maintain security and control over the virtual infrastructure.
03
Developers and testers: Developers and testers working with virtual machines may require VM auth to create, modify, or test software within the virtual environment.
04
Service providers: Companies or individuals offering virtual machine services may also need VM auth. This authorization allows them to provision and manage virtual machines for their clients.
05
Cloud service users: Users of cloud computing services, where virtual machines are commonly utilized, may need VM auth to control and access their virtual infrastructure effectively.
06
Compliance and security officers: Compliance and security officers responsible for ensuring that virtual machine usage adheres to regulatory requirements may require VM auth to monitor and audit virtual machine activities.
Overall, VM auth is necessary for individuals and organizations involved in utilizing, managing, or providing virtual machine services to ensure proper access control, security, and administration of virtualized environments.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is vm auth?
VM auth stands for Vendor Managed Authorization, it is a process used by vendors to manage and report information related to their authorizations.
Who is required to file vm auth?
Vendors who have authorizations for their products or services are required to file vm auth.
How to fill out vm auth?
To fill out vm auth, vendors need to provide detailed information about their authorizations, including product/service details, expiration dates, and any relevant documentation.
What is the purpose of vm auth?
The purpose of vm auth is to ensure that vendors are compliant with regulations and have the necessary authorizations for their products or services.
What information must be reported on vm auth?
Vendors must report detailed information about their authorizations, including product/service details, expiration dates, and any relevant documentation.
How do I complete vm auth online?
Filling out and eSigning vm auth is now simple. The solution allows you to change and reorganize PDF text, add fillable fields, and eSign the document. Start a free trial of pdfFiller, the best document editing solution.
How do I fill out vm auth using my mobile device?
Use the pdfFiller mobile app to fill out and sign vm auth on your phone or tablet. Visit our website to learn more about our mobile apps, how they work, and how to get started.
How can I fill out vm auth on an iOS device?
Install the pdfFiller app on your iOS device to fill out papers. If you have a subscription to the service, create an account or log in to an existing one. After completing the registration process, upload your vm auth. You may now use pdfFiller's advanced features, such as adding fillable fields and eSigning documents, and accessing them from any device, wherever you are.
Fill out your vm auth online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Vm Auth is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.