
Get the free How vulnerable is your business - ioshroutefinder co
Show details
Howvulnerableisyourbusiness? Salesandmarketing Youneedtosellyourproductsorservices, andhaveeffectivemarketingandreliabledistribution. Therisksyoufaceinclude
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign how vulnerable is your
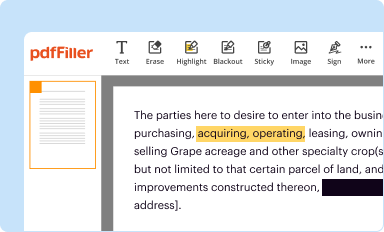
Edit your how vulnerable is your form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
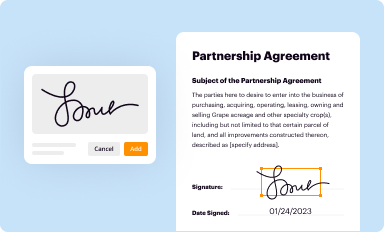
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
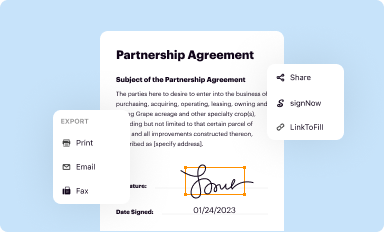
Share your form instantly
Email, fax, or share your how vulnerable is your form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit how vulnerable is your online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
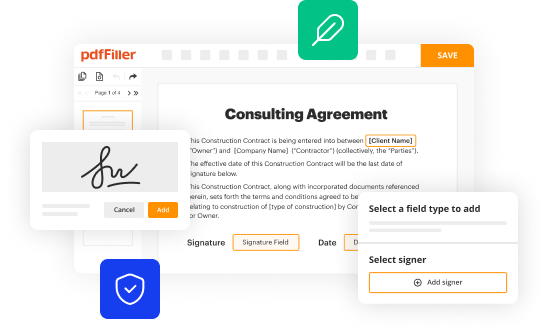
Edit how vulnerable is your. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out how vulnerable is your
To fill out "how vulnerable is your," follow these steps:
01
Start by opening the "how vulnerable is your" form or questionnaire. You can typically find this online or in the software or tool you are using.
02
Read through the instructions and questions carefully. Make sure you understand what is being asked for and what information is required.
03
Begin answering the questions one by one. Be honest and accurate in your responses. Provide relevant details and examples where necessary to support your answers.
04
Take your time to thoroughly assess your situation and vulnerabilities. Consider factors like cybersecurity, physical security, personal safety, financial security, and more.
05
If you are unsure about any questions or need additional information, feel free to seek guidance or research more on the topic. It's important to provide as accurate and complete information as possible.
06
Once you have completed all the questions, review your answers. Make sure everything is filled out correctly and there are no errors or omissions.
07
Finally, submit the filled-out form or questionnaire as per the instructions provided. If it is an online form, click the submit button. If it is a physical document, follow the designated submission process.
Who needs "how vulnerable is your"?
01
Individuals: Anyone concerned about their personal security, be it online or offline, can benefit from assessing their vulnerabilities. "How vulnerable is your" can provide insights into potential risks and suggest ways to mitigate them.
02
Businesses: Business owners, managers, and IT professionals can use "how vulnerable is your" to evaluate their organization's vulnerability to various threats. This can help identify weaknesses in security systems, protocols, and processes, allowing for appropriate measures to be taken.
03
Organizations: Non-profit organizations, government agencies, and other institutions that handle sensitive data or want to ensure the safety and well-being of their stakeholders may find "how vulnerable is your" useful. By understanding vulnerabilities, they can enhance their overall security posture and minimize potential risks.
Remember, assessing and addressing vulnerabilities is an ongoing process. It's crucial to regularly re-evaluate and take necessary actions to protect oneself, businesses, and organizations from potential threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I complete how vulnerable is your online?
Completing and signing how vulnerable is your online is easy with pdfFiller. It enables you to edit original PDF content, highlight, blackout, erase and type text anywhere on a page, legally eSign your form, and much more. Create your free account and manage professional documents on the web.
How do I edit how vulnerable is your on an Android device?
You can make any changes to PDF files, like how vulnerable is your, with the help of the pdfFiller Android app. Edit, sign, and send documents right from your phone or tablet. You can use the app to make document management easier wherever you are.
How do I fill out how vulnerable is your on an Android device?
Complete your how vulnerable is your and other papers on your Android device by using the pdfFiller mobile app. The program includes all of the necessary document management tools, such as editing content, eSigning, annotating, sharing files, and so on. You will be able to view your papers at any time as long as you have an internet connection.
What is how vulnerable is your?
How vulnerable is a measure of susceptibility to harm or damage.
Who is required to file how vulnerable is your?
Anyone who wants to assess their level of vulnerability and take appropriate actions to mitigate risks.
How to fill out how vulnerable is your?
You can fill out how vulnerable is by analyzing various factors such as physical security, cybersecurity, and environmental hazards.
What is the purpose of how vulnerable is your?
The purpose of how vulnerable is to identify potential weaknesses and vulnerabilities in order to strengthen defenses and reduce risks.
What information must be reported on how vulnerable is your?
Information such as current security measures, past incidents, and potential threats must be reported on how vulnerable is.
Fill out your how vulnerable is your online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

How Vulnerable Is Your is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















